Cracked Software
Here you can find all cracked software for hacking like emails, SMS, Whatsapp related as well as all cracking tools for you
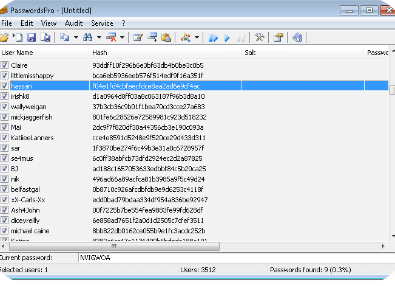
PASSWORDS PRO v3.1 with All Plugins
PASSWORDS PRO v3.1 Cracked with All Plugins is a powerful and flexible password recovery tool designed to help users regain access to forgotten or lost credentials. Supporting a wide range of file types and encryption methods, this portable, pre-activated version is especially useful for cybersecurity professionals, ethical hackers, and IT specialists who need a comprehensive […]
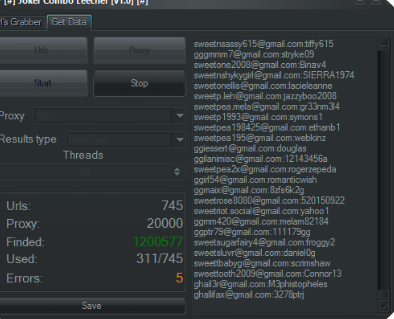
Joker Combo Leecher v1.0
Joker Combo Leecher v1.0 is a powerful yet controversial tool designed to extract and leech combo lists (username and password combinations) from various sources. This portable, pre-cracked version offers users immediate access without the need for installation or activation—making it a widely discussed tool in certain online communities. However, its use raises serious ethical and […]
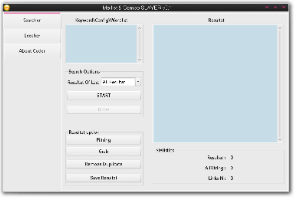
Mailist Combo Leecher
In the fast-paced world of digital marketing, having access to high-quality, targeted email lists can significantly impact your campaign’s success. Mailist Combo Leecher is a powerful tool designed to help marketers extract relevant email addresses quickly and efficiently. Whether you’re a seasoned professional or just starting out, this tool can streamline your lead generation efforts […]
Beaver SMS Bomber 2025
In the evolving landscape of cyber threats, tools designed to disrupt communication systems have become a growing concern. Among these, SMS bombing software has gained notoriety for its ability to overwhelm targets with a flood of text messages, causing service disruptions, psychological distress, and even financial losses. Beaver SMS Bomber 2025 is often exploited in harassment […]
Best SEO Tools 2025
The best SEO Tools of 2025 have become indispensable for digital marketers; however, cybercriminals are increasingly exploiting their capabilities to conduct sophisticated attacks. Malicious actors abuse these tools to manipulate search rankings, distribute malware, and launch phishing campaigns. By leveraging automated keyword research, backlink analysis, and content optimization features, attackers can craft highly targeted lures […]
NinjaTok tiktok Bot 2024
In recent years, tools like NinjaTok TikTok Bot 2024 have become a growing threat in the cybersecurity landscape. These automated bots are designed to manipulate social media platforms by generating fake engagement, spreading malware, or conducting large-scale spam campaigns. Attackers use them to artificially inflate follower counts, like/dislike ratios, and comment sections, often for financial […]
Pandora hVNC Cracked 2024
The rise of advanced remote access tools in cyberattacks has significantly increased the sophistication of modern threats. Among these tools, “Pandora hVNC Cracked 2024” has gained notoriety for enabling stealthy, persistent access to compromised systems. Often distributed through phishing campaigns or exploit kits, this tool allows attackers to bypass security measures and maintain undetected control […]
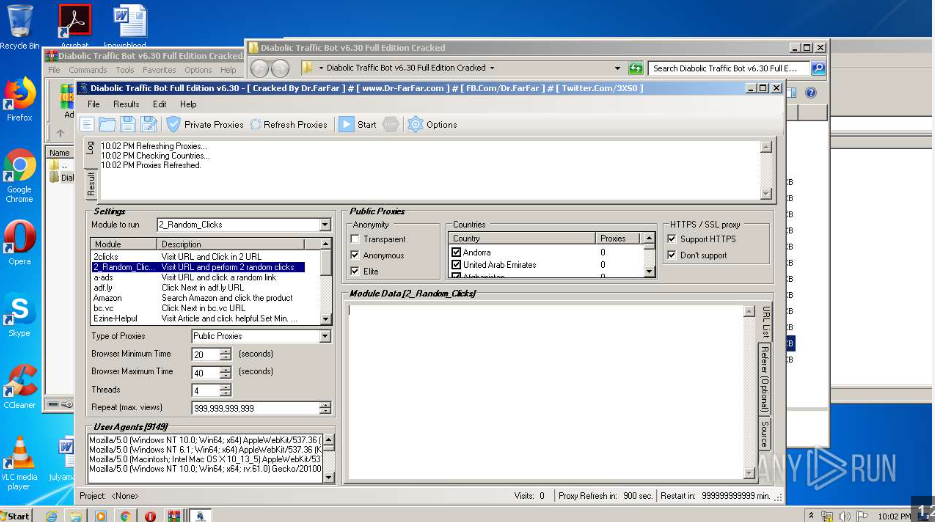
Diabolic Traffic Bot Full Edition v8.0 Activated
Automated tools that manipulate web traffic pose a growing challenge for cybersecurity professionals. Among these, traffic generation bots are particularly concerning. Diabolic traffic bot simulate human-like interactions to overwhelm websites, distort analytics, or commit fraud. Often, attackers use them in distributed denial-of-service (DDoS) attacks, ad fraud, or competitive sabotage. Because they mimic legitimate users at scale, […]
Eziriz Net Reactor 5.9.2.0
Eziriz Net Reactor is a powerful obfuscation and protection tool designed to secure .NET applications from reverse engineering and unauthorized modifications. While it serves as a valuable resource for developers, its robust capabilities have also made it a favored choice among threat actors aiming to conceal malicious code, evade detection, and deploy payloads in cyberattacks. […]
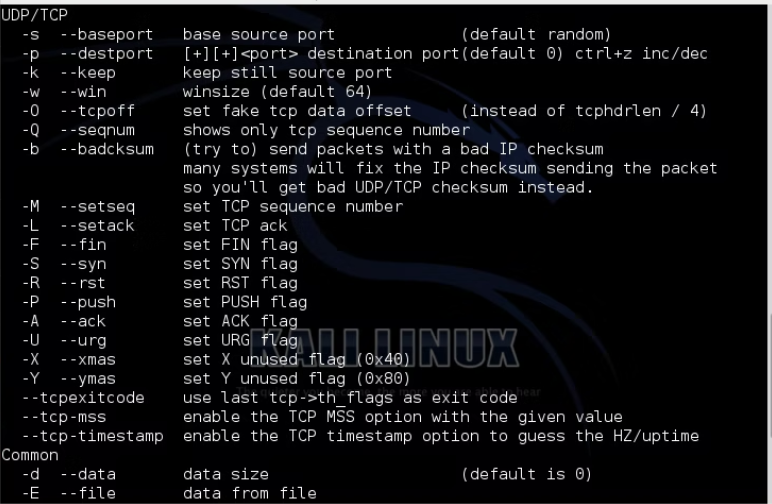
HULK DDOS 2024
Distributed Denial-of-Service (DDoS) attacks remain a persistent threat in cybersecurity, and tools like HULK DDoS 2024 have emerged as potent weapons for disrupting online services. Unlike traditional DDoS methods, modern iterations employ advanced evasion techniques and increased scalability, making them more challenging to mitigate. These attacks overwhelm target servers with massive volumes of malicious traffic, often […]