Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Hack Pack 2025
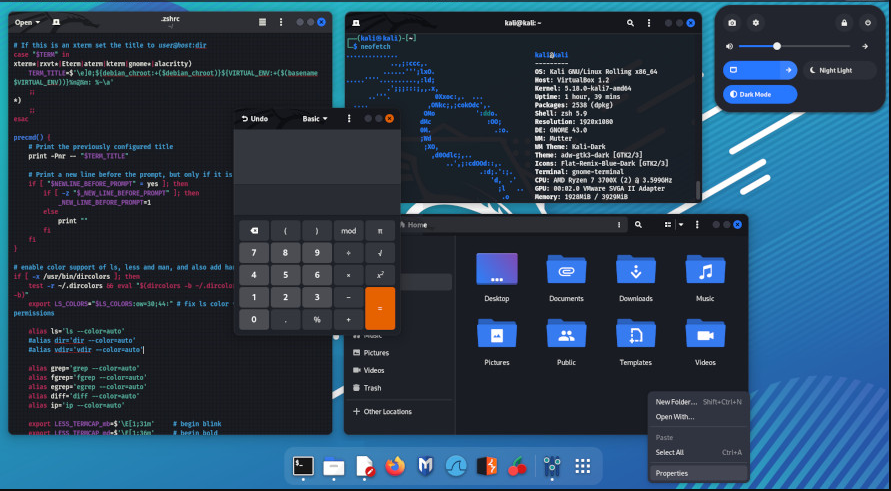
The cybersecurity threat landscape has seen a surge in all-in-one attack toolkits that bundle multiple malicious capabilities into a single package. These comprehensive suites lower the barrier to entry for cybercriminals by providing ready-made tools for various attack vectors. Particularly concerning is their modular design, which allows even novice attackers to launch sophisticated campaigns with […]
Screen Lock Builder 1.1.2.0
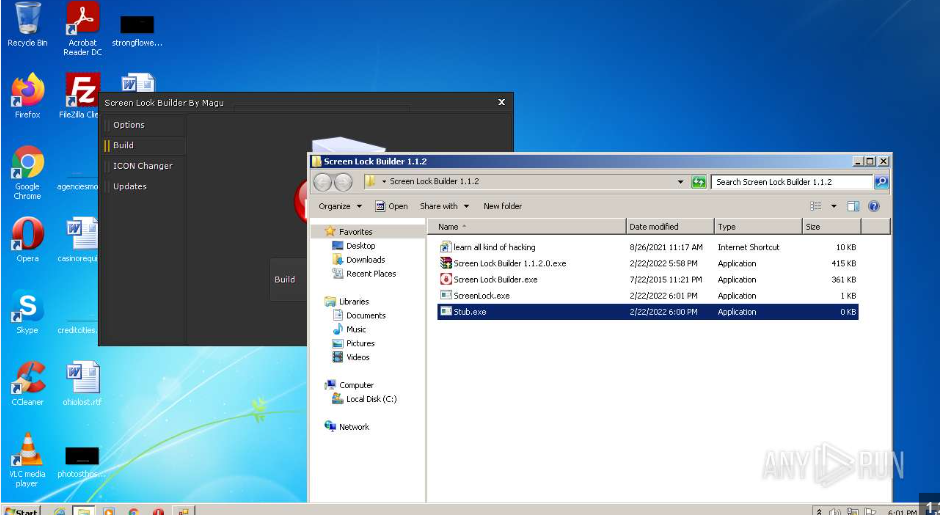
In recent years, cybercriminals have increasingly turned to specialized tools to enhance the effectiveness of their attacks. One such tool, often distributed through malicious campaigns, is designed to lock users out of their systems while demanding payment for restoration. Screen Lock Builder attacks, commonly categorized as ransomware or screen locker threats, disrupt productivity and extort […]
StormKitty Stealer 2025
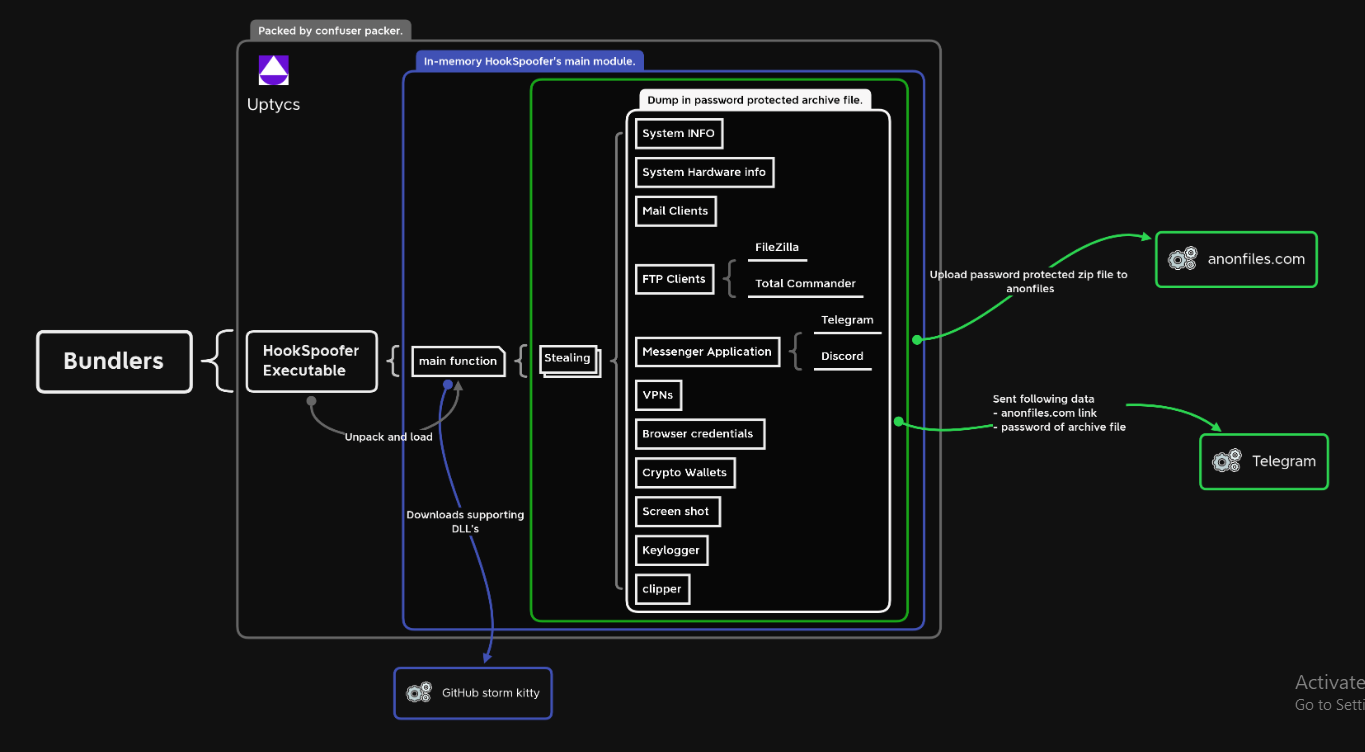
In the ever-evolving landscape of cyber threats, information stealers have become one of the most prevalent and damaging tools in an attacker’s arsenal. These specialized malware variants are designed to covertly harvest sensitive data from infected systems, often leading to financial fraud, identity theft, and corporate espionage. The latest iterations of these stealers demonstrate increasing […]
Mars Stealer v3 Cracked
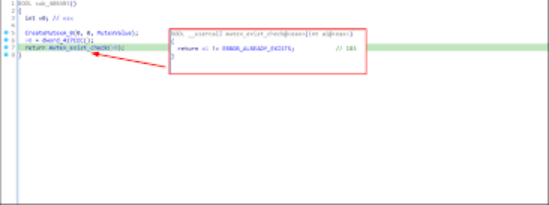
The cybersecurity landscape faces an escalating threat from sophisticated information stealers, with Mars Stealer v3 Cracked emerging as one of the most dangerous tools in modern credential harvesting campaigns. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful attack tools at minimal cost. Mars Stealer v3 Cracked […]
Cypher Rat 2025 cracked
In recent years, cybercriminals have increasingly relied on sophisticated information-stealing malware to compromise sensitive data. One such tool, often referred to as “X-FILES STEALER 2025,” has gained notoriety for its ability to evade detection while exfiltrating credentials, financial data, and other valuable information. These stealers are frequently distributed through phishing campaigns, malicious downloads, or exploit […]
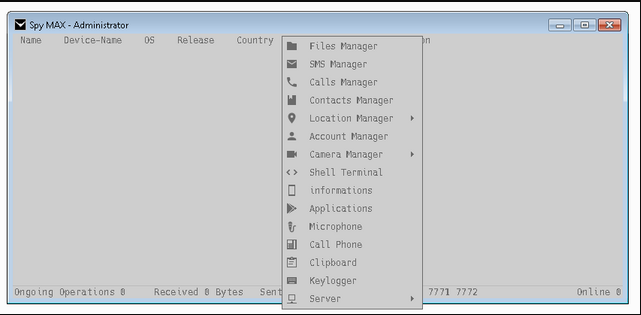
SpyMax 4 RAT Cracked
Cybercriminals increasingly rely on commercially available spyware tools to conduct surveillance and data theft operations. Among these threats, cracked or pirated versions of legitimate monitoring software pose a significant risk, as they are often repurposed for malicious activities. SpyMax 4 RAT provides attackers with powerful capabilities while evading legal restrictions, making them attractive for unauthorized […]
PEGASUS RAT 2024 FULL VERSION SOURCE
Cyberattacks have grown increasingly sophisticated, with advanced remote access trojans (RATs) becoming a favored tool for threat actors. These malware strains enable attackers to infiltrate systems, exfiltrate sensitive data, and maintain long-term access without detection. Among these threats, highly customizable RATs—often distributed through exploit kits, phishing, or zero-day vulnerabilities—pose significant risks to governments, corporations, and […]
X-FILES STEALER CRACKED 2024
The rise of information-stealing malware has significantly impacted modern cyberattacks, with tools like “X-FILES STEALER CRACKED” becoming a notable threat. These malicious programs are designed to exfiltrate sensitive data from compromised systems, often targeting credentials, financial information, and personal documents. Cracked or pirated versions of such software are particularly dangerous, as they are distributed freely […]
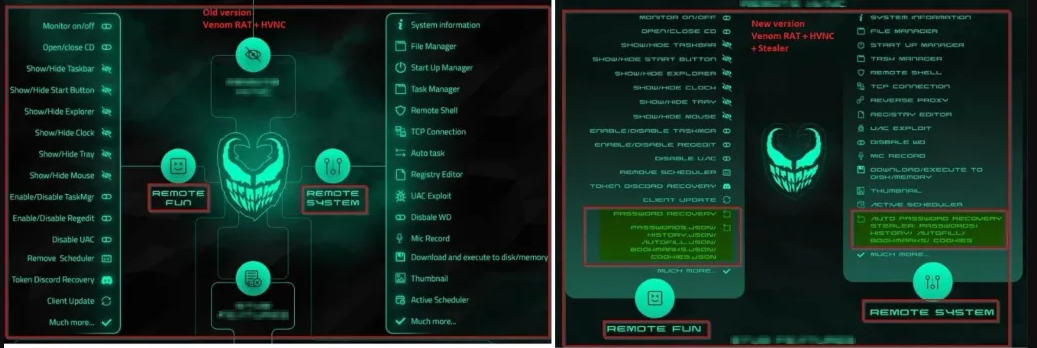
VENOM RAT 2.8 FINAL HRDP LOCKER HVNC RAT
Cyber threats continue to evolve, with remote access trojans (RATs) playing a significant role in modern cyberattacks. These malicious tools provide attackers with unauthorized control over compromised systems, enabling data theft, surveillance, and further network infiltration. Among these threats, advanced RATS stand out due to their stealth, persistence, and ability to bypass security measures. VENOM […]
Redline Clipper Cracked 2024
Cybercriminals continuously evolve their tools to bypass security measures, and one such tool gaining attention is the “Redline Clipper Cracked 2024.” This malicious software has been increasingly observed in modern cyberattacks, particularly in credential theft and financial fraud. By manipulating clipboard contents in real time, attackers can redirect cryptocurrency transactions or steal sensitive data without […]