Nigger RAT v1.8
🧠 What is Nigger RAT v1.8?
Nigger RAT v1.8 is a cutting-edge remote access tool designed for full unauthorized control and silent monitoring of target Windows PCs. This version focuses on enhanced evasion, richer data collection, and easier management of infected systems.
With features like hidden VNC, comprehensive credential theft, real-time keylogging, and plugin extensibility, it serves both individual hackers and organized groups. Nigger RAT v1.8 maintains low system impact while providing reliable long-term access and efficient data exfiltration. Its modern builder and dashboard ensure quick setup and smooth operation. 🚀
⚡ Key Features of Nigger RAT v1.8
🖥️ Stealth HVNC Remote Desktop
Completely hidden control sessions for safe and discreet operations.
🔑 Comprehensive Password Extractor
Targets all popular browsers, apps, and Windows credential vaults.
⌨️ Advanced Keystroke Recorder
Logs input with detailed context and multilingual support.
📂 Smart File Exfiltration
Automatic detection and transfer of important documents and databases.
🌐 Full Browser Data Harvesting
Steals cookies, history, and active sessions for quick account access.
💰 Crypto Theft Tools
Clipboard monitoring and wallet file extraction for financial gain.
🧩 Flexible Plugin Support
Add new capabilities like encryption or mining modules easily.
🛡️ Strong Anti-Analysis Protection
Bypasses AV, EDR, and virtual environment detection.
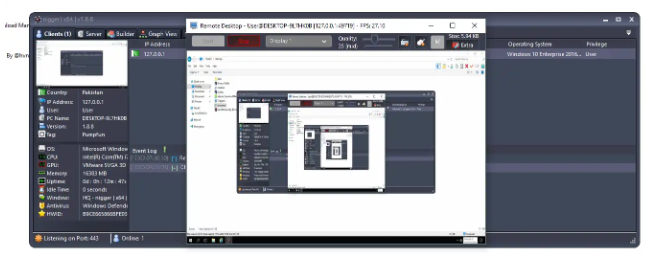
📊 Advanced C2 Management Interface
Real-time victim tracking with detailed information and bulk controls.
🔄 How Nigger RAT v1.8 Works – Complete Technical Breakdown
Nigger RAT v1.8 follows an efficient client-server workflow. The builder lets users create highly customized payloads with strong obfuscation and multiple persistence options. After infection, the client connects back to the C2, sends system details, and awaits commands.
Operators use the dashboard to activate HVNC, start keylogging, dump credentials, and manage files. Data is transferred securely in small packets. The RAT uses advanced techniques to stay hidden, including memory execution and traffic camouflage. Version 1.8 offers better stability and updated evasion against the latest security tools.