Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
GhostDZ RAT v1.1D
The GhostDZ RAT v1.1D has emerged as a significant threat in modern cyberattacks, particularly due to its stealthy infiltration capabilities and persistence mechanisms. Often deployed in targeted attacks, this malware enables threat actors to gain long-term access to compromised systems, exfiltrate sensitive data, and execute malicious commands remotely. Its ability to evade detection while maintaining […]
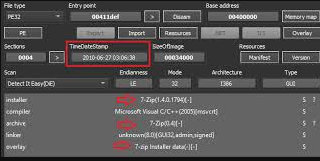
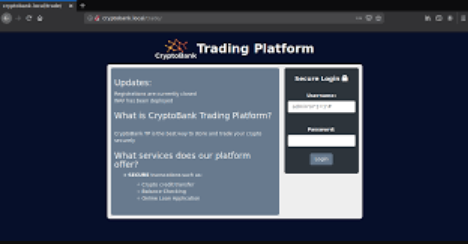
CryptoBanker v0.17a Cracked
The rise of cryptocurrency has given birth to a new generation of financial malware, with CryptoBanker emerging as one of the most sophisticated threats targeting digital asset holders. This advanced malware exemplifies how cybercriminals are adapting traditional banking trojan techniques to exploit cryptocurrency transactions, creating specialized tools for financial theft in the blockchain era. Operating as […]
VenomRAT Cracked v2.7.0.0
In recent years, cybercriminals have increasingly turned to sophisticated malware tools to infiltrate systems, steal sensitive data, and maintain persistent access. One such tool, often distributed through underground forums, is a remote access trojan (RAT) known for its stealth and versatility. VenomRAT Cracked v2.7.0.0 malware has been linked to numerous high-profile attacks, enabling threat actors […]
Android Tester v6.4.6
In the expanding world of mobile malware, a particularly dangerous application has emerged as a significant threat to Android users. This Android Tester v6.4.6, often distributed under the guise of legitimate testing tools, has become a favored weapon for cybercriminals targeting mobile devices. Its sophisticated capabilities allow attackers to gain complete control over infected devices, […]
Supreme Studio v1.0
In the underground cybercrime ecosystem, specialized tools are constantly being developed to streamline attacks, evade detection, and maximize profits for malicious actors. Among these tools is a sophisticated malware development suite known in hacking circles as Supreme Studio v1.0. This all-in-one framework has gained notoriety for enabling even low-skilled criminals to create customized, high-impact malware […]
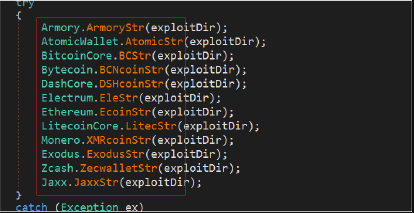
BTC Stealer 2025
Cybercriminals have developed specialized tools to exploit digital asset holders as cryptocurrency adoption grows. Among these threats is a malicious software category designed to steal cryptocurrency wallets and credentials, commonly called BTC Stealer 2025 in underground forums. This type of malware has become increasingly prevalent in attacks targeting both individual investors and exchanges, often leading […]
Improved RedLine Clipper 2025 Cracked
In the ever-evolving world of cybercrime, attackers are constantly refining their tools to exploit digital transactions, particularly those involving cryptocurrencies. One of the most insidious threats to emerge in recent years is an advanced form of malware designed to hijack cryptocurrency transfers by manipulating clipboard data. This sophisticated evolution of traditional Improved RedLine clipper 2025 […]
AsyncRAT v0.5.6
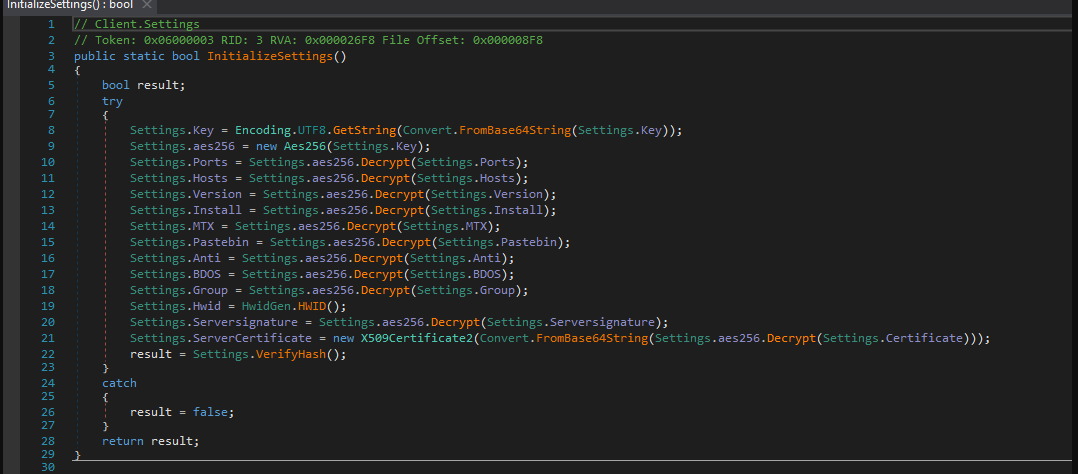
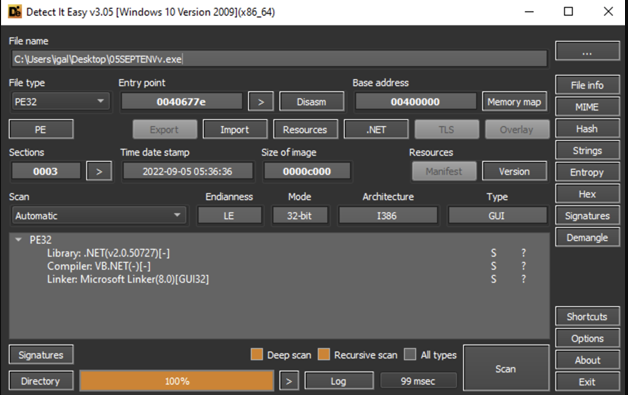
In the rapidly evolving cybersecurity landscape, AsyncRAT v0.5.6 has become increasingly sophisticated, posing significant threats to individuals and organizations alike. One particularly dangerous variant, known for its asynchronous communication capabilities, has gained prominence among cybercriminals for its stealth and versatility. This RAT enables attackers to maintain persistent access to compromised systems while evading traditional detection […]
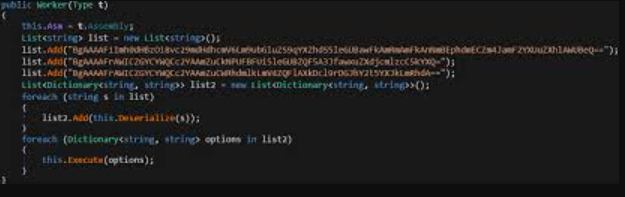
WH-RAT v1.0.1
In today’s threat landscape, WH-RAT v1.0.1 continues to evolve, becoming more sophisticated and dangerous. One such RAT, commonly known by its alias, has emerged as a significant tool for cybercriminals due to its advanced capabilities and ease of deployment. This malware enables attackers to gain complete control over infected systems, steal sensitive data, and carry […]
NJRAT Red Version Error 404
In the ever-evolving world of cyber threats, Remote Access Trojans (RATs) remain a persistent and dangerous tool for attackers. Among these, a well-known NJRAT Red Version —often referred to by its alias—has gained notoriety for its flexibility and widespread use in cyberattacks. This malware enables attackers to take full control of infected systems, steal sensitive […]