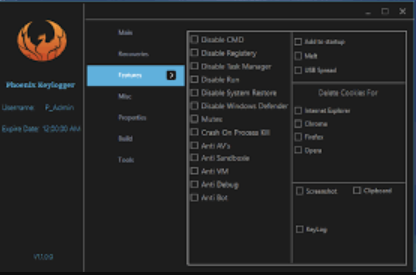
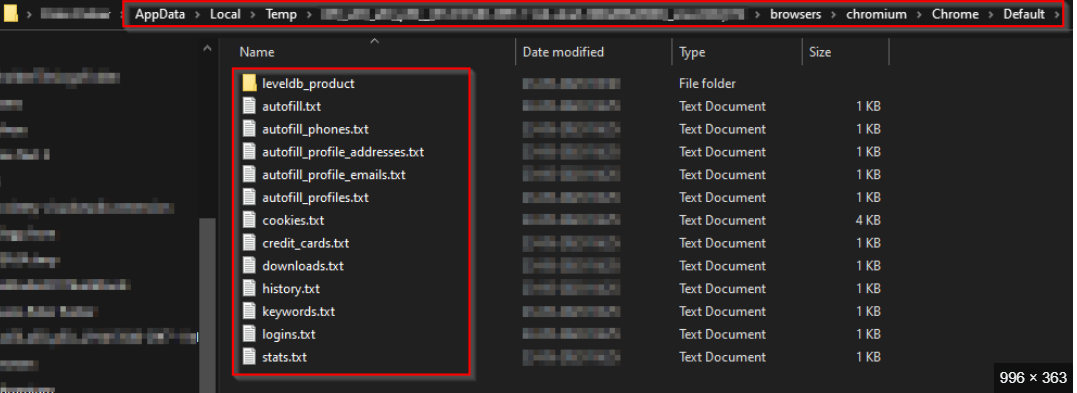
Phoenix Keylogger 2025
Phoenix Keylogger 2025 has emerged as one of the most advanced and stealthy keylogging tools in the cybercriminal arsenal, representing a significant leap in credential theft and surveillance capabilities. This latest iteration of the notorious malware has been observed in high-profile attacks against corporate networks, financial institutions, and individual users, demonstrating alarming improvements in evasion […]
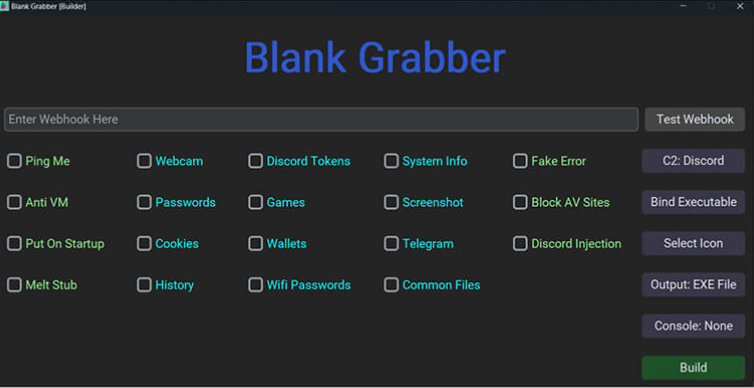
Blank Grabber 2025
Cyber threats continue to evolve, with attackers leveraging increasingly sophisticated tools to exploit vulnerabilities. One such tool, often referred to as “Blank Grabber 2025,” has gained notoriety for its ability to harvest sensitive data from compromised systems stealthily. This malware exemplifies the growing trend of credential theft and information-gathering attacks, which are often used as […]
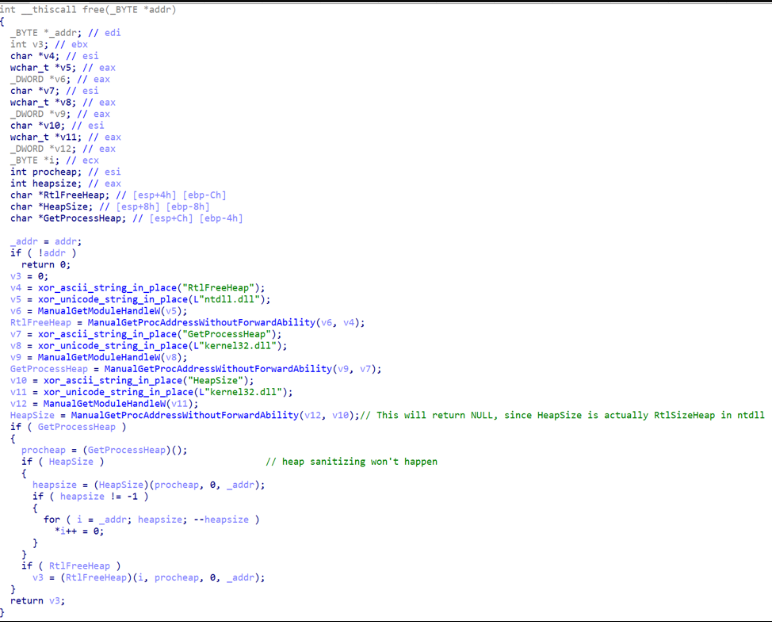
Parasite HTTP Botnet with All Plugins 2025
Modern cyberattacks increasingly rely on sophisticated botnets that leverage legitimate web protocols to blend into normal network traffic. The Parasite HTTP Botnet with All Plugins 2025 represents a dangerous evolution in this space, combining the stealth of HTTP-based communication with modular attack capabilities. Unlike traditional botnets that use easily detectable IRC or custom protocols, this […]
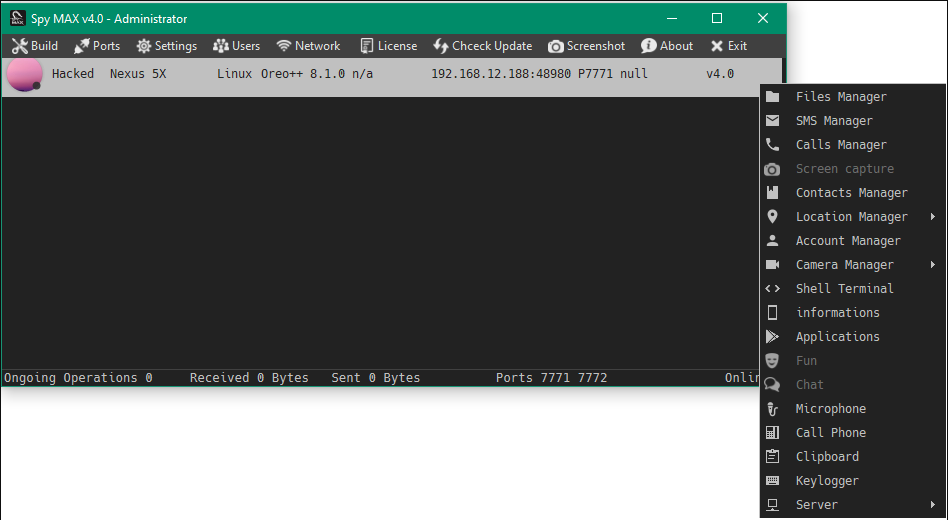
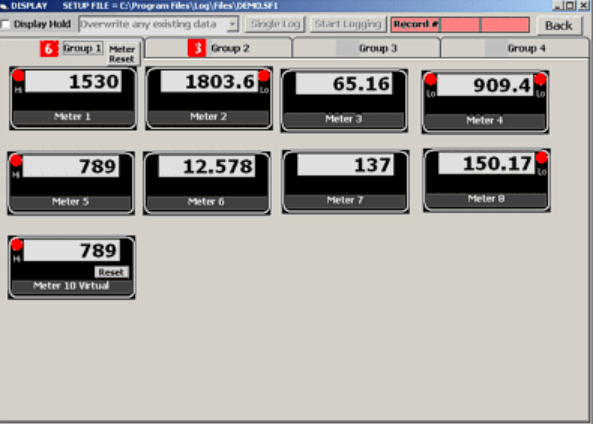
Spy max v2.0
In an era where digital surveillance and data theft have become increasingly sophisticated, tools like Spy Max v2.0 have emerged as potent threats in the cybercrime arsenal. This advanced spyware represents a significant evolution in surveillance malware, combining traditional monitoring capabilities with modern evasion techniques. Unlike basic keyloggers or simple data stealers, this software offers […]
Aurora Stealer 2025 Cracked
Cyber threats continue to evolve, with malicious tools playing a significant role in modern attacks. Among these, information-stealing malware has become a favored tool for cybercriminals, enabling them to harvest sensitive data, including credentials, financial information, and system details. Cracked or illicitly distributed versions of such tools further lower the barrier to entry, allowing even […]
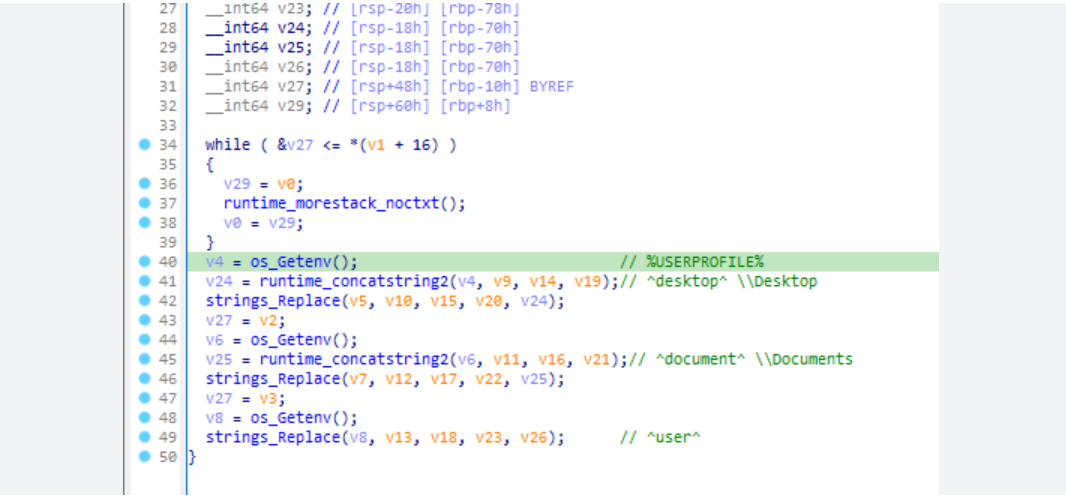
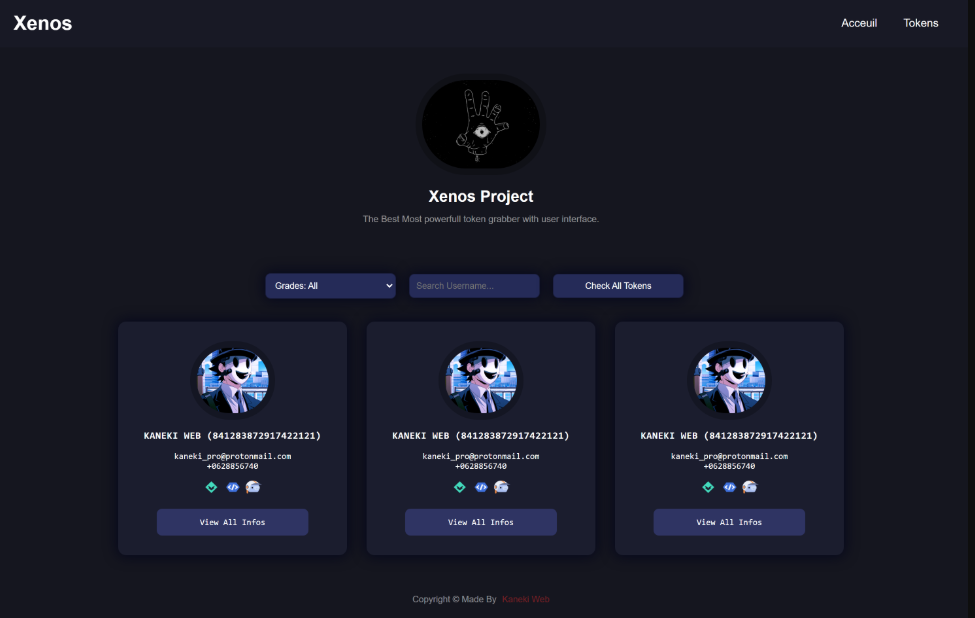
Xenos Grabber 2025
Information stealers have become one of the most pervasive threats in the cybercrime landscape, with attackers constantly developing more sophisticated tools to harvest sensitive data. The Xenos Grabber 2025 represents a new generation of malware designed to silently collect and exfiltrate valuable information from compromised systems. Unlike traditional stealers that focus on a single data […]
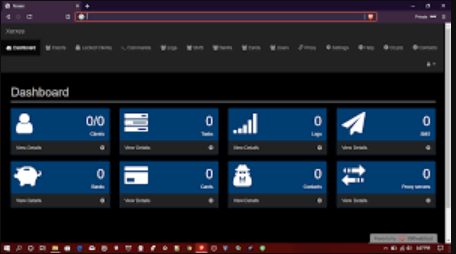
Xerxes Android Botnet 2025
XERXES Android Botnet 2025 has emerged as one of the most sophisticated mobile botnets currently threatening the cybersecurity landscape, representing a significant evolution in Android-focused malware capabilities. This advanced threat has been actively deployed in global campaigns targeting both individual users and enterprise mobile devices, demonstrating alarming flexibility in its attack vectors and command structure. […]
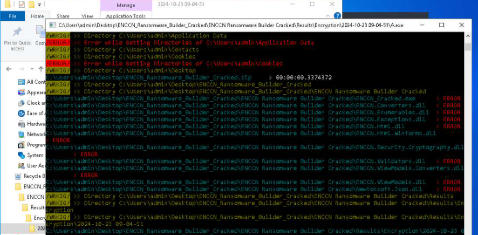
ENCCN RANSOMWARE 2025 cracked
Ransomware continues to be one of the most destructive forms of malware, with attackers constantly refining their techniques to maximize profits and evade detection. The ENCCN Ransomware 2025 cracked variant represents the latest evolution in this threat landscape, combining advanced encryption methods with sophisticated evasion tactics. Unlike earlier ransomware strains that were often detectable by […]
Invicta Stealer 2025
Cyber threats continue to evolve, with information-stealing malware playing a significant role in modern attacks. One such example is a powerful stealer that emerged in 2025, capable of extracting sensitive data from infected systems with alarming efficiency. Invicta Stealer 2025 stealers are often distributed through phishing campaigns, malicious downloads, or exploit kits, enabling attackers to […]
LO$R Logger v2
Cyberattacks have evolved significantly, leveraging advanced tools to exploit vulnerabilities and steal sensitive data. One such tool, often referred to as “LO$R Logger v2,” has gained notoriety for its effectiveness in credential theft and surveillance. This malware variant is commonly distributed through phishing campaigns, malicious downloads, or exploit kits, targeting both individuals and organizations. Once […]