uProxy Tool v1.81 proxy grabber and checker
uProxy Tool v1.81 is an advanced software solution for automated proxy harvesting and validation. Combining proxy scraping, real-time checking, and performance analysis, it is ideal for cybersecurity experts, web scrapers, and privacy-focused users. With powerful algorithms and an intuitive interface, uProxy Tool v1.81 simplifies building reliable proxy lists for legitimate uses. Download Link 1 Download […]
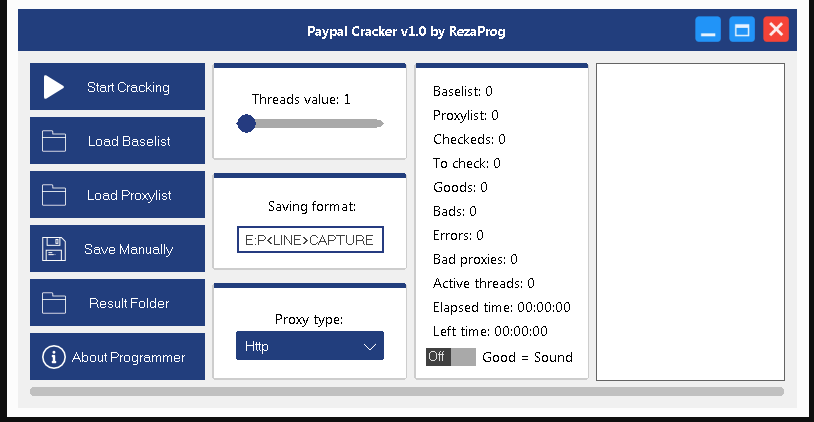
PayPal Cracker v1.0
PayPal Cracker v1.0 is a highly controversial and illegal software program marketed on underground forums. It claims to exploit vulnerabilities in PayPal accounts to gain unauthorized access, often through brute force and phishing tactics. Despite the bold claims made by its promoters, using this tool is illegal, unethical, and exposes users to serious legal, security, […]
Red Proxy Checker 2024
Red Proxy Checker 2024 is a high-performance proxy testing solution designed for cybersecurity experts, network admins, and ethical hackers. It verifies proxy functionality, anonymity, speed, and geolocation to ensure secure browsing, effective data scraping, and reliable penetration testing. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What Is Red Proxy Checker […]
Proxy Checker v0.2 by X-SLAYER
Proxy Checker v0.2 by X-SLAYER is a lightweight and powerful software designed to verify proxy servers’ functionality, anonymity level, and performance. Widely used by cybersecurity experts, ethical hackers, and network administrators, it ensures secure and reliable proxy connections for privacy, penetration testing, and automated tasks like web scraping. Download Link 1 Download Link 2 Download […]
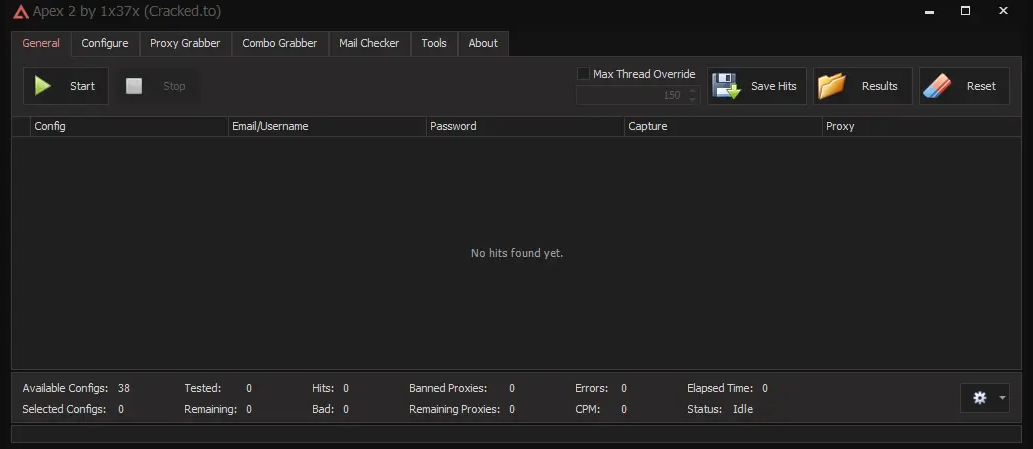
Apex 2: The All-In-One Checker 2024
In the modern digital era, verifying data quickly and accurately is essential to security, marketing, and system integrity. Apex 2: The All-In-One Checker 2024 is a powerful, unified platform designed to validate critical information—emails, phone numbers, proxies, passwords, and more—with precision and ease. Ideal for IT professionals, digital marketers, and data analysts, Apex 2 helps […]
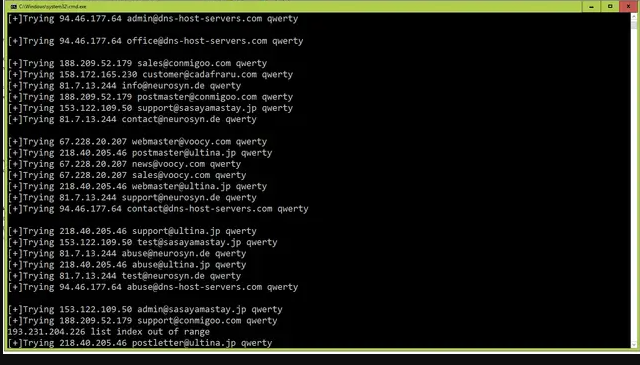
SBR SMTP Scanner 2024
In a time when reliable email delivery and server security are crucial to business communication, SBR SMTP Scanner 2024 offers a sophisticated solution for analyzing and optimizing SMTP servers. Designed for IT professionals, system administrators, and cybersecurity teams, this tool helps ensure your email infrastructure is fast, secure, and compliant. Download Link 1 Download Link […]
vProxy v1.4
In today’s cyber-focused world, privacy and secure communication are more important than ever. vProxy v1.4 is a lightweight yet powerful proxy tool designed for ethical hackers, penetration testers, security researchers, and privacy-conscious users. It allows you to hide your IP, manipulate traffic, and test networks without being detected. Download Link 1 Download Link 2 Download […]
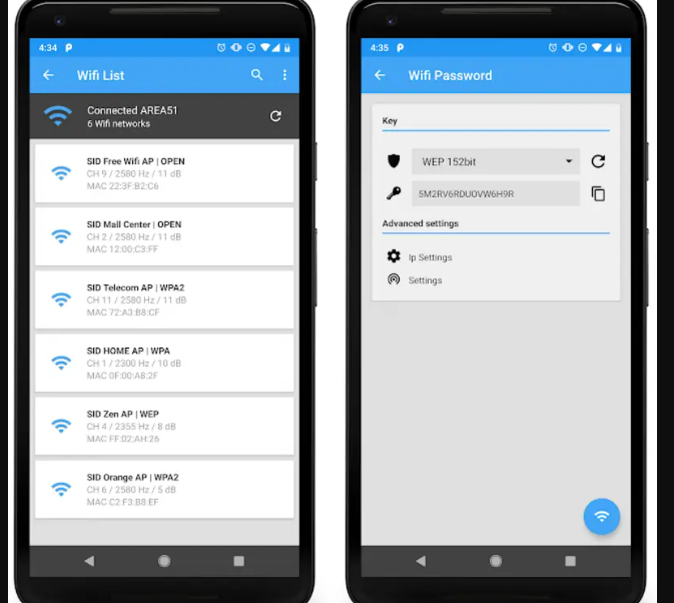
WIFI PASSWORD PRO v5.6.0 (Unlocked)
In today’s hyper-connected world, having quick and secure access to WiFi networks is essential. WIFI PASSWORD PRO v5.6.0 (Unlocked) is a powerful Android application that enables users to retrieve, manage, and share saved WiFi passwords with ease. Whether you’re troubleshooting, switching networks, or managing multiple devices, this app simplifies WiFi access while ensuring security and […]
IP and Port Scanners 2024
In an increasingly interconnected and threat-prone digital landscape, IP and Port Scanners 2024 play a vital role in cybersecurity, IT operations, and infrastructure monitoring. The 2024 generation of these tools delivers fast, intelligent, and automated scanning capabilities to help administrators identify devices, open ports, and hidden vulnerabilities across networks—before attackers do. What Is an IP […]
Learning Tor and the Dark Web 2024
The Dark Web and the Tor network continue to play vital roles in cybersecurity, digital privacy, and ethical hacking. Often misunderstood, the Dark Web isn’t solely a hub for illegal activity—it also serves as a critical tool for whistleblowers, journalists, and privacy-focused users. Learning how Tor works and how to explore the Dark Web responsibly […]