IP Domain SMTP Scanner And Cracker 2024
Email servers remain one of the most popular attack surfaces for threat actors. IP Domain SMTP Scanner & Cracker 2024 gives penetration testers, network administrators, and red‑teamers a single platform to uncover—and help remediate—SMTP weaknesses before they are exploited. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What is IP Domain SMTP Scanner & Cracker 2024? This all‑in‑one utility scans SMTP endpoints, validates configurations, and […]
Certified Ethical Hacker v10 PDFs Books
The Certified Ethical Hacker (CEH) v10 certification remains one of the most respected credentials in the field of cybersecurity. Although CEH v12 is now the latest version, CEH v10 books and PDFs continue to be highly useful for learning penetration testing, ethical hacking, and defensive strategies. This guide explores why CEH v10 study materials are […]
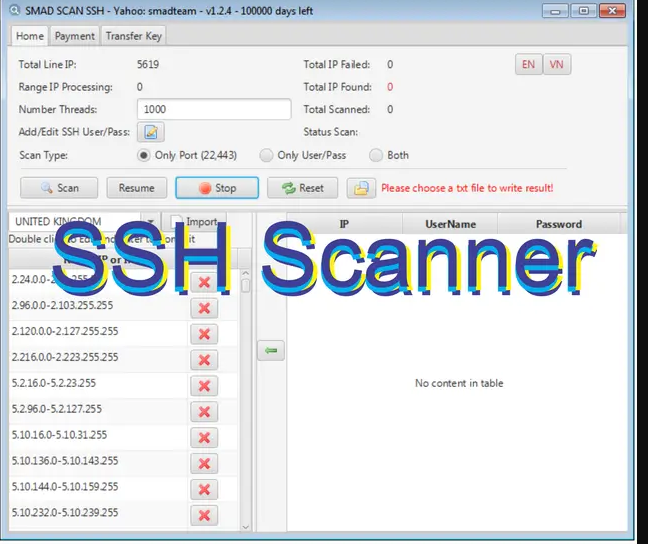
Smad SSH Scanner 2024
As cyber threats continue to target critical infrastructure, Smad SSH Scanner 2024 stands out as a vital solution for IT security teams. Designed to secure SSH (Secure Shell) services across networks of all sizes, this advanced tool identifies vulnerabilities, simulates attacks, and delivers actionable insights to protect against unauthorized access. Download Link 1 Download Link […]
Hacking Android 2024
With over 3 billion active devices, Android remains the most widely used mobile operating system—and consequently, a top target for cyberattacks. Ethical Android hacking plays a vital role in defending against these threats by identifying vulnerabilities, securing applications, and testing system defenses. Whether you’re a penetration tester, security researcher, or cybersecurity student, mastering Android hacking […]
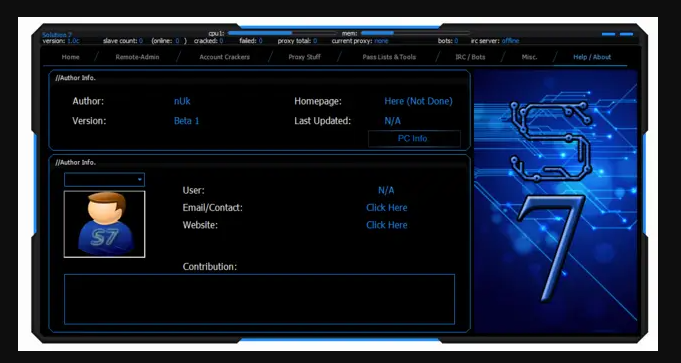
Solution 7
In today’s digital-first world, businesses need intelligent solutions that streamline operations, enhance productivity, and support sustainable growth. Solution 7 is an all-in-one business management platform engineered to meet the demands of modern enterprises. Whether you’re a startup or a large organization, Solution 7 empowers teams to automate tasks, collaborate seamlessly, and make data-driven decisions. What […]
Crypters and Binders Pack 2024
Crypters and Binders Pack 2024 is a powerful toolkit designed for developers, security researchers, and ethical hackers to securely encrypt, bind, and deliver executable files while maintaining confidentiality and functionality. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What Is Crypters and Binders Pack 2024? Crypters and Binders Pack is a […]
SSH Root Scanner 2024
In today’s fast-paced cybersecurity landscape, SSH Root Scanner 2024 stands out as a critical tool for identifying vulnerabilities in SSH (Secure Shell) servers. Designed for system administrators, ethical hackers, and security professionals, this powerful scanner uncovers weak configurations, root login risks, and brute-force attack vectors—ensuring your infrastructure remains protected from unauthorized access. What is SSH […]
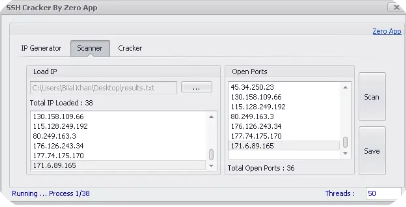
SSH IP Generator, Port Scanne,r RDP Cracker 2024
SSH IP Generator Port Scanner RDP Cracker 2024 is a versatile, all-in-one cybersecurity tool designed for penetration testers, ethical hackers, and network administrators. It combines IP generation, port scanning, and credential cracking to help identify vulnerabilities and strengthen network defenses effectively. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What Is […]
FTP Scanner 2024
In today’s digital age, ensuring secure and reliable file transfers is critical for both organizations and individuals. FTP Scanner 2024 is a next-generation tool designed to secure, scan, and monitor FTP (File Transfer Protocol) servers with precision. Ideal for system administrators, developers, and cybersecurity professionals, this tool offers comprehensive features to safeguard file transfers and […]
Zeroday Link exploit 2024
Zero-Day Link Exploit 2024 is a recently discovered cybersecurity vulnerability that enables attackers to execute malicious code or gain unauthorized access through unpatched software flaws. This exploit poses a critical threat due to its ability to bypass conventional security defenses, putting organizations and individuals worldwide at risk. Download Link 1 Download Link 2 Download Link […]