Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Crypto Wallet Replacer 2024
Crypto Wallet Replacer 2024 is a sophisticated malware strain designed to covertly hijack cryptocurrency transactions by manipulating wallet addresses in a victim’s clipboard. This stealthy threat targets Windows, macOS, and Linux systems, focusing on users of popular wallets like MetaMask, Exodus, and Ledger Live. By silently altering copied wallet addresses during transactions, it redirects funds to attacker-controlled […]
LoveNikki Stealer Cracked 2024
LoveNikki Stealer Cracked 2024 is a leaked version of a premium information-stealing malware, now circulating freely in underground hacking communities. This cracked variant retains the original’s powerful data extraction capabilities while adding custom obfuscation and evasion tweaks to bypass security software. Specializing in credential harvesting from browsers, cryptocurrency wallets, and gaming platforms, it poses a significant threat to both individual users […]
Ozone RAT 2024
Ozone RAT 2024 emerges as a sophisticated Remote Access Trojan (RAT) designed for stealthy, long-term system infiltration. This advanced malware combines fileless execution, AI-driven evasion, and blockchain-backed C2 infrastructure to bypass modern security measures. Targeting both individuals and enterprises, Ozone RAT enables complete system control while maintaining operational secrecy, making it particularly dangerous for financial fraud, corporate espionage, and large-scale credential […]
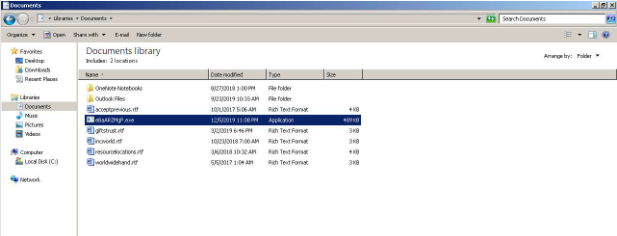
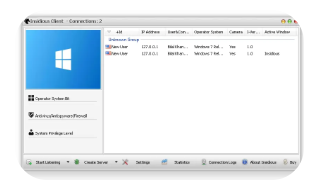
Insidious rat Cracked 2024
Insidious RAT Cracked 2024 is a pirated version of a premium Remote Access Trojan (RAT) circulating in hacker forums, offering unauthorized users full system control without licensing restrictions. This cracked variant retains the original malware’s powerful surveillance capabilities while adding custom obfuscation and evasion tweaks to bypass modern security solutions. Designed for stealthy, long-term access, it poses a severe risk to […]
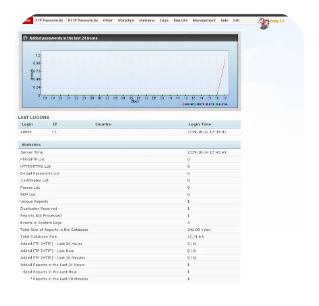
Gorynych Diamond Fox HTTP Botnet 4.2.0 v650 with Tutorial
Gorynych Diamond Fox HTTP Botnet 4.2.0 v650 represents a state-of-the-art malware framework designed for large-scale credential harvesting, financial fraud, and distributed attacks. This latest version introduces AI-driven target selection, blockchain-anonymized C2 infrastructure, and self-learning evasion techniques, making it one of the most sophisticated threats in 2024. Bundled with an extensive tutorial, the package enables even novice hackers to deploy advanced […]
Pony 2.2 HTTP Botnet English
Pony 2.2 HTTP Botnet (English Version) marks the return of one of history’s most notorious credential-stealing botnets, now upgraded with modern evasion tactics and expanded functionality. This reborn threat combines the original Pony Loader’s efficient data harvesting capabilities with HTTPS-based C2 communication, sandbox detection, and automated wallet theft, making it particularly dangerous for both individual users and enterprise […]
SAS – Saefko Attack Systems Rat android 2024
This sophisticated malware grants hackers full control over compromised smartphones, enabling data theft, surveillance, and remote command execution. With its enhanced evasion techniques and modular architecture, SAS RAT 2024 poses a severe threat to personal privacy, corporate security, and mobile banking integrity. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What is SAS RAT Android […]
WSH Rat Cracked 2024
WSH RAT Cracked 2024 is a pirated version of a premium Windows Script Host-based Remote Access Trojan, recently leaked in underground hacking communities. This cracked variant provides threat actors with sophisticated surveillance and system control capabilities without license verification, making it dangerously accessible. The 2024 iteration features enhanced obfuscation techniques and expanded plugin support, posing […]
GhostRat 2024
GhostRat 2024 emerges as one of the most sophisticated Remote Access Trojans (RATs) in the cybersecurity landscape, designed to operate with near-total invisibility. This advanced malware combines fileless execution, AI-driven evasion, and blockchain-based C2 infrastructure to bypass traditional security measures. Targeting both individuals and organizations, GhostRat 2024 enables complete system control while leaving minimal forensic traces, making it a formidable tool […]
Blue Eagle Shades 2024
Blue Eagle Shades 2024 represents a cutting-edge advancement in digital surveillance technology, blending military-grade monitoring capabilities with artificial intelligence-driven analytics. This sophisticated system offers unprecedented visibility into network activities while maintaining complete operational stealth. Designed for both defensive cybersecurity operations and advanced threat intelligence gathering, its modular architecture allows for customized deployment across enterprise networks, […]