Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Vulturi Stealer Cracked 2025
The underground cybercrime ecosystem continues to evolve with increasingly sophisticated data theft tools, and Vulturi Stealer has emerged as one of the most dangerous information stealers in recent years. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial malware to create powerful, low-cost attack tools. Vulturi Stealer Cracked 2025 has been actively […]
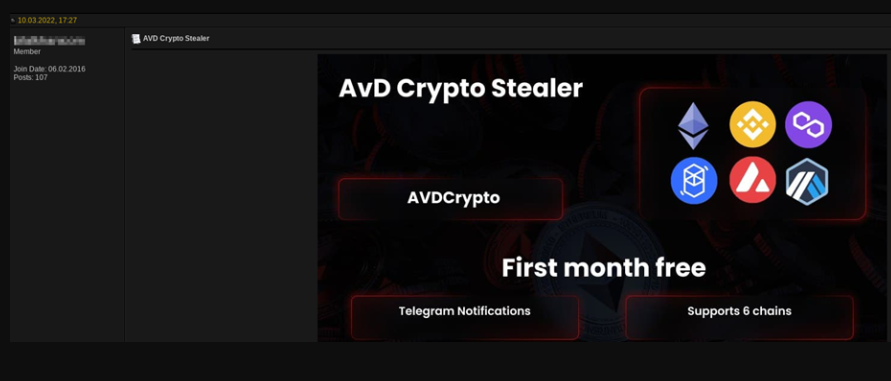
Crypto Ripper 2024
In 2024, cryptocurrency-focused malware has emerged as one of the most lucrative tools in the cybercriminal arsenal, with specialized stealers targeting both retail investors and institutional crypto platforms. Crypto Ripper 2024 sophisticated threats have evolved beyond simple wallet theft to encompass complex attacks against decentralized finance (DeFi) protocols, browser-based wallets, and even hardware wallet integrations. […]
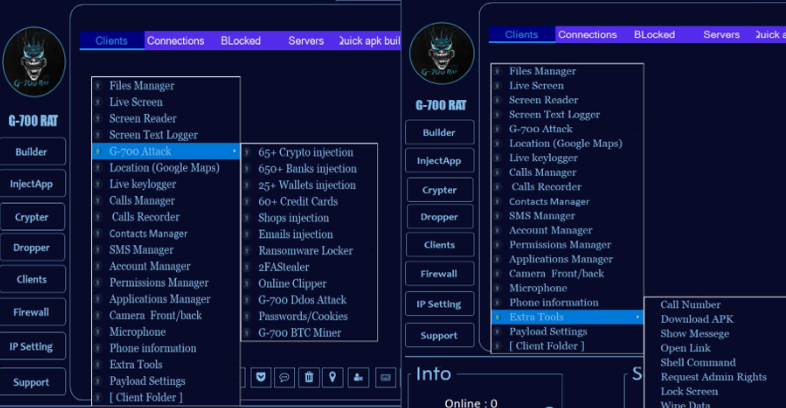
Scorpion Android Rat Cracked 2025
In 2025, cracked versions of advanced Android Remote Access Trojans (RATs) have become a growing threat in the mobile malware landscape, enabling attackers to bypass paywalls and distribute powerful spyware tools to a wider range of cybercriminals. Scorpion Android Rat Cracked 2025 illicitly modified RAT packages lower the barrier to entry for malicious actors, allowing […]
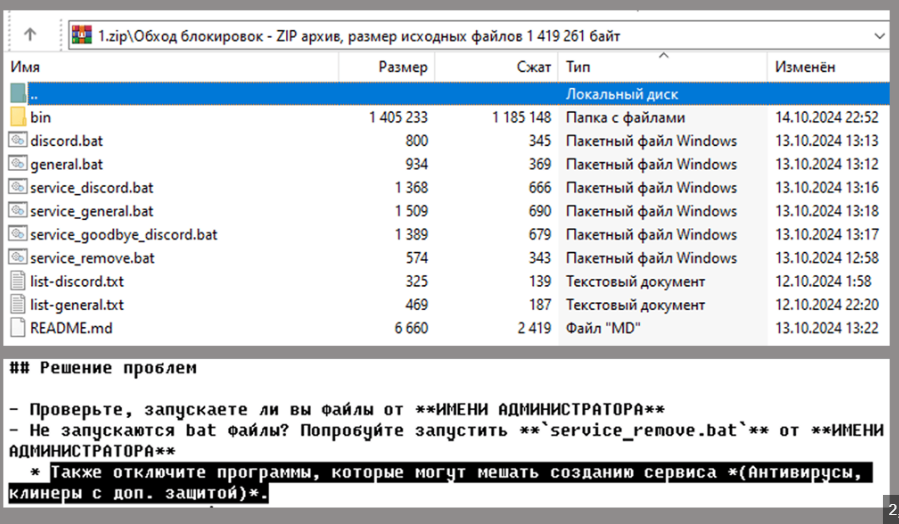
Silent Crypto Miner v2.1.0
Silent cryptocurrency miners have become a significant threat in modern cyberattacks, leveraging compromised systems to generate revenue for attackers without the victim’s knowledge or awareness. One such tool, Silent Crypto Miner v2.1.0, a widely known silent miner, exemplifies this trend by employing stealthy techniques to evade detection while maximising the theft of computational resources. These […]
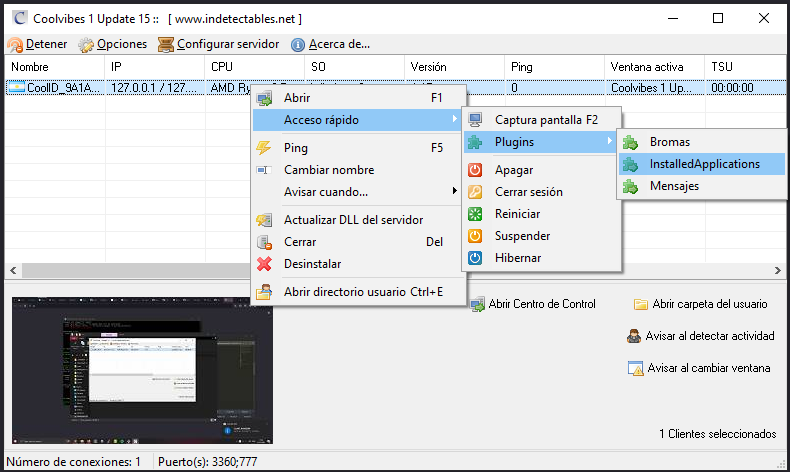
Coolvibes Rat 1.15
The evolution of Remote Access Trojans (RATs) has reached new levels of sophistication in 2024, with modern variants posing significant threats to both individual users and organizations. Coolvibes Rat 1.15 advanced malware tools have transitioned from simple backdoor access to comprehensive surveillance and control platforms, capable of bypassing even robust security measures. Particularly concerning is […]
Native Stealer Cracked 2025
The cybercrime underground continues to evolve with increasingly sophisticated data theft tools, and Native Stealer has emerged as a particularly dangerous threat in modern cyberattacks. This advanced information-stealing malware demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful, low-cost attack tools. This malware has been actively used in credential harvesting campaigns […]
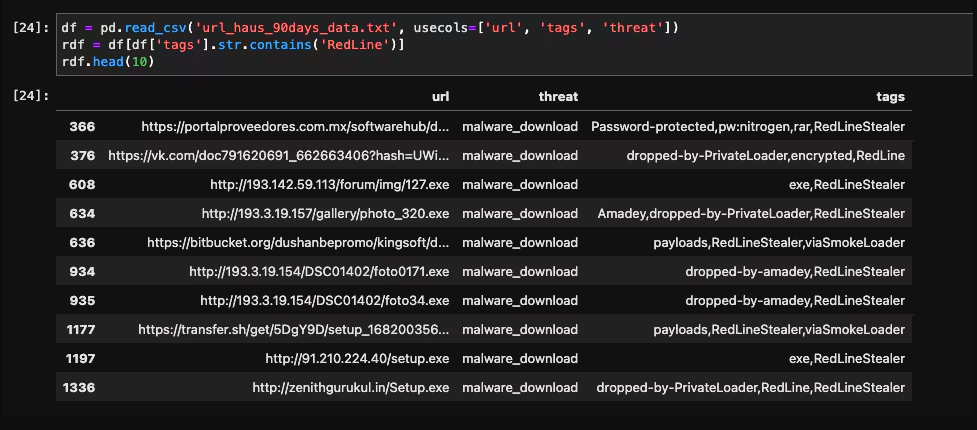
AVD Crypto Stealer 2025
In 2025, cryptocurrency theft has evolved into a highly specialized form of cybercrime, with advanced malware tools targeting both retail investors and institutional crypto platforms. AVD Crypto Stealer 2025 sophisticated stealers represent a significant shift from traditional banking trojans, adapting to the unique challenges of blockchain transactions and decentralized finance (DeFi) ecosystems. Modern variants now […]
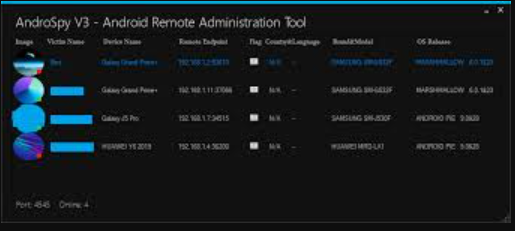
AndroSpy-v3
The mobile threat landscape has grown increasingly sophisticated, with AndroSpy v3 emerging as a particularly dangerous tool in modern cyberattacks targeting Android devices. This advanced surveillance malware exemplifies how cybercriminals are developing more stealthy and feature-rich tools to compromise smartphones. This malware has been actively used in targeted attacks against individuals and organizations, demonstrating its […]
PEGASUS LIME HVNC 2025
In 2025, advanced remote access threats have reached unprecedented levels of sophistication, with next-generation HVNC (Hidden Virtual Network Computing) tools becoming a weapon of choice for both cybercriminals and state-sponsored actors. PEGASUS LIME HVNC 2025 stealthy intrusion platforms represent a significant evolution from traditional RATs (Remote Access Trojans), offering complete device control while remaining virtually […]
Gray Keylogger v3 Cracked
The threat landscape continues to evolve with increasingly stealthy surveillance tools, among which Gray Keylogger has emerged as a particularly insidious threat. This advanced keylogging malware exemplifies how cybercriminals are developing more sophisticated methods to capture sensitive information without detection. Gray Keylogger v3 has been implicated in numerous credential theft campaigns and corporate espionage cases, […]