Cooked Grabber 2024
Cooked Grabber 2024 is a sophisticated information-stealing malware designed to extract sensitive data from compromised systems. Often distributed through phishing attacks or malicious downloads, it targets credentials, cookies, cryptocurrency wallets, and other valuable information. Cybersecurity experts categorize it as a significant threat due to its stealthy operation and advanced evasion techniques. Download Link 1 Download […]
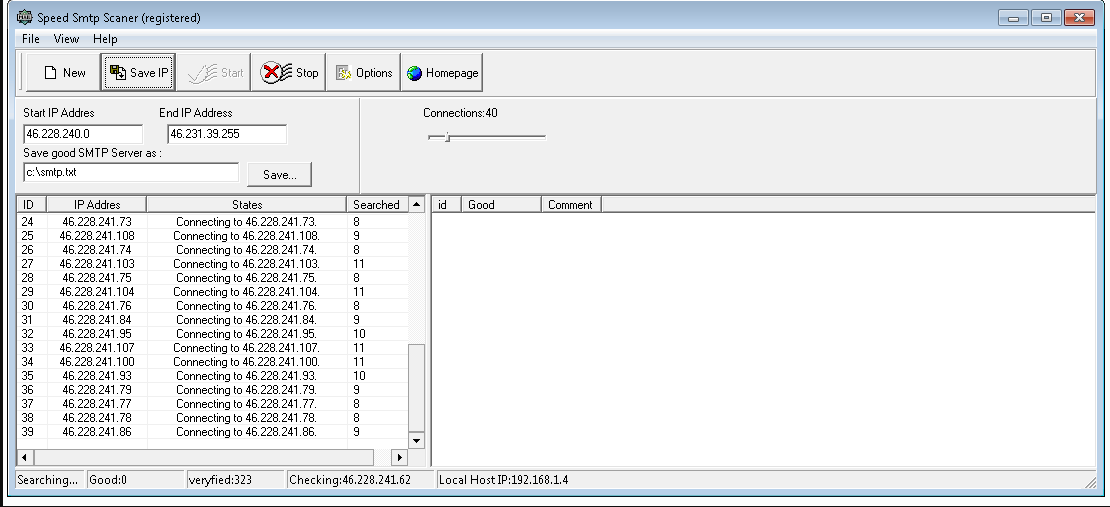
Speed SMTP Scanner v2.5 Registered
Speed SMTP Scanner v2.5 Registered is a professional-grade utility built for IT experts, network administrators, and cybersecurity professionals. Designed to scan and validate SMTP (Simple Mail Transfer Protocol) servers, it offers fast, accurate, and bulk email verification to ensure secure and optimized email communications. With advanced features and a clean interface, it’s ideal for server […]
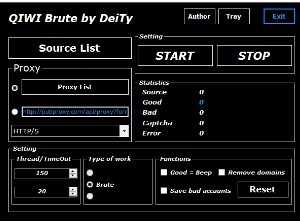
QIWI Brute 2024
QIWI Brute 2024 is a specialized cybersecurity tool designed for penetration testers and ethical hackers to assess the strength of QIWI wallet security. It simulates brute-force attacks to identify weak credentials and vulnerabilities in payment systems. This tool is intended solely for authorized security research and must never be used for illegal activities. Download Link […]
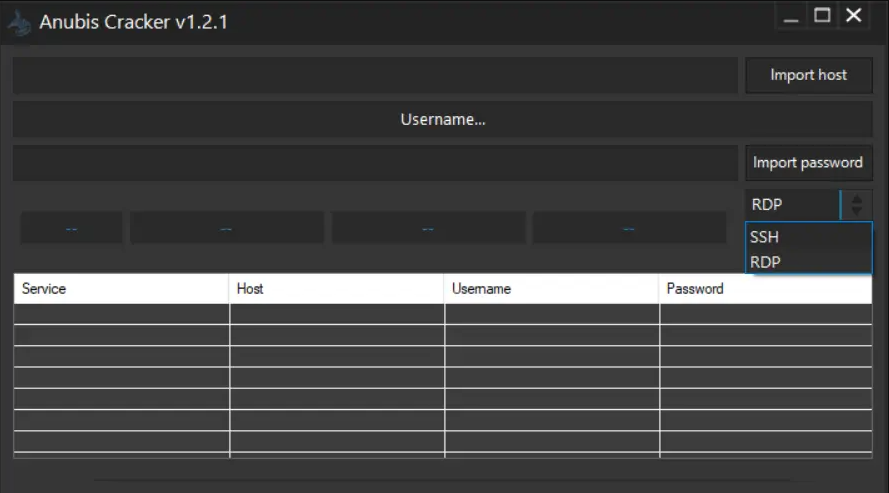
ANUBIS CRACKER V.1.2.1 – SSH/RDP Brute-Force Testing Too
ANUBIS CRACKER V.1.2.1 is a high-performance brute-force tool designed to test the strength of SSH (Secure Shell) and RDP (Remote Desktop Protocol) login credentials. Built for cybersecurity professionals and ethical hackers, it automates the credential guessing process to expose weak authentication and enhance overall network security. Download Link 1 Download Link 2 Download Link 3 […]
Silent Doc Exploit 2024
Silent Doc Exploit 2024 is a sophisticated and stealthy exploitation framework designed to leverage document-based attack vectors for penetration testing and red teaming. Unlike traditional exploits, it operates covertly by embedding malicious payloads within seemingly harmless documents (e.g., PDFs, Word, Excel), making it a potent tool for advanced security assessments. Download Link 1 Download Link […]
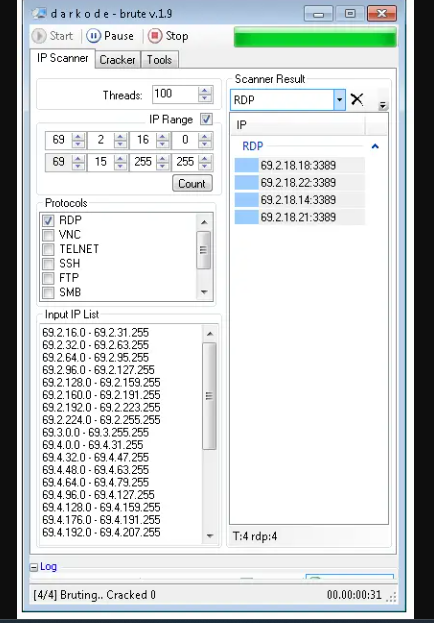
DK Brute 1.9 + Keygen (Network Scanner & Password Cracker)
DK Brute 1.9 + Keygen is a robust cybersecurity tool designed for ethical hacking, network scanning, and password auditing. With powerful scanning features and brute-force capabilities, it helps professionals identify security vulnerabilities and weak credentials in various network environments. Download Link 1 Download Link 2 Download Link 3 Download Link 4 What is DK Brute […]
Exploit Pack 2024
Exploit Pack 2024 is a state-of-the-art cybersecurity tool tailored for penetration testers, ethical hackers, and security researchers. It offers a comprehensive suite of exploits, payloads, and vulnerability assessment modules to help identify and address security risks in modern systems. With an intuitive interface and advanced automation, Exploit Pack streamlines security testing while adhering to ethical […]
Multi Exploit Builder V1
Multi Exploit Builder V1 is a powerful and flexible tool designed for cybersecurity professionals, ethical hackers, and penetration testers. It streamlines exploit creation and deployment, enabling efficient identification and mitigation of vulnerabilities. With an intuitive interface and advanced features, it is essential for modern cybersecurity tasks. Detailed Features of Multi Exploit Builder Feature Description Multi-Platform […]
Doc Exploit FUD 2024 with Tutorial
In the fast-changing cybersecurity landscape, attackers continually develop advanced tools to evade detection. Doc Exploit FUD 2024 is one such tool—a fully undetectable (FUD) payload generator targeting Microsoft Word documents. This overview explains its functionality, key features, use cases, and includes an educational guide. What Is Doc Exploit FUD 2024? Doc Exploit FUD 2024 is […]
Link Exploit 2024
In the constantly evolving digital landscape, effective link management is vital for cybersecurity professionals, ethical hackers, and IT specialists. Link Exploit 2024 stands out as an advanced tool designed to analyze, manipulate, and secure URLs with high accuracy. Ideal for penetration testing, vulnerability assessments, and red team operations, this tool offers a comprehensive framework for […]