Bruter
Here are all types of bruter like Password Bruters, Hash Bruters, Wi-Fi Bruters, API/Token Bruters, ZIP/RAR Bruters, Credential Stuffing Tools.
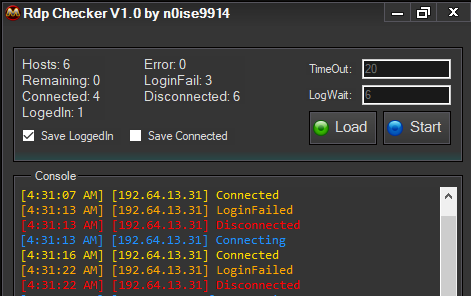
RDP Multi Tool Cracked 2025
The rise of remote work has made Remote Desktop Protocol (RDP) a prime target for cybercriminals, leading to the development of increasingly sophisticated attack tools. In 2025, cracked versions of professional RDP exploitation tools have become particularly prevalent in cyberattacks, enabling threat actors to automate large-scale brute-force attacks, vulnerability scanning, and post-compromise activities. RDP Multi […]
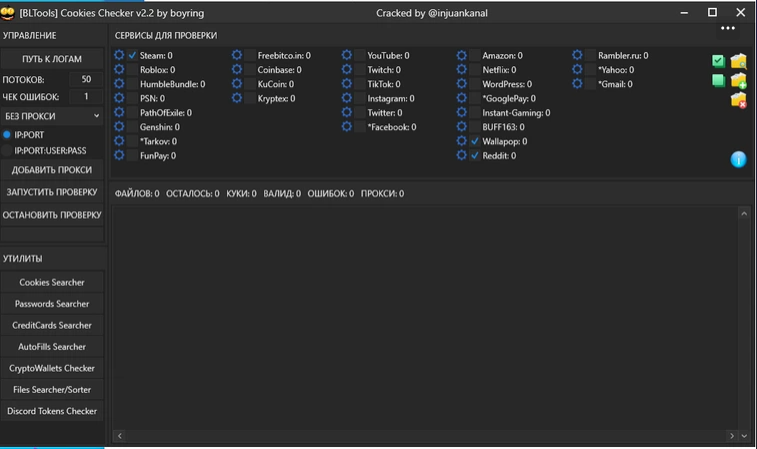
BLTools v2.0
In 2024, SMTP exploitation tools have become increasingly sophisticated, with web-based interfaces making them more accessible to attackers of varying skill levels. These browser-controlled platforms have lowered the barrier to entry for email-based attacks while increasing the scale and efficiency of SMTP server exploitation. By combining automated testing capabilities with intuitive dashboards, these tools enable […]
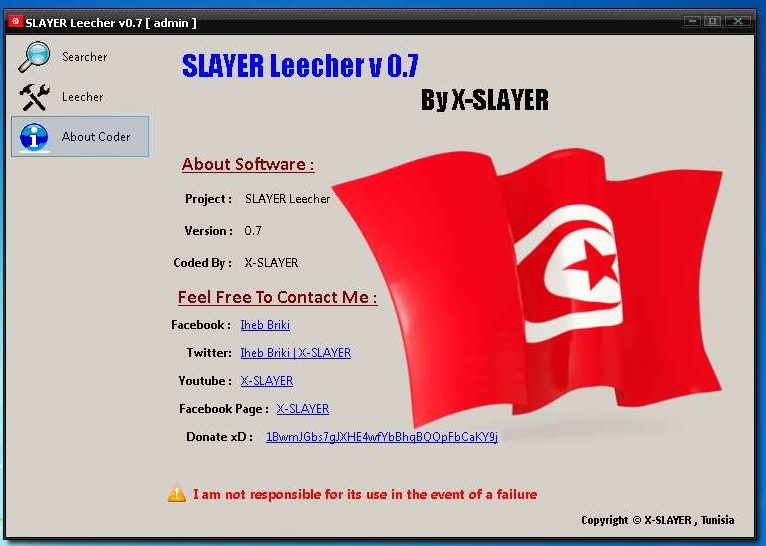
SLAYER Leecher V0.7 Final Edition with tutorial
In the ever-evolving landscape of cybercrime, credential harvesting tools have become increasingly sophisticated, enabling attackers to automate large-scale account compromise with minimal effort. The latest iteration of these specialized tools represents a significant advancement in credential theft capabilities, combining user-friendly interfaces with powerful automation features. These tools have become particularly prevalent in attacks against online […]
Cpanel Checker Account 2025
As web hosting control panels remain critical infrastructure for millions of websites, specialized tools have emerged to target these administrative interfaces. In 2025, credential testing tools focusing specifically on hosting control panels have become increasingly sophisticated, posing significant risks to web infrastructure security. These tools enable attackers to systematically probe for vulnerable accounts, often serving […]