Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
ZeroTrace Stealer 2025
In today’s threat landscape, information stealers have become one of the most pervasive and damaging tools in a cybercriminal’s arsenal. The latest generation of these malicious programs demonstrates alarming sophistication, combining stealthy data harvesting capabilities with advanced evasion techniques. These stealers are particularly dangerous because they target the most sensitive user credentials and financial information, […]
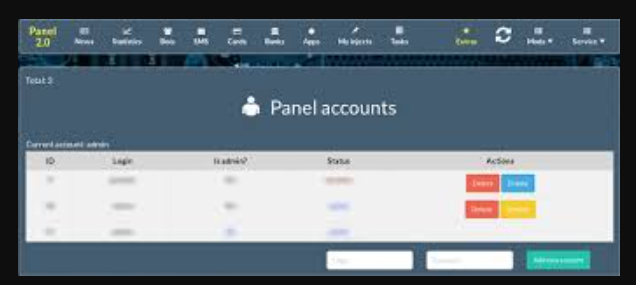
CH Miner 4.0 Builder with Panel Cracked
CH Miner 4.0 Builder with Panel represents a sophisticated evolution in cryptocurrency mining malware toolkits, enabling attackers to create and manage customized mining payloads with alarming efficiency. This malicious software builder has gained notoriety in underground forums for its user-friendly interface and powerful features, allowing even low-skilled threat actors to deploy large-scale cryptojacking operations. Security […]
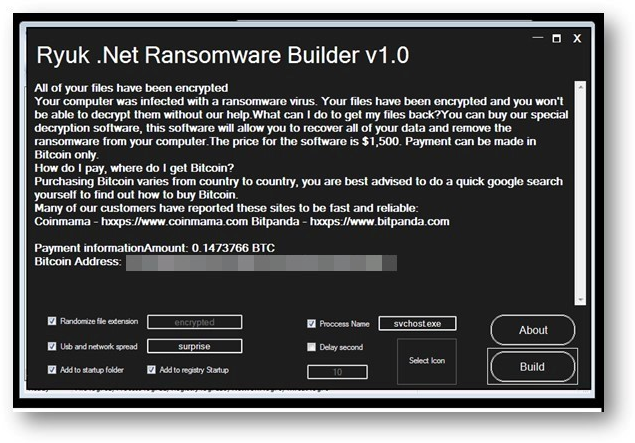
CHAOS RANSOMWARE 2025
Ransomware has emerged as one of the most destructive and financially motivated cyber threats in recent years, with attackers constantly refining their tactics to maximize impact. The latest generation of CHAOS RANSOMWARE 2025 variants demonstrates increased sophistication, combining advanced encryption methods with aggressive propagation techniques. These malicious programs have evolved beyond simple file encryption to […]
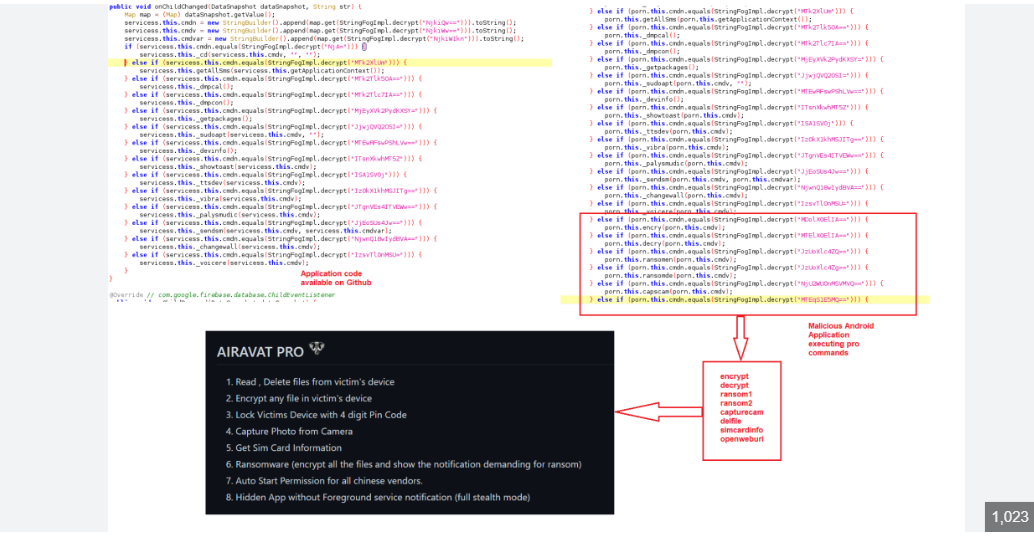
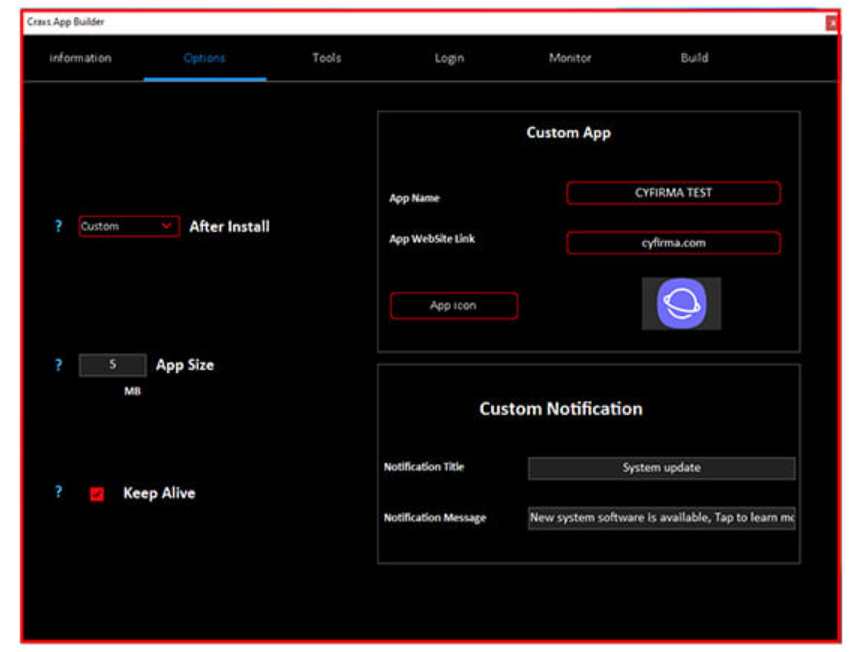
AIRAVAT multifunctional Android RAT 2025
Cybercriminals are increasingly using sophisticated Android Remote Access Trojans (RATs) to breach mobile devices, steal sensitive data, and maintain hidden control over their victims. AIRAVAT multifunctional Android malicious tools pose a severe risk due to their stealthy operation, modular capabilities, and ability to evade detection. Attackers leverage them in espionage, financial fraud, and large-scale botnet […]
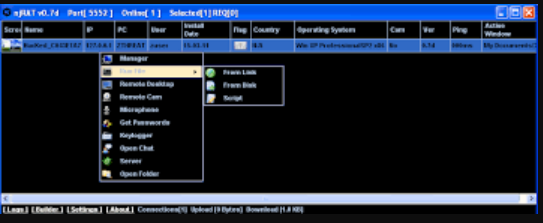
njRAT ACS Version 2024 Cracked
NjRAT ACS Version 2024 represents the latest iteration of a notorious remote access trojan that has become a staple in cybercriminal operations. This enhanced version continues the legacy of its predecessors while incorporating advanced evasion techniques and expanded functionality, making it particularly dangerous in the current threat landscape. Security researchers have observed its widespread use […]
SQLi Dumper V.10.5 Cracked
SQL injection remains one of the most prevalent and dangerous web application vulnerabilities, accounting for numerous data breaches worldwide. The emergence of automated SQL injection tools has significantly lowered the technical barrier for attackers, enabling even novice hackers to exploit vulnerable websites at scale. Cracked versions of commercial SQL injection tools circulating in underground forums […]
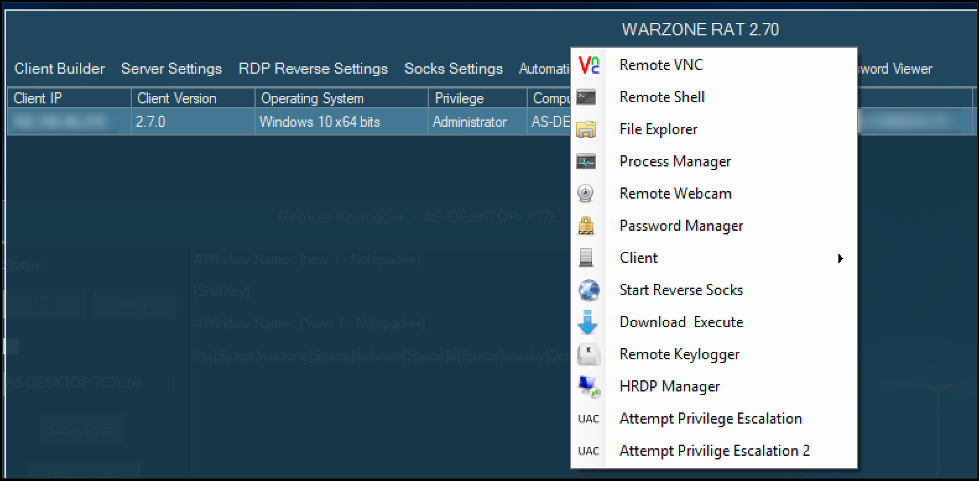
WarZone RAT 3.03 Cracked
In the ever-evolving landscape of cyber threats, Remote Access Trojans (RATs) continue to be a weapon of choice for malicious actors seeking unauthorized access to sensitive systems. The availability of cracked versions of commercial RATs on underground forums has significantly lowered the barrier to entry, enabling even low-skilled attackers to deploy sophisticated surveillance and data […]
Shark Crypto Clipper 2025
In the evolving landscape of cyber threats, malicious tools designed to hijack cryptocurrency transactions have become increasingly sophisticated. One such tool, emerging in 2025, exemplifies this trend by targeting users during financial transactions, silently altering wallet addresses to divert funds to attackers. Shark Crypto Clipper is a type of malware, often referred to as a […]
Eagle Monitor RAT Reborn V3.2.2.0
Remote Access Trojans (RATs) remain one of the most dangerous tools in a cybercriminal’s arsenal, enabling complete control over compromised systems. Modern variants, often distributed through underground forums and illicit marketplaces, have evolved to include advanced evasion techniques and modular capabilities. Eagle Monitor RAT Reborn is frequently used in targeted attacks against businesses, government entities, […]
Exobot 2.5 Trump Edition
Cybercriminals continuously evolve their tools to bypass security measures and maximize their illicit gains. Among these threats, advanced banking trojans have emerged as a significant risk, particularly those distributed through underground markets in cracked or modified forms. Exobot 2.5 variants are often designed to steal financial data, automate fraudulent transactions, and evade detection—making them a […]