Crypter
Here are various crypter for you like PE (Portable Executable) Crypters, FUD, Code Packers, Metamorphic Crypters, Web Crypters, and .NET Crypters.
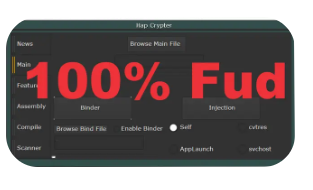
Hap Crypter Cracked 2024
Hap Crypter is a well-known software crypter designed to obfuscate malicious executables, making them undetectable by antivirus programs. The “cracked” 2024 version refers to an illicitly modified release, often distributed in underground forums. While it has legitimate uses in penetration testing, its misuse poses significant cybersecurity threats. This article explores its functionality, risks, and defensive measures. Download Link 1 Download […]
Crypters and Binders Pack 2024
Crypters and Binders Pack 2024 is a powerful toolkit designed for developers, security researchers, and ethical hackers to securely encrypt, bind, and deliver executable files while maintaining confidentiality and functionality. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What Is Crypters and Binders Pack 2024? Crypters and Binders Pack is a […]
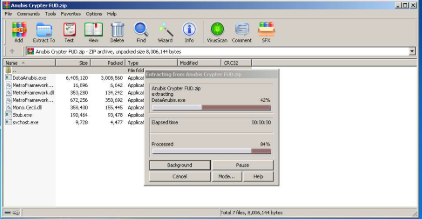
Anubis Crypter FUD 2025
In the arms race between cybercriminals and security professionals, Anubis Crypter FUD 2025 have emerged as a critical weapon for evading detection. The latest iterations of these tools employ increasingly sophisticated methods to bypass even advanced security solutions, enabling malware to operate undetected for extended periods. These evasion capabilities make crypters particularly dangerous in ransomware […]
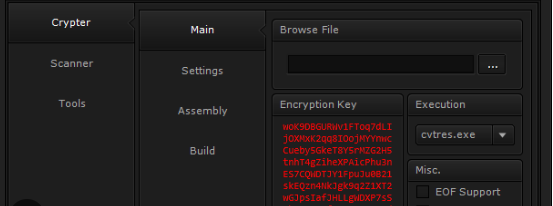
0 Crypter
Cybercriminals continue to leverage advanced 0 Crypter to bypass security measures, with newer variants becoming more sophisticated in their evasion techniques. These tools play a critical role in modern cyberattacks by enabling malware to remain undetected long enough to compromise systems, exfiltrate data, or establish persistent access. As endpoint detection solutions improve, crypters evolve in […]
WH ApkCrypter V2
In the evolving landscape of cybersecurity, malicious actors increasingly rely on advanced tools to bypass detection and deploy harmful payloads. One such tool, known for its ability to evade traditional security measures, is the WH ApkCrypter V2. This type of software plays a significant role in modern cyberattacks, particularly in obfuscating malware to avoid analysis […]
Acordx Crypter 2024 Cracked
In today’s cybersecurity landscape, Acordx Crypter 2024 are playing an increasingly significant role in enabling sophisticated cyberattacks. These tools are specifically designed to bypass modern security measures by disguising malicious code, making them a favourite among ransomware operators, data thieves, and other cybercriminals. Cracked or pirated versions of crypters circulating in underground forums further lower […]
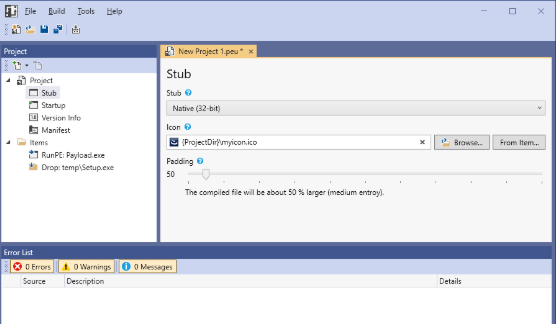
PEUNION Crypter 2024
In the ever-evolving world of cyber threats, PEUNION Crypter 2024 have become a crucial tool for attackers looking to bypass security measures and deliver malicious payloads undetected. These programs specialise in obfuscating and encrypting malware, making it difficult for traditional antivirus solutions to detect and identify them. Modern cyberattacks, including ransomware, banking trojans, and spyware, […]
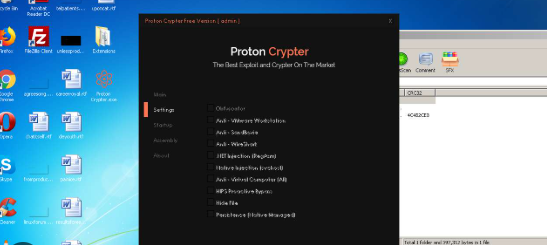
Proton Crypter V 2.0
In the evolving landscape of cybersecurity threats, Proton Crypter V 2.0 has emerged as a critical tool for attackers who aim to evade detection and deploy malicious payloads. These programs are specifically designed to obfuscate and encrypt harmful code, thereby making it extremely difficult for traditional antivirus solutions to identify and block them. Consequently, modern […]
Visual Protector 0.5
In modern cyberattacks, tools like Visual Protector 0.5 play a significant role in bypassing security measures and delivering malicious payloads. These tools are often used by threat actors to evade detection, making them a persistent challenge for cybersecurity professionals. By leveraging obfuscation, encryption, and other evasion techniques, such tools enable malware to infiltrate systems undetected, […]
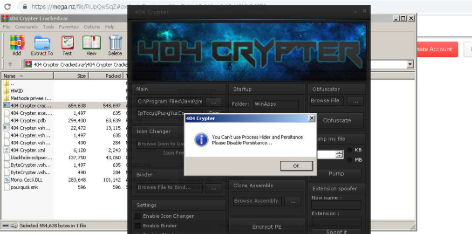
404 Crypter Cracked
In the evolving landscape of cyber threats, 404 Crypter Cracked have become indispensable tools for malicious actors seeking to evade detection. Cracked versions of these programs circulate in underground forums, democratizing access to advanced obfuscation techniques. These tools empower attackers to bypass traditional security measures, facilitating the distribution of ransomware, data stealers, and other malware. […]