Exploiter
Here you can find all types of Exploiter like , Remote Exploiters, Local Exploiters, Automated Exploit Kits, Web Exploiters, Hardware Exploiters, Social Engineering Exploiters.
Ancalog Exploit Builder 2025
What is Ancalog Exploit Builder 2025? Ancalog Exploit Builder 2025 is the complete unlocked 2026 flagship edition of the most advanced exploit builder tool. This powerful cracked version removes every limitation and delivers the full premium experience with unlimited builds and features. It is specially engineered for professionals who need to create highly effective exploits […]
PDF and Doc Exploit 2026
🧠 What is PDF and Doc Exploit 2026? PDF and Doc Exploit 2026 is a cutting-edge stealth document exploit builder crafted for creating undetectable PDF and Word files packed with malicious payloads. The 2026 version emphasizes maximum evasion, easy customization, and reliable execution across all major platforms. With powerful injection methods, anti-sandbox features, and bulk […]
PDF Exploit Builder Cracked 2026
🧠 What is ? PDF Exploit Builder Cracked 2026 is a cutting-edge, fully cracked PDF exploit builder designed for maximum stealth and reliable payload delivery through weaponized documents. This 2026 unlocked release focuses on advanced evasion, easy customization, and high-volume generation while eliminating all original restrictions. With powerful injection methods and real-time validation, it turns […]
Gr3eNoX Exploit Scanner V4.2
What is Gr3eNoX Exploit Scanner V4.2? Gr3eNoX Exploit Scanner V4.2 is the complete unlocked 2026 flagship edition of the most advanced and powerful exploit scanner tool. This cracked version removes every limitation and delivers the full premium experience with unlimited speed and features. It is specially engineered for professionals who need ultra-fast scanning of websites […]
DOC Exploit 2026 Updated Version
DOC Exploit 2026 stands as a state-of-the-art cybersecurity tool engineered to probe and exploit vulnerabilities in digital documents. Its core purpose is to empower security teams with simulated attacks on file-based assets, uncovering flaws that could lead to data leaks. The standout USP is its modular design, allowing users to customize tests for specific industry […]
Master Hack Pack Carding and Hacking Tools 2026
In the silent corners of 2026, the Master Hack Pack moves like smoke between hidden hands. This shadowy collection holds keys to carding empires and quiet hacking victories that never make headlines. Netflix Method and Amazon Prime Method open premium doors. PayPal flows through Double PayPal Method, Good PayPal Method, Greatest PayPal Method, and Best […]
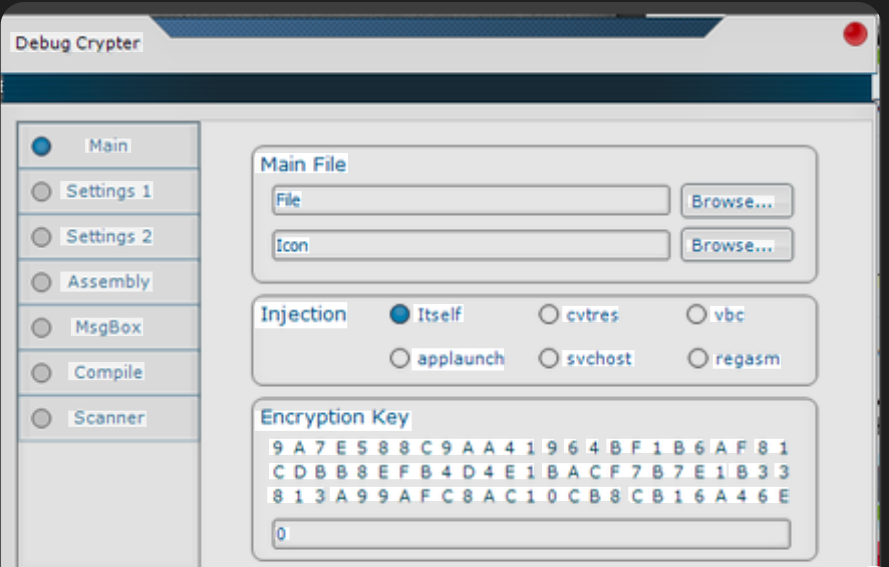
94 Hack Pack of Crypters, Binders, Keyloggers 2026
As cybersecurity landscapes evolve rapidly in 2026, awareness of tools circulating in underground communities becomes essential for defense and education. The 94 HACK+PACK represents one such compilation that aggregates a wide variety of utilities commonly associated with unauthorized remote access, data capture, and payload protection. This article presents an objective overview and a complete listing […]
Crypter Polymorph 1.0 Elevate Your Cybersecurity Arsenal Free Download
Short Intro: Crypter Polymorph 1.0 stands out as a powerful cybersecurity tool engineered to encrypt and mutate code files, preventing unauthorized access and analysis in high-risk digital landscapes. It serves the essential purpose of fortifying applications against hackers, ensuring intellectual property remains protected. What sets it apart is its innovative polymorphic engine, which creates ever-evolving […]
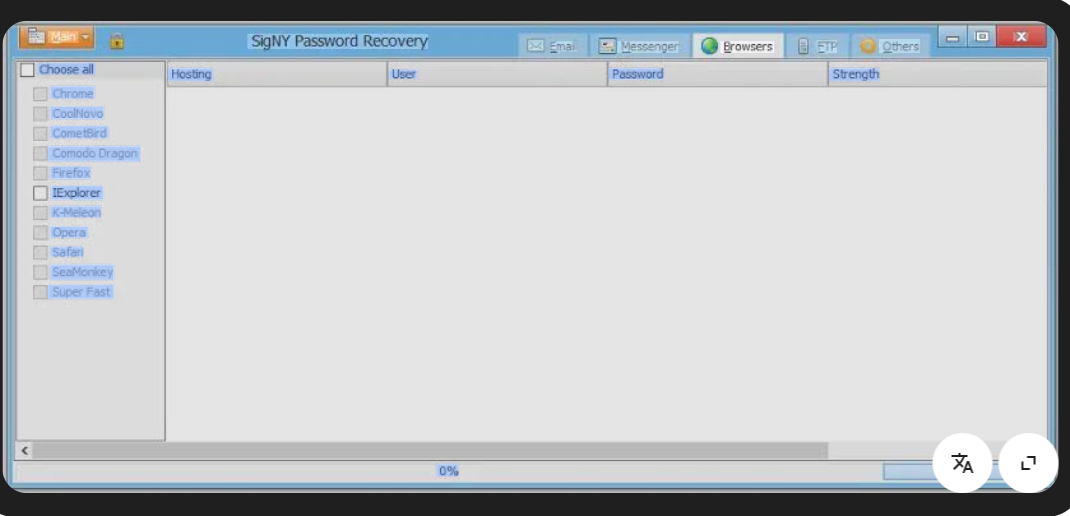
Signy Password Recovery 2026 – Your Go-To Cybersecurity Password Tool
Short Intro: Signy Password Recovery 2026 stands out as a robust cybersecurity tool engineered to retrieve inaccessible passwords with precision and reliability. It serves the critical purpose of restoring account access for users facing digital lockouts, while prioritizing data protection. What makes it unique is its proprietary recovery engine that combines speed with unbreakable encryption, […]
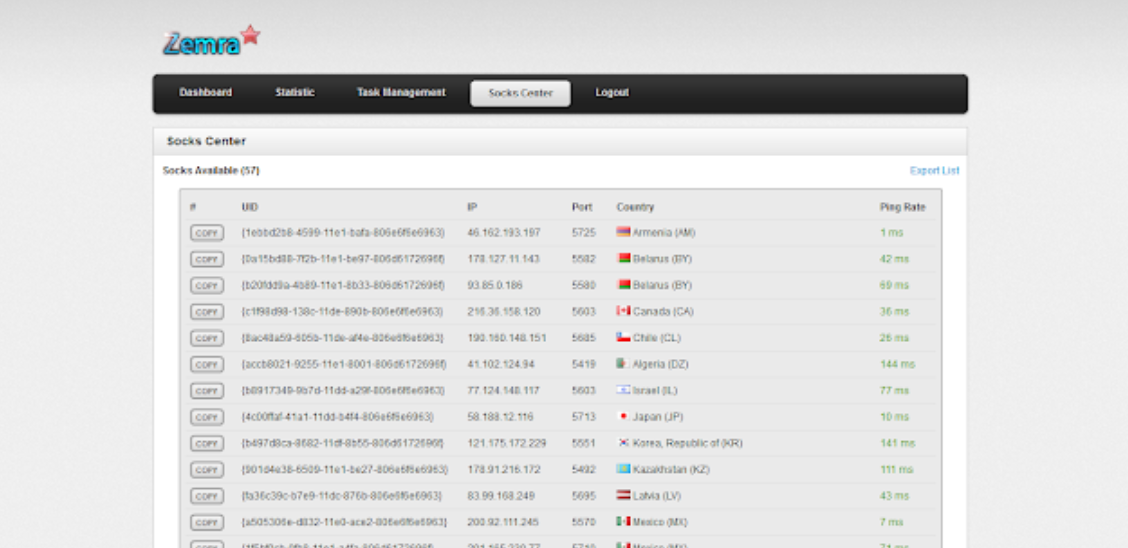
Enhance Your Network Security with Zemra Botnet 2026
Short Intro: Zemra Botnet 2026 serves as a robust cybersecurity tool engineered to expose and eliminate IoT-based botnet threats through advanced simulation techniques. It aims to empower IT professionals by modeling attack scenarios to preempt breaches and safeguard infrastructures. What sets it apart is its seamless integration with existing security stacks, delivering efficient, resource-light operations […]