DARKTRACK 4 ALIEN: Stealth Android Shadow Tool
What is DARKTRACK 4 ALIEN? DARKTRACK 4 ALIEN is a silent, powerful Remote Access Trojan that infiltrates Android devices to grant hidden control. Operating in the shadows of 2026, it turns ordinary smartphones into surveillance nodes for remote operators.
Download Link 1
Download Link 2
Download Link 3
Key Features of DARKTRACK 4 ALIEN
Invisible Remote Domination Full command over the device — launching apps, controlling screens, and executing actions unseen.
Silent Visual Feed Live screen streaming and recording that captures every displayed activity.
Hidden Eyes and Ears Camera and microphone access that activates without notification or visible indicators.
Deep Data Harvest File exploration, SMS interception, call log extraction, and contact theft.
Keystroke Ghost Advanced keylogger that records every tap and password entry.
Location Phantom Continuous GPS tracking that maps the device’s every move.
Eternal Persistence Stealth mode and anti-removal that keeps the tool alive despite restarts or scans.
Clever Delivery Binder and customization options to disguise payloads inside trusted apps.
Evasion Armor Strong bypass against modern mobile security layers and analysis tools.
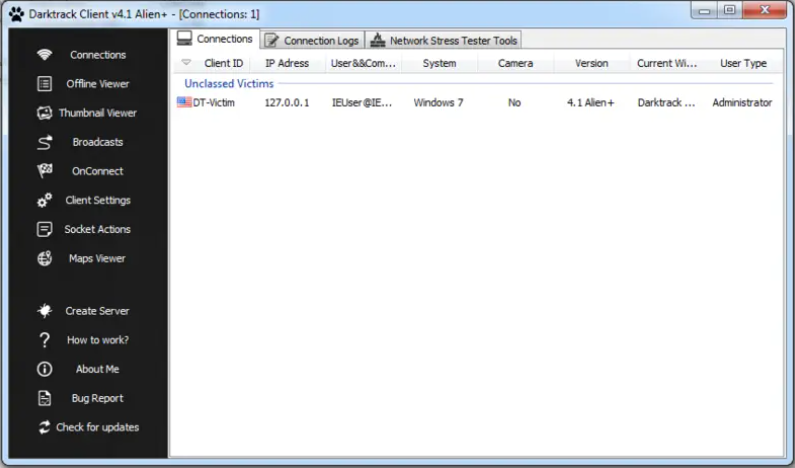
Shadow Panel Central dashboard for commanding multiple infected devices in silence.
How DARKTRACK 4 ALIEN Works The process begins in darkness. The builder crafts a tailored APK. Social engineering delivers it to the target. Once installed, the payload awakens quietly, requests permissions under the guise of normal functions, and vanishes from view.
It phones home to the C&C server, registers the device, and waits for commands. When orders arrive, the device obeys — streaming visuals, capturing audio, harvesting files, or logging inputs — all while the user remains unaware.
Data travels encrypted back to the operator. Persistence mechanisms ensure survival. In 2026, improved evasion lets it operate longer on updated Android versions.
DARKTRACK 4 ALIEN moves like a ghost in the machine, turning personal devices into windows for remote eyes. Its feature set makes it a dangerous yet effective tool in the underground mobile threat world.