Frutas rat english 2024
Frutas RAT English 2024 is an emerging Remote Access Trojan that has gained notoriety for its lightweight design and effective evasion capabilities. Originally developed in Spanish-speaking hacking communities, this English version now poses a global threat with improved functionality. Unlike more complex RATs, Frutas maintains a low profile while providing comprehensive system control, making it particularly dangerous […]
Mega RAT 1.5 Beta
Mega RAT 1.5 Beta is an advanced Remote Access Trojan (RAT) designed to provide hackers with complete, undetected control over compromised systems. This latest version introduces enhanced evasion techniques, expanded surveillance capabilities, and improved command-and-control (C2) communication. Targeting both Windows and Android devices, Mega RAT 1.5 Beta poses a significant threat to personal privacy and enterprise […]
Sauron Locker 2024
Sauron Locker 2024 represents a significant leap in ransomware sophistication, combining advanced encryption methods with stealthy infiltration techniques. This malware variant targets both individual users and enterprise networks, employing a double-extortion model that encrypts files while exfiltrating sensitive data. Its modular design and polymorphic code make it particularly resistant to traditional security measures, posing a […]
Project Neptune v2.0
Project Neptune v2.0 is a sophisticated credential-harvesting malware designed to stealthily collect sensitive login information from compromised systems. Built with modular architecture and advanced evasion techniques, it primarily targets web browsers, email clients, and financial applications. Its ability to bypass security measures while remaining undetected makes it a significant threat in the cybersecurity landscape. What is […]
Atomic Email Verifier 9.41.0.97 – Portable Cracked
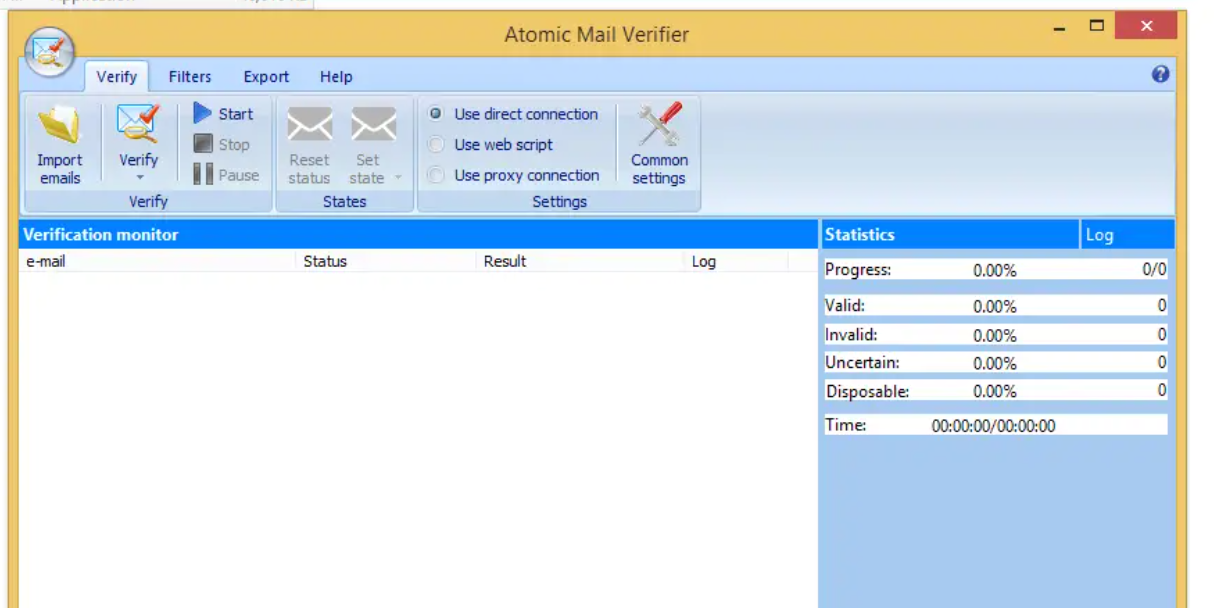
Atomic Email Verifier 9.41.0.97 – Portable Cracked is a powerful software designed to verify email addresses in bulk, ensuring high deliverability and reducing bounce rates. This portable, pre-activated version offers a seamless experience for marketers, businesses, and individuals looking to clean their email lists efficiently. Download Link 1 Download Link 2 Download Link 3 Download […]
LimeStealer 2024
LimeStealer 2024 is a cutting-edge information-stealing malware designed to extract sensitive data from infected systems with high efficiency. Known for its stealthy operation and modular design, it targets browsers, cryptocurrency wallets, gaming credentials, and financial applications. Its evolving evasion techniques make it a significant threat in cybersecurity. Download Link 1 Download Link 2 Download Link […]
Twilight Stealer 2024
Twilight Stealer 2024 is a sophisticated information-stealing malware designed to extract sensitive data from compromised systems. Unlike traditional stealers, it employs advanced evasion techniques, targeting browsers, cryptocurrency wallets, FTP clients, and more. Its modular architecture and regular updates make it a persistent threat in the cybersecurity landscape. What is Twilight Stealer 2024 Twilight Stealer 2024 […]
Denial of Service DDOS Mega Pack 2024
The DDoS Mega Pack 2024 is a powerful and comprehensive toolkit designed for cybersecurity professionals, ethical hackers, and researchers to simulate, analyze, and mitigate Distributed Denial of Service (DDoS) attacks. This advanced suite provides an all-in-one solution for testing network resilience, identifying vulnerabilities, and strengthening defences against one of the most disruptive cyber threats in […]
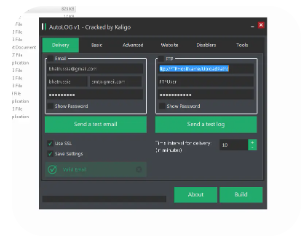
AutoLOG Keylogger 2024
AutoLOG Keylogger 2024 represents the latest evolution in stealthy keystroke monitoring tools, combining traditional logging functions with advanced evasion techniques. This sophisticated keylogger demonstrates concerning capabilities for capturing sensitive user input while avoiding standard detection methods. Cybersecurity professionals study AutoLOG to develop stronger defensive measures against unauthorized surveillance and credential theft. What is AutoLOG Keylogger? AutoLOG […]
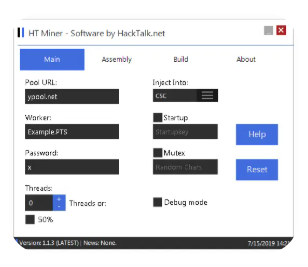
hMinerPTS Bitcoin Miner 2024
hMinerPTS is a sophisticated cryptojacking malware that surfaced in 2024, targeting Windows and Linux systems to mine Bitcoin without user consent. This stealthy miner utilizes advanced evasion techniques to avoid detection while maximizing computational power for illicit cryptocurrency mining. Cybersecurity researchers analyze hMinerPTS to develop better detection methods and protect systems from unauthorized resource hijacking. Download […]