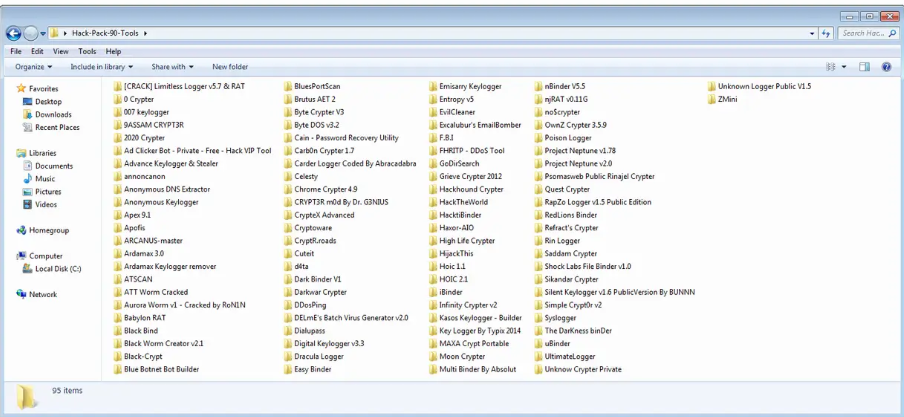
94 Hack Pack of Crypters, Binders, Keyloggers 2026
As cybersecurity landscapes evolve rapidly in 2026, awareness of tools circulating in underground communities becomes essential for defense and education. The 94 HACK+PACK represents one such compilation that aggregates a wide variety of utilities commonly associated with unauthorized remote access, data capture, and payload protection. This article presents an objective overview and a complete listing of the tools included in the pack, aimed at helping security professionals, researchers, and students recognize and understand the names frequently mentioned in threat reports.
The pack primarily focuses on four main categories: crypters for obfuscating executables, binders for combining files, keyloggers for recording user activity, and various remote access or auxiliary utilities. Compilations like this often appear in private forums and are studied in malware analysis labs to improve detection capabilities and develop better protective measures.
Download Link 1
Download Link 2
Download Link 3
Security teams benefit from familiarity with these tool names because many appear in incident response logs, reverse engineering tasks, and threat intelligence feeds. Knowing the exact nomenclature helps analysts correlate samples, identify campaign patterns, and build more accurate signatures.
Below is the exhaustive list of all 94 tools as they appear in the 2026 collection:
- MAXA Crypt Portable
- Moon Crypter
- Multi Binder By Absolut
- nBinder VolS
- nRAT v0.11G
- noScrypter
- OwnZ Crypter 3.5.9
- Poison Logger
- Project Neptune v1.78
- Project Neptune v2.0
- Psomasweb Public Rinajel Crypter
- Quest Crypter
- RapZo Logger v1.5 Public Edition
- RedLions Binder
- Refract_s Crypter
- Rin Logger
- Saddam Crypter
- Shock Labs File Binder v1.0
- Sikandar Crypter
- Silent Keylogger v1.6 PublicVersion By BUNNN
- Simple Crypt0r v2
- Syslogger
- The DarKness binDer uBinder
- UltimateLoggen
- Unknow Crypter Private
- Unknown Logger Public V1.5
- ZMini Caccess
- CRYPT3R mOd By Dr. G3NIUS
- CrypteX Advanced
- Cryptoware
- CryptR.roads
- Cuteit d4ta
- Dark Binder V1
- Darkwar Crypter
- DDosPing
- DELmE_s Batch Virus Generator v2.0
- Dialupass
- Digital Keylogger v3.3
- Dracula Logger
- Easy Binder
- Emisarry Keylogger
- Entropy v5
- EvilCleaner
- Excalubur_s EmailBomber
- F.B.I
- FHRITP – DDoS Tool
- GoDirSearch
- Grieve Crypter 2012
- Hackhound Crypter
- HackTheworld
- Hackti Binder maxor-A O
- High Life Crypter
- Hilackunis Luick access
- Ad Clicker Bot – Private – Free – Hack VIP Tool
- Advance Keylogger & Stealer
- annoncanon
- Anonymous DNS Extractor
- Anonymous Keylogger
- Apex 9.1
- Apofis
- ARCANUS-master
- Ardamax 3.0
- Ardamax Keylogger remover
- ATSCAN
- ATT Worm Cracked
- Aurora Worm v1 – Cracked by RoNIN
- Babylon RAT
- Black Bind
- Black Worm Creator v2.1
- Black-Crypt
- Blue Botnet Bot Builder
- BluesPortScan
- Brutus AET Z
- Byte Crypter V3
- Byte DOS Ye.2
- Cain – Password Recovery Utility
- Carbon Crypter 1.4
- Carder Logger Coded By Abracadabra
- Celesty
- Chrome Crypter 4.9
This catalog serves as a reference point for understanding the breadth of utilities available in underground packs during 2026. Crypters form a significant portion, reflecting the ongoing arms race between malware authors and antivirus vendors. Binders enable social engineering tactics by disguising payloads. Keyloggers and stealers focus on credential harvesting, while RATs and worms provide persistent access and propagation capabilities.
From a defensive perspective, organizations should prioritize endpoint protection, network monitoring, user education, and regular patching to mitigate risks associated with tools of this nature. Security researchers often analyze samples from such packs in isolated environments to extract indicators of compromise (IOCs) and develop updated detection rules.
Educational programs in ethical hacking and malware analysis frequently reference similar compilations (without encouraging misuse) to illustrate real-world techniques employed by threat actors. The goal remains building stronger defenses through knowledge rather than exploitation.
In summary, the 94 HACK+PACK 2026 offers a broad snapshot of tools discussed in underground circles. The complete name list above provides clarity for anyone involved in cybersecurity awareness, threat hunting, or incident response activities. Responsible handling of this information focuses exclusively on improving protection and understanding adversary tactics.