OwnZ Crypter 3.5.9
OwnZ Crypter 3.5.9 is a cutting-edge file encryption and obfuscation tool designed to protect executable files from detection and analysis. It is widely used by developers, cybersecurity professionals, and ethical hackers to safeguard their software from reverse engineering and malicious attacks. With advanced features and a user-friendly interface, OwnZ Crypter ensures top-tier security for sensitive […]
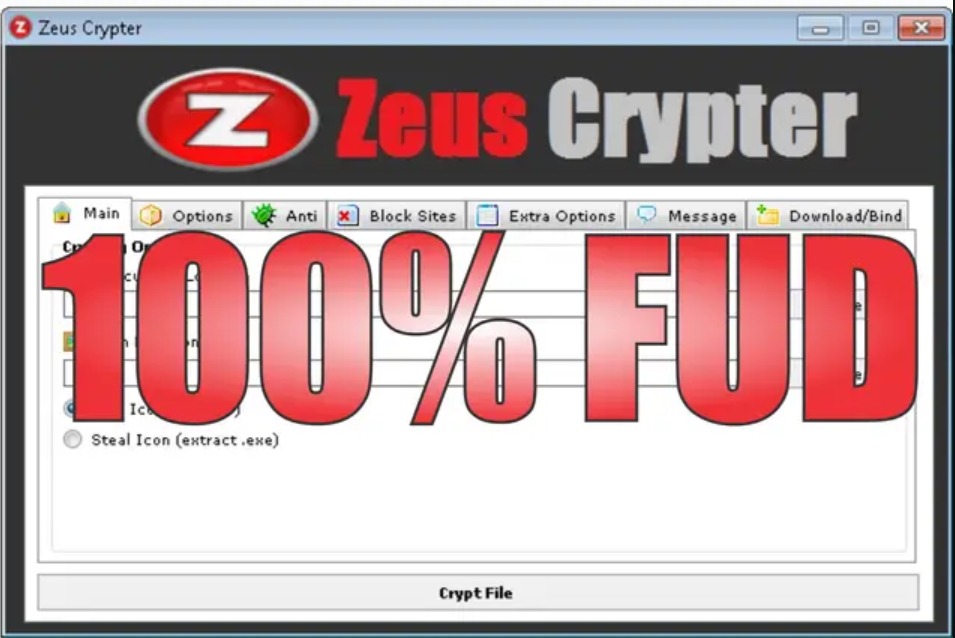
Zeus Crypter 2024
In the ever-evolving landscape of cybersecurity, protecting sensitive files and executables from detection and analysis is crucial. Zeus Crypter 2024 emerges as a cutting-edge solution designed to encrypt, obfuscate, and secure files against reverse engineering and antivirus detection. Whether for ethical penetration testing or advanced malware research, Zeus Crypter 2024 offers robust features to ensure […]
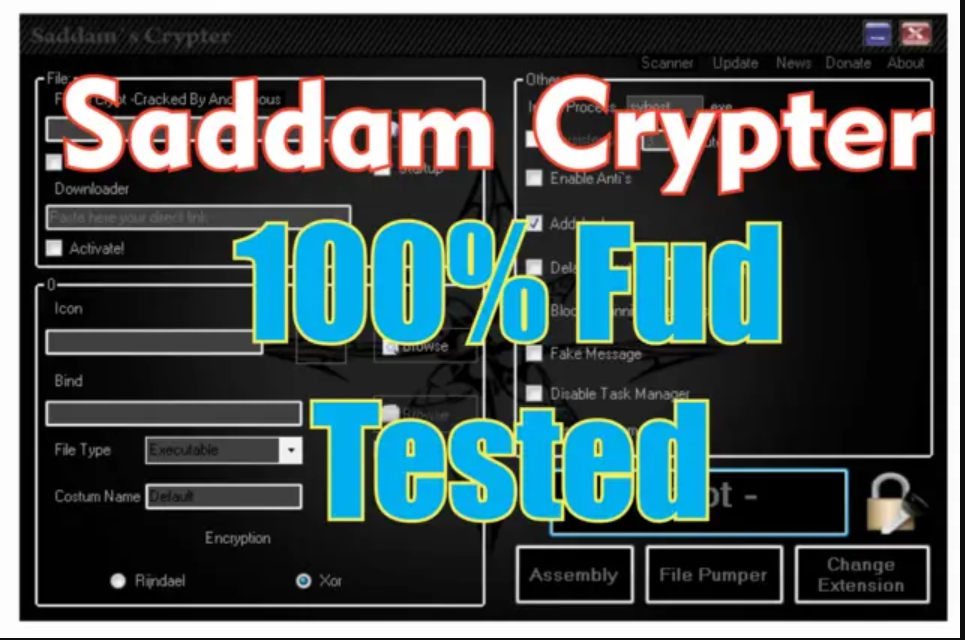
Saddam Crypter 2024
In an era where digital security is paramount, Saddam Crypter 2024 emerges as a cutting-edge solution for encryption and data protection. Designed for both cybersecurity professionals and privacy-conscious users, this tool offers advanced features to safeguard sensitive information from unauthorized access. Whether for personal use or enterprise-level security, Saddam Crypter 2024 provides a robust defense against cyber […]
War botnet Cracked
War Botnet Cracked is an illicitly modified version of a sophisticated botnet framework designed to create and control networks of compromised devices. Originally developed for malicious purposes, the cracked version circulates underground, enabling unauthorized users to deploy cyberattacks without proper licensing. While it may appear as a powerful tool, its use is strictly illegal and […]
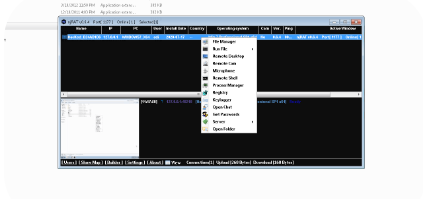
njRAT v0.6.4
njRAT v0.6.4 is a notorious Remote Access Trojan (RAT) that emerged as a significant cybersecurity threat, primarily targeting Windows systems. This malware variant enables attackers to gain complete control over infected machines while evading detection through various obfuscation techniques. While some position it as an administrative tool, its predominant use involves illegal surveillance and data […]
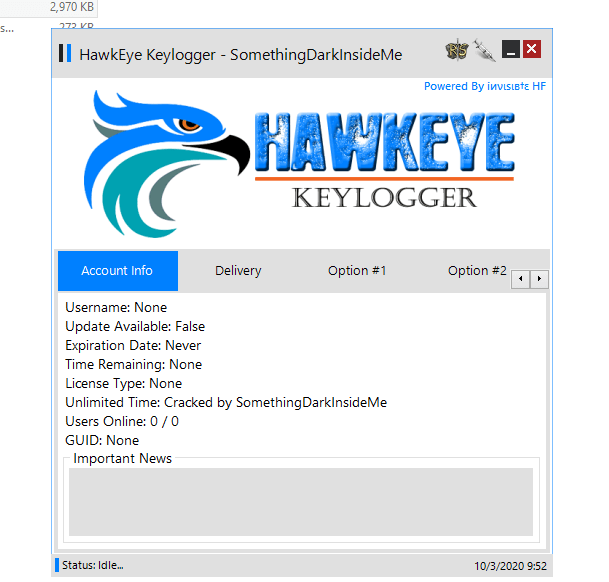
HawkEye Keylogger Cracked 2024
HawkEye Keylogger Cracked 2024 has resurfaced in underground hacking communities as a potent, freely available credential-stealing tool. Originally a commercial keylogger, the cracked version removes license restrictions, making it accessible to less sophisticated hackers while retaining its powerful surveillance capabilities. This Windows-based malware specializes in harvesting sensitive data, including login credentials, financial information, and browsing […]
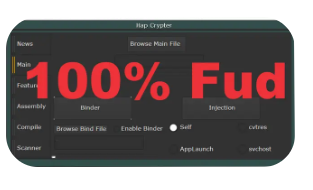
Hap Crypter Cracked 2024
Hap Crypter is a well-known software crypter designed to obfuscate malicious executables, making them undetectable by antivirus programs. The “cracked” 2024 version refers to an illicitly modified release, often distributed in underground forums. While it has legitimate uses in penetration testing, its misuse poses significant cybersecurity threats. This article explores its functionality, risks, and defensive measures. Download Link 1 Download […]
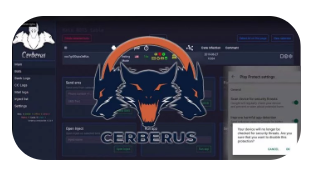
CERBERUS V2 with source
Cerberus V2 with source is a sophisticated Android-based banking Trojan that emerged as an evolution of the original Cerberus malware. Initially sold as a Malware-as-a-Service (MaaS), it gained notoriety for its ability to bypass security measures, steal sensitive financial data, and perform unauthorized transactions. Despite its shutdown in 2020, its techniques remain relevant for cybersecurity professionals studying financial malware […]
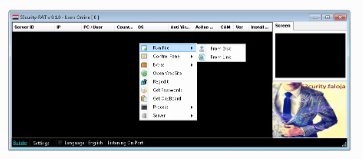
S3curity-RAT v0.1.0
S3curity-RAT v0.1.0 is a Remote Access Trojan (RAT) designed to provide covert control over compromised systems. Marketed as a penetration testing tool, it can be misused for malicious activities such as data theft, surveillance, and system manipulation. While some may claim legitimate uses, unauthorized deployment of such software violates cybersecurity laws and ethical standards. What […]
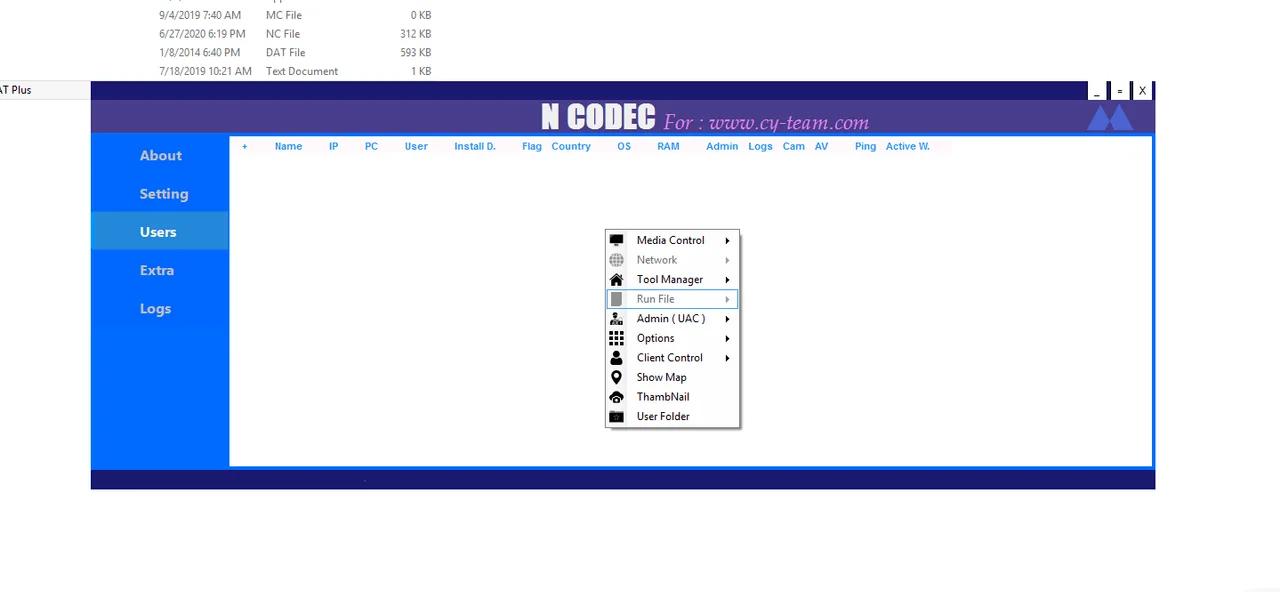
N Codec RAT Plus Premium 2020
N Codec RAT Plus Premium 2020 emerged as a sophisticated, multi-functional Remote Access Trojan (RAT) that gained notoriety in underground cyber communities for its advanced surveillance capabilities and premium-grade features. Marketed as a “professional surveillance solution,” this Windows-based malware combines traditional remote administration functions with cutting-edge evasion techniques, making it particularly effective against targets with […]