CEH V11 EC-COUNCIL CERTIFIED ETHICAL HACKER
The CEH v11 (Certified Ethical Hacker) certification by EC-Council is a globally recognized program designed to train cybersecurity professionals in identifying and mitigating vulnerabilities in modern systems. As cyberattacks become increasingly sophisticated, ethical hacking tools and methodologies—often covered in resources like the EC-Council Certified Ethical Hacker (CEH V11)— play a crucial role in both offensive and defensive cybersecurity. Attackers frequently exploit weaknesses in networks, applications, and human behavior, making ethical hacking knowledge essential for penetration testers, security analysts, and IT professionals to defend against real-world threats.
The software in question is a powerful penetration testing tool used by security experts to simulate cyberattacks and assess system vulnerabilities. It is commonly employed in ethical hacking, red teaming, and security research to identify weaknesses before malicious actors can exploit them. The tool integrates multiple attack vectors, including network scanning, exploitation, and post-exploitation techniques, making it a comprehensive solution for security assessments.
Key Features
| Feature | Description |
| Network Scanning | Detects live hosts, open ports, and services running on target systems. |
| Exploitation Framework | Provides pre-built and customizable exploits for known vulnerabilities. |
| Payload Delivery | Supports multiple payload types (e.g., reverse shells, malware) for post-exploitation. |
| Social Engineering | Facilitates phishing and other human-based attack simulations. |
| Reporting & Logging | Generates detailed reports for vulnerability analysis and remediation. |
How the Software Works
The software employs a structured approach, combining reconnaissance, exploitation, and persistence techniques to simulate real-world attacks. Below is a breakdown of its functionality:
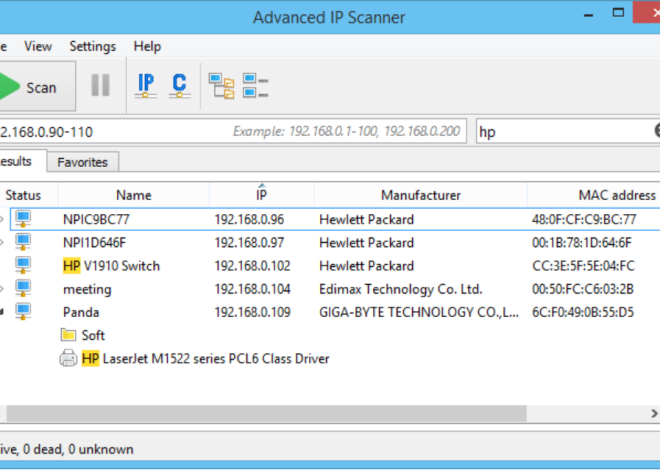
Reconnaissance & Scanning
- The tool begins by gathering information about the target, including IP ranges, active hosts, and open ports, using techniques such as ARP scanning, ICMP pings, and service fingerprinting.
- Vulnerability scanning identifies weak points in services (e.g., outdated software, misconfigurations).
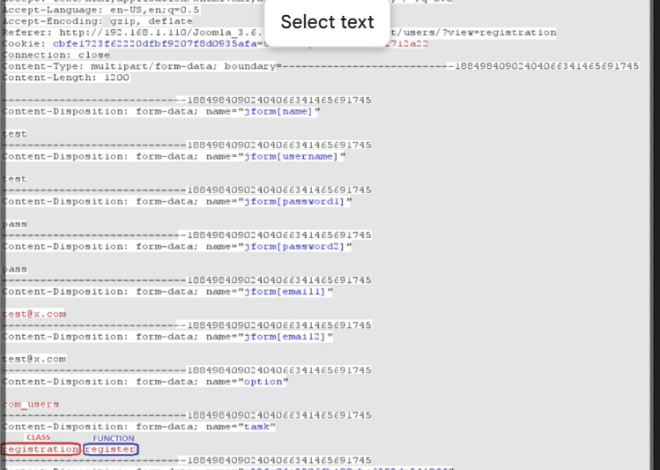
Exploitation
- Once vulnerabilities are detected, the software leverages its exploit database to execute attacks. Standard methods include buffer overflows, SQL injection, or credential brute-forcing.
- Exploits are often modular, allowing testers to customize attacks based on the target environment.
Payload Delivery & Post-Exploitation
- After gaining initial access, the software deploys payloads to maintain persistence, escalate privileges, or move laterally across the network.
- Payloads may include reverse shells for remote control, keyloggers for data theft, or ransomware for destructive testing (in controlled environments).
Covering Tracks (Optional)
- Advanced modules can erase logs or modify system files to avoid detection, simulating how real attackers evade security monitoring.