Hacking Tutorial
This platform is very informative for you because here you can find all hacking tutorial which helps you to become expert
Hacking Android 2026 Updated Version Tools
Hacking Android 2026 is a robust cybersecurity solution tailored for experts who need to test and fortify Android devices against evolving cyber risks. Its core purpose is to facilitate ethical hacking practices, revealing weaknesses in apps and hardware through precise simulations. The primary USP is its modular design, allowing seamless upgrades and integrations for ongoing […]
Master Hack Pack Carding and Hacking Tools 2026
In the silent corners of 2026, the Master Hack Pack moves like smoke between hidden hands. This shadowy collection holds keys to carding empires and quiet hacking victories that never make headlines. Netflix Method and Amazon Prime Method open premium doors. PayPal flows through Double PayPal Method, Good PayPal Method, Greatest PayPal Method, and Best […]
94 Hack Pack of Crypters, Binders, Keyloggers 2026
As cybersecurity landscapes evolve rapidly in 2026, awareness of tools circulating in underground communities becomes essential for defense and education. The 94 HACK+PACK represents one such compilation that aggregates a wide variety of utilities commonly associated with unauthorized remote access, data capture, and payload protection. This article presents an objective overview and a complete listing […]
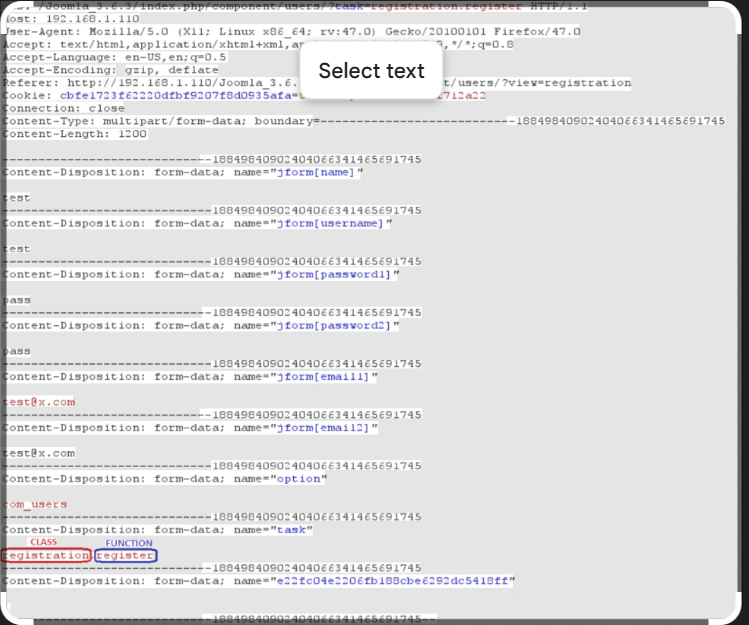
Joomla User Exploit Helper v1.1: Essential Tool for Cybersecurity Vulnerabilities in 2026
Short Intro: Introducing Joomla User Exploit Helper v1.1, a powerful cybersecurity utility focused on detecting and mitigating exploits within Joomla content management systems. This tool empowers professionals to conduct thorough audits of Joomla-based websites, protecting against data breaches. Its standout feature is the intuitive dashboard that simplifies exploit analysis, setting it apart for rapid, effective […]
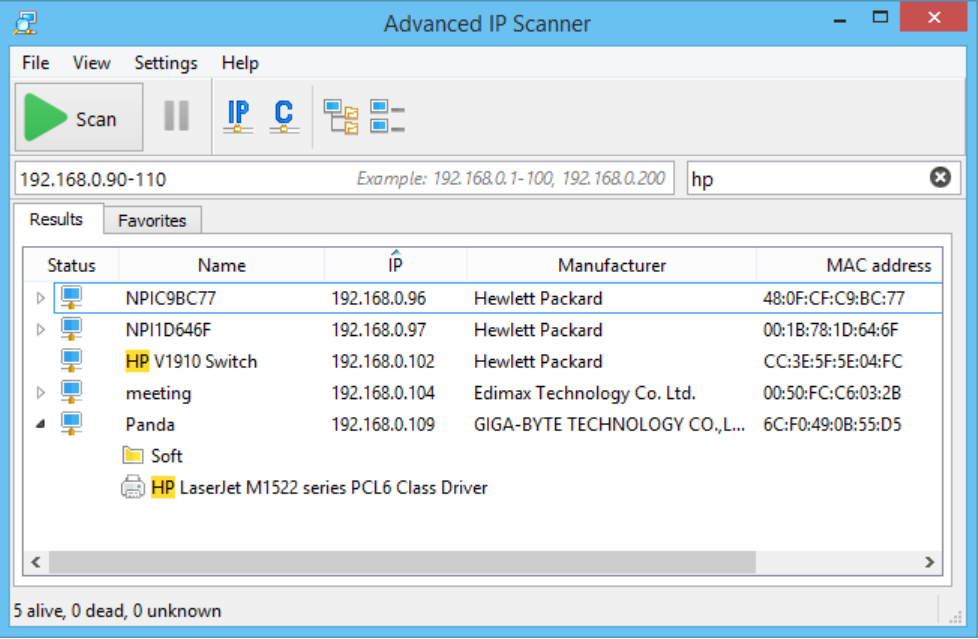
Xdedic IP Scanner 2026
Short Intro: The Xdedic IP Scanner 2026 is a cutting-edge cybersecurity tool designed to scan and analyze IP addresses for vulnerabilities, ensuring robust network security. Its primary purpose is to help professionals identify threats proactively, making it an essential asset for IT teams and cybersecurity experts. What sets it apart is its lightning-fast scanning speed […]
Lime Crypter 2026 – Revolutionizing Malware Encryption
Short Intro: Lime Crypter 2026 stands out as a premier cybersecurity solution focused on transforming raw data into fortified, undecryptable formats. It serves to block unauthorized decryption attempts and enhance overall system resilience against digital intrusions. What sets it apart is its AI-driven adaptive encryption, which learns from threats to provide dynamic, intelligent protection. Feature […]
Learning Tor and the Dark Web 2024
The Dark Web and the Tor network continue to play vital roles in cybersecurity, digital privacy, and ethical hacking. Often misunderstood, the Dark Web isn’t solely a hub for illegal activity—it also serves as a critical tool for whistleblowers, journalists, and privacy-focused users. Learning how Tor works and how to explore the Dark Web responsibly […]
Certified Ethical Hacker v10 PDFs Books
The Certified Ethical Hacker (CEH) v10 certification remains one of the most respected credentials in the field of cybersecurity. Although CEH v12 is now the latest version, CEH v10 books and PDFs continue to be highly useful for learning penetration testing, ethical hacking, and defensive strategies. This guide explores why CEH v10 study materials are […]
Hacking Android 2024
With over 3 billion active devices, Android remains the most widely used mobile operating system—and consequently, a top target for cyberattacks. Ethical Android hacking plays a vital role in defending against these threats by identifying vulnerabilities, securing applications, and testing system defenses. Whether you’re a penetration tester, security researcher, or cybersecurity student, mastering Android hacking […]
CEH V11 EC-COUNCIL CERTIFIED ETHICAL HACKER
The CEH v11 (Certified Ethical Hacker) certification by EC-Council is a globally recognized program designed to train cybersecurity professionals in identifying and mitigating vulnerabilities in modern systems. As cyberattacks become increasingly sophisticated, ethical hacking tools and methodologies—often covered in resources like the EC-Council Certified Ethical Hacker (CEH V11)— play a crucial role in both offensive […]