Dork Searcher V3 By CRYP70
Cyberattacks continue to evolve, leveraging increasingly sophisticated tools. Among these, Dork Searcher V3 By CRYP70 plays a critical role in identifying and exploiting vulnerabilities. This type of tool streamlines the process of gathering sensitive information from exposed systems, enabling attackers to deploy follow-up exploits efficiently. As a result, it has become a significant enabler of modern cyber threats.
Primarily, the tool scans and extracts data from misconfigured or publicly exposed databases, directories, and services. By automating queries to search engines and other data sources, it identifies potential targets, such as unsecured servers, open ports, or sensitive files. While penetration testers may use similar tools for legitimate security assessments, malicious actors often abuse them to facilitate data breaches, credential theft, and other cyberattacks.
Download Link 1
Download Link 2
Download Link 3
Download Link 4
Key Features
| Feature | Description |
|---|---|
| Automated Scanning | Rapidly queries search engines and public databases to find exposed systems. |
| Custom Search Dorks | Supports user-defined search parameters to refine target discovery. |
| Payload Delivery | Can deploy malicious scripts or exfiltrate data from vulnerable systems. |
| Multi-Platform Support | Works across Windows and Linux environments. |
| Anonymization Techniques | Uses proxies or VPNs to hide the attacker’s origin. |
How Dork Searcher V3 By CRYP70Works
The tool operates systematically, progressing from reconnaissance to payload delivery. Below is a breakdown of its functionality:
1. Target Discovery
- The software uses predefined or custom “dorks” (specialized search queries) to scan for exposed web applications, databases, or files.
- Additionally, it may crawl public directories or APIs to find misconfigured services, such as open FTP servers or unsecured cloud storage.
2. Vulnerability Verification
- After identifying potential targets, the tool performs basic checks to confirm accessibility, such as testing default credentials or unprotected endpoints.
- Some versions include fingerprinting techniques to detect software versions (e.g., CMS, database type) for known exploits.
3. Payload Execution
- Depending on the attacker’s goals, the tool may deliver malicious scripts (e.g., web shells for persistent access) or extract sensitive data, such as credentials.
- In some cases, it chains its findings with other exploitation frameworks to escalate attacks, such as deploying ransomware or moving laterally within a network.
4. Anonymization & Evasion
- To avoid detection, the software routes traffic through proxies, Tor, or virtual private networks (VPNs).
- Some versions include rate-limiting or randomized delays to evade IP-based blocking.
By automating these steps, the tool drastically reduces the effort needed for large-scale attacks, making it a favorite among cybercriminals. Its effectiveness relies on the abundance of misconfigured systems and exposed data online. To mitigate risks, organizations must strengthen security configurations, monitor for exposures, and implement robust access controls.
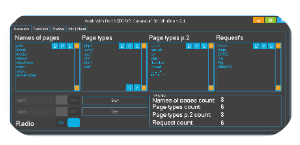
![Work With Dorks [DORK’s Generator]-Dork Generator](https://blackhatus.com/wp-content/uploads/2025/07/Work-With-Dorks-DORKs-Generator-Dork-Generator-1.png)