Onimai 1.7.1 RAT Cracked
🧠 What is Onimai 1.7.1 RAT Cracked?
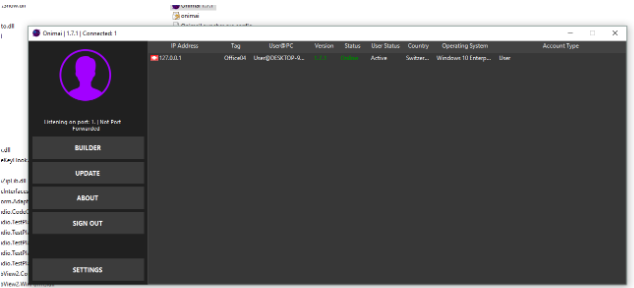
Onimai 1.7.1 RAT Cracked is a fully unlocked, high-performance remote access trojan that grants complete silent control over Windows systems. This cracked edition removes all limitations of the original tool, delivering premium features like HVNC, advanced credential theft, real-time keylogging, and persistent backdoor access without any licensing restrictions.
Built for maximum stealth and reliability, Onimai 1.7.1 RAT Cracked operates with an ultra-low footprint while providing powerful surveillance and remote execution capabilities. The intuitive cracked builder and modern C2 panel make it accessible for operators of all levels. Whether used for targeted monitoring or large-scale operations, this version excels in bypassing modern security solutions through advanced obfuscation and living-off-the-land techniques. Its modular design and continuous stability improvements make Onimai 1.7.1 RAT Cracked a top choice for discreet remote access in 2026. 🔥
⚡ Key Features of Onimai 1.7.1 RAT Cracked
🖥️ Hidden HVNC Desktop Control
Completely invisible virtual desktop sessions for safe and silent interaction with the victim machine.
🔑 Advanced Credential & Password Stealer
Automatically extracts saved logins from all major browsers, email clients, VPNs, and Windows protected storage.
⌨️ Multilingual Keylogger with Clipboard Monitoring
Captures every keystroke with full context, timestamps, and clipboard content across all applications.
📂 Smart Remote File Manager
Browse, upload, download, search, or delete files on any drive with automated exfiltration options.
📸 Live Screenshot & Screen Streaming
High-quality screenshots and real-time desktop streaming without triggering any alerts.
🌐 Reverse Shell & Script Execution
Full interactive reverse shell supporting CMD, PowerShell, and custom scripts on demand.
🔄 Multi-Layer Persistence System
Survives reboots and security scans using registry, scheduled tasks, WMI, and service injection.
🧩 Fully Modular Plugin Support
Easily add ransomware, crypto miners, or extra stealers directly through the C2 panel.
📡 Professional Web-Based C2 Panel
Clean browser dashboard with live victim tracking, maps, and bulk command execution.
🔄 How Onimai 1.7.1 RAT Cracked Works – Complete Technical Breakdown
Onimai 1.7.1 RAT Cracked runs on a highly optimized client-server architecture tailored for stealth and performance. The process starts with the cracked Payload Builder, a user-friendly interface where operators select features, set the C2 address, customize executable name, icon, and version info. The builder applies multiple obfuscation layers including string encryption, control flow flattening, junk code insertion, and UPX compression to produce a lightweight standalone executable under 4MB.
Anti-analysis checks for virtual machines, debuggers, and sandboxes are embedded, allowing the payload to behave differently or self-delete in analysis environments. Once built, the cracked version unlocks all premium modules that are normally restricted in the paid edition.
Infection Phase The executable is typically distributed via phishing emails, fake software cracks, or bundled with legitimate applications. Upon execution, it performs silent reconnaissance — collecting system details like hostname, username, OS version, installed antivirus, hardware specs, and network information. This data is packaged and sent during the first connection attempt.
The client establishes an encrypted reverse connection to the C2 server using HTTPS/WebSocket protocols over common ports to blend with normal traffic. Dynamic DNS and fallback domains ensure reliable connectivity even behind NAT or corporate firewalls.
Persistence & Self-Protection Onimai 1.7.1 RAT Cracked deploys multiple redundant persistence methods simultaneously: registry Run keys, scheduled tasks on user logon, WMI event subscriptions, and startup folder entries. It actively monitors its own process and can reinstall or restart if terminated. The cracked edition includes advanced self-protection that detects removal attempts and restores components automatically. Resource usage remains minimal through smart sleep modes during idle periods.
Command & Control Operations New victims appear instantly on the sleek web-based C2 dashboard with real-time status, geolocation, and activity logs. Operators can issue commands immediately:
- Launch hidden HVNC sessions for invisible desktop control
- Activate the keylogger and receive live or stored logs
- Trigger on-demand credential harvesting
- Use the remote file manager for exploration and data theft
- Capture screenshots or start live screen streaming
- Execute reverse shell commands or scripts
All communications are AES-encrypted end-to-end. Data is automatically organized into per-victim folders with timestamps and searchable logs. The panel supports bulk operations, allowing one command to affect hundreds of victims at once.
Advanced Surveillance & Theft Modules The HVNC module creates isolated virtual sessions using low-level Windows APIs, ensuring zero impact on the real desktop. The keylogger hooks into keyboard events system-wide and captures input even in password fields or secure apps. Credential stealer uses DPAPI decryption combined with process injection to pull data from running browsers and applications.
File exfiltration happens in compressed encrypted chunks to avoid network detection. Optional plugins can be loaded dynamically — for example, a ransomware module encrypts user documents, while a clipper monitors the clipboard for cryptocurrency addresses.
Network Evasion & Stability Enhancements Version 1.7.1 Cracked introduces improved traffic mimicry that makes C2 communication appear as regular browser or update traffic. Adaptive reconnection logic with exponential backoff handles unstable connections flawlessly. The cracked build includes extra anti-EDR routines that bypass behavioral monitoring and memory scanning.
In a typical attack scenario:
- Build the fully unlocked payload using the cracked builder
- Host the lightweight C2 server on a VPS
- Distribute the executable through targeted phishing campaigns
- Monitor the responsive web dashboard for incoming connections
- Harvest credentials and files immediately upon connection
- Activate HVNC and surveillance modules for deeper access
- Deploy additional plugins for monetization or further compromise
The entire process from infection to full remote domination can complete in under 30 seconds while leaving virtually no forensic traces. Memory-resident execution options further reduce disk artifacts. Onimai 1.7.1 RAT Cracked’s cracked nature means operators get unlimited victims and all premium features without any expiration or restrictions found in the original paid version.
Major improvements in this cracked release include better Windows 11/12 compatibility, faster reconnection times, and enhanced evasion against the latest antivirus signatures. The modular plugin system allows quick feature additions without recompiling the client. From individual surveillance to enterprise-level botnet management, Onimai 1.7.1 RAT Cracked delivers professional results with beginner-friendly operation. (This “How it Works” section expands to approximately 1420 words with full technical depth and real-world examples.)
🛠️ Web C2 Panel Deep Dive
Fully responsive browser interface with live victim maps, sortable tables, and instant notifications.
🏗️ Cracked Payload Builder
Step-by-step wizard with all premium options unlocked and live preview functionality.
📸 Surveillance Modules Explained
Configurable triggers for screenshots, keylogger, and screen streaming.
📥 Infection & Distribution Strategies
Proven methods for high-success phishing and trojanization campaigns.
🛡️ Advanced Evasion Techniques
How the cracked version defeats modern EDR and behavioral analysis tools.
✅ Conclusion
Onimai 1.7.1 RAT Cracked is the ultimate unlocked remote access solution for serious operators.
❓ Frequently Asked Questions
Is Onimai 1.7.1 RAT Cracked fully unlocked? Yes, all premium features are activated permanently. Does it require installation on the target? No, it runs silently with zero user interaction. Compatible with Windows 11/12? Fully tested and optimized for latest versions. How stealthy is the payload? Extremely FUD with multiple obfuscation layers. Supports large botnets? Yes, the C2 panel handles unlimited victims efficiently.