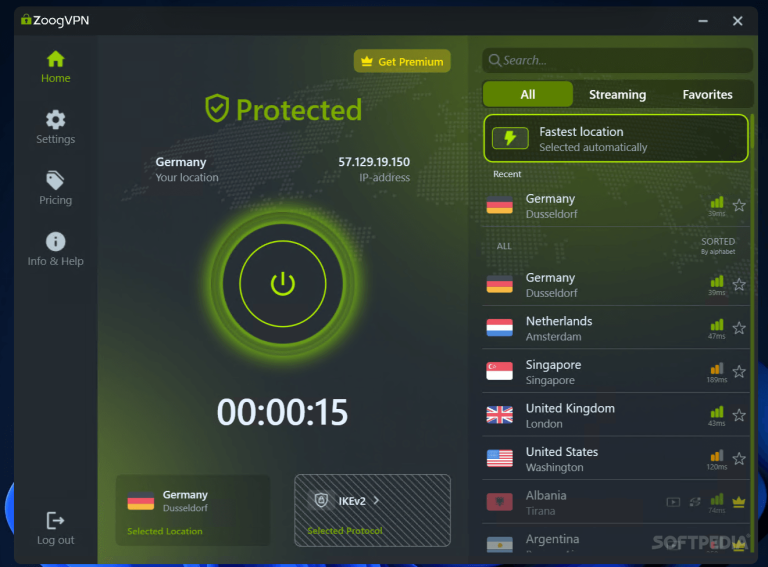
ZoogVPN Cracked Version Download Now
ZoogVPN Cracked Version is a cost-effective VPN service that offers solid core features with attractive pricing and lifetime plans. It focuses on ease of use and everyday privacy rather than advanced enterprise tools. This review provides a balanced analysis of its capabilities and practical …