888 Rat v1.2.4 Cracked
The proliferation of cracked remote access tools has significantly lowered the barrier to entry for cybercriminals, enabling even novice attackers to launch sophisticated intrusions. These illicitly modified versions of commercial surveillance software bypass licensing restrictions and often include additional malicious payloads, making them particularly dangerous in the hands of threat actors. The availability of such tools on underground forums has contributed to a surge in targeted attacks against individuals, small businesses, and corporate networks, with attackers leveraging them for everything from credential theft to ransomware deployment. The latest 888 Rat v1.2.4 versions demonstrate improved evasion capabilities, including the ability to bypass endpoint detection systems and maintain persistence through system updates.
Download Link 1
Download Link 2
Download Link 3
Download Link 4
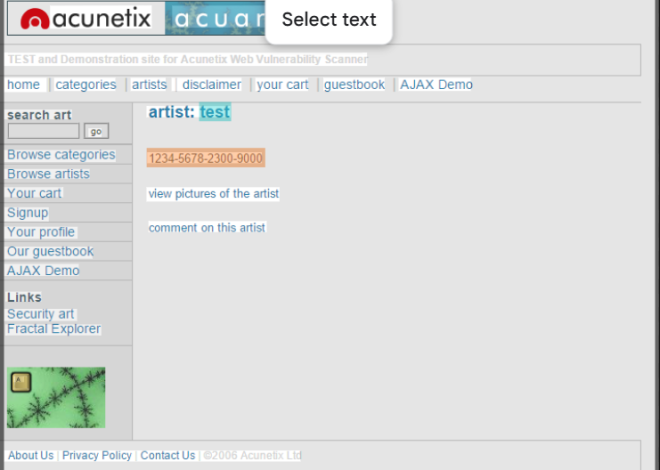
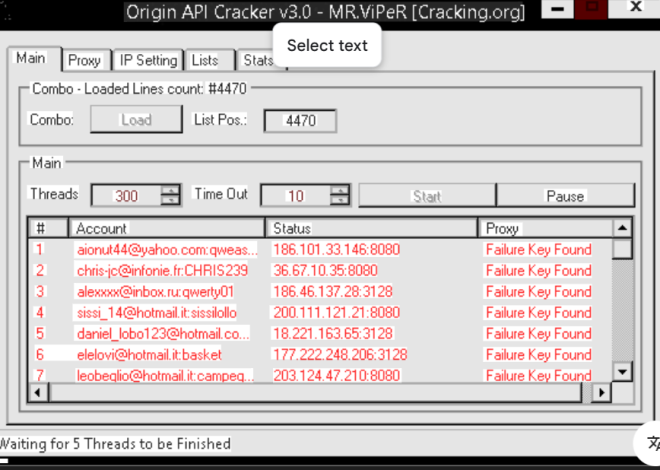
This type of software is a pirated version of a legitimate remote administration program that has been modified to remove license verification and often bundled with additional malware components. While the original software may have been designed for system administration or parental control, the cracked variant is almost exclusively used for malicious purposes. Cybercriminals deploy these tools to gain complete control over victim devices, enabling them to steal sensitive data, monitor user activity, and deploy secondary payloads. The cracked nature of these tools makes them particularly dangerous, as they often include undocumented backdoors that can be accessed by multiple parties beyond the initial purchaser.

Key Features
| Feature | Description |
| Hidden Remote Desktop | Provides stealthy GUI access without visible indicators |
| Keylogging Functionality | Captures all keyboard input including secure fields |
| Webcam Activation | Enables covert surveillance through device cameras |
| File Transfer Capability | Allows uploading/downloading files to/from infected systems |
| Process Manipulation | Can terminate security processes or inject code into running applications |
| Persistence Mechanisms | Survives reboots and maintains access through multiple methods |
| Network Propagation | Spreads to other systems on local networks |
| Anti-Detection Techniques | Uses process hollowing and rootkit-like hiding methods |
How 888 Rat v1.2.4 Works
The cracked remote access tool operates through a multi-stage infection and control process:
- Distribution Methods
- Embedded in pirated software cracks and keygens
- Distributed as fake game mods or productivity tools
- Delivered through phishing emails with malicious attachments
- Installation Process
- Uses social engineering to bypass User Account Control (UAC)
- Exploits known vulnerabilities in popular software for silent installation
- Drops multiple payloads in different locations for redundancy