Octo Botnet: Stealthy Android RAT Platform
What is Octo Botnet Octo Botnet represents a mature, service-based Android malware solution optimized for remote access and fraud execution. Evolving from ExobotCompact and maintaining links to the Exobot family, it is marketed with a control panel for building and orchestrating infections. Known interchangeably as Coper, the platform prioritizes on-device fraud through direct takeover capabilities. Its design supports high-survival deployments across diverse Android ecosystems, with variants incorporating DGA and advanced obfuscation. Renters benefit from modular tools that facilitate credential theft, session hijacking, and persistent control, making Octo a practical choice for operators needing dependable performance without extensive technical overhead in fast-changing mobile threat scenarios.
Download Link 1
Download Link 2
Download Link 3
Key Features
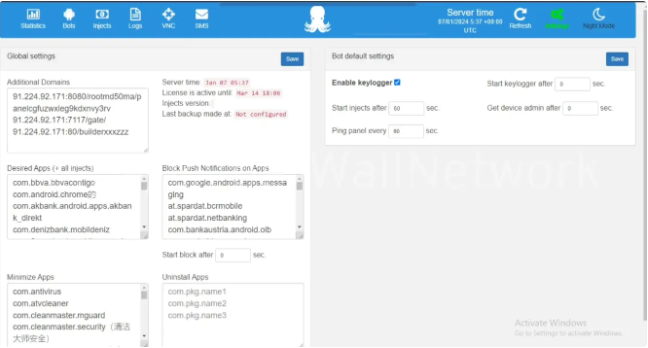
- Live Remote Control (VNC/HVNC): Gesture simulation, screen streaming, and full interaction for takeover scenarios.
- Targeted Banking Injects: Overlays and keylogging tailored to financial apps for efficient data capture.
- Notification/SMS Management: Real-time interception and blocking to maintain operational secrecy.
- Advanced Stealth Mechanisms: Screen dimming, black overlays, sound control, and app launching in hidden modes.
- MaaS Panel with Builder: Custom payload creation and device fleet management tools.
- Resilient C2 with DGA: Dynamic addressing and per-request keys for evasion and uptime.
- Multi-Version Android Support: Optimized for versions 9-14 with stability enhancements in later releases.
How It Works Octo Botnet’s mechanics emphasize layered infection, resilient communication, and precise control to maximize uptime and success rates. The journey starts at the operator panel, where builders produce customized APKs. These often masquerade as legitimate utilities or use droppers like Zombinder to stage the infection, requesting secondary installs that load the full trojan while soliciting Accessibility Service permissions.
After installation, the payload phones home to the C2 using robust encryption. Variants such as Octo2 introduce DGA for generating varied domain names and unique keys per interaction, complicating blocking efforts. Configurations pulled from the server include app-specific rules, timing parameters, and available commands, drawn from a command set refined over iterations.
Once connected, the malware leverages Android APIs to establish a virtual presence on the device. MediaProjection enables screen capture and streaming to the panel, while Accessibility allows input simulation—taps, swipes, text entry—giving operators god-like control. During fraud windows, it can suppress notifications, mute audio, reduce brightness, or apply black screen overlays, creating the illusion of inactivity.
Interception features monitor and reroute SMS, push alerts, and clipboard data. Keylogging operates continuously, logging entries from any app. For banking targets, custom overlays mimic legitimate interfaces to phish credentials or authorize actions remotely.
Anti-detection layers include obfuscated code, multi-stage loading (decrypting payload parts only when needed), and checks to avoid analysis environments. Session optimizations in updated versions lower resource use, improving reliability on varied network conditions and device hardware.
Operators interact via the panel to view connected devices, send targeted commands, or run automated scripts based on pre-set delays. The service model ensures the core infrastructure and updates are managed upstream, allowing focus on campaign strategy rather than maintenance.
Typical workflow: disguised APK sideload or dropper delivery → permission acquisition → encrypted C2 beacon with device telemetry → targeted config application → trigger detection (banking app open) → stealth engagement and remote session → data harvest and exfiltration → optional persistence mechanisms.
This structured yet flexible approach, building on proven code lineages while adding contemporary resilience, makes Octo Botnet an effective product for sustained mobile operations in the underground economy.