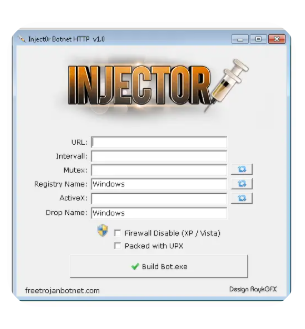
Inject0r Bot HTTP 2024
Inject0r Bot HTTP 2024 is an advanced web injection and credential harvesting botnet designed to manipulate browser sessions, steal sensitive data, and automate financial fraud. This malware leverages man-in-the-browser (MITB) attacks, real-time HTML manipulation, and encrypted C2 communication to bypass security measures. With its modular architecture and adaptive evasion techniques, Inject0r Bot poses a severe threat to online […]
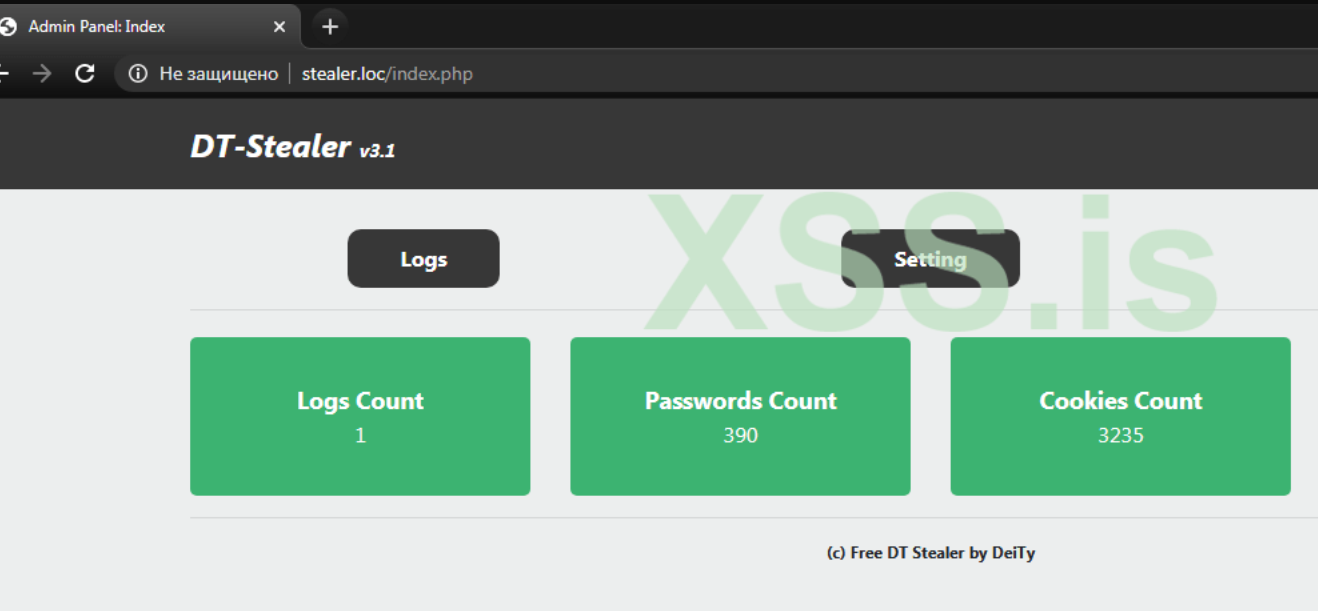
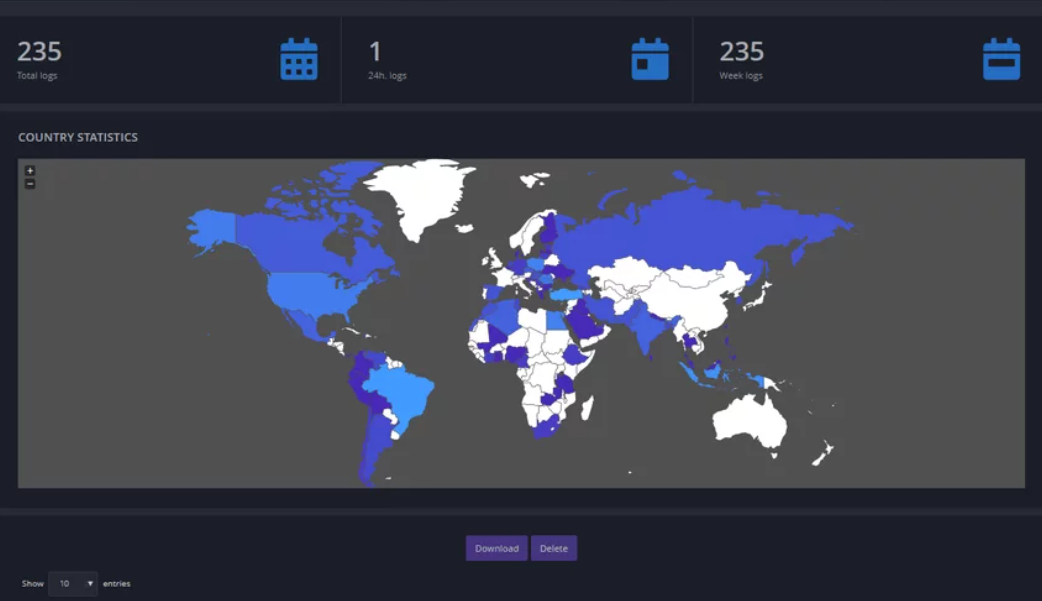
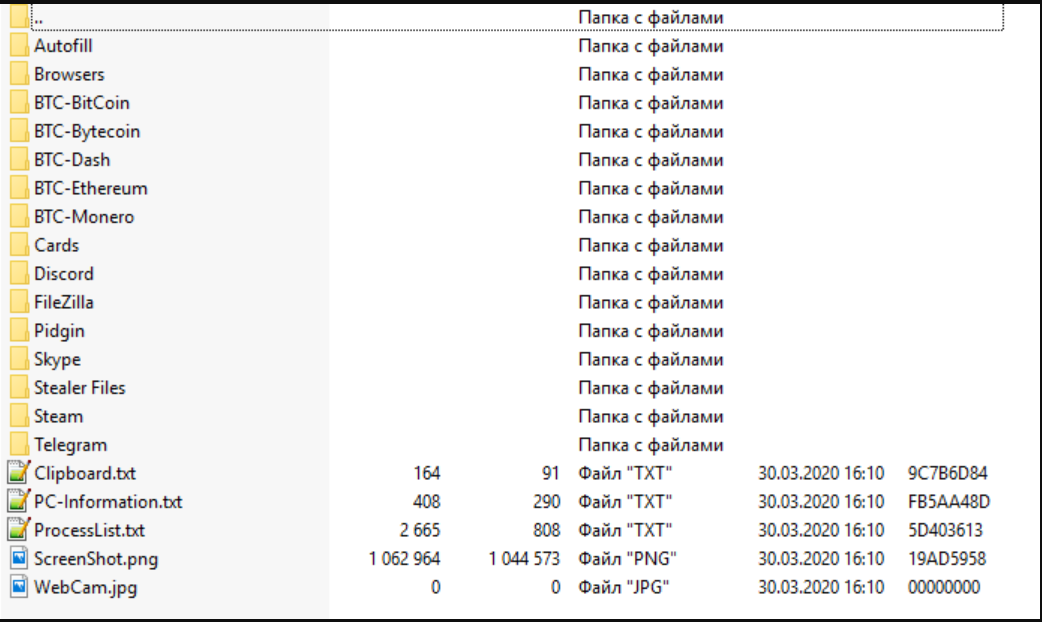
DT Stealer V1.3 with Source
DT Stealer V1.3 is a powerful information-stealing malware designed to extract sensitive data from compromised systems. With its open-source availability, it has gained attention among cybersecurity researchers and threat actors alike. This article delves into its functionality, features, and the risks it poses. Download Link 1 Download Link 2 Download Link 3 What is DT […]
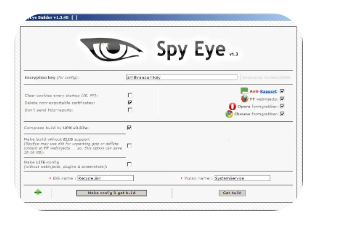
SpyEye Botnet 2024
SpyEye Botnet 2024 marks the alarming resurgence of one of history’s most notorious banking trojans, now upgraded with modern evasion tactics and expanded targeting capabilities. This reengineered malware combines sophisticated web injection frameworks with advanced persistence mechanisms, specializing in financial data theft from both consumer and corporate banking platforms. Its modular architecture allows for real-time […]
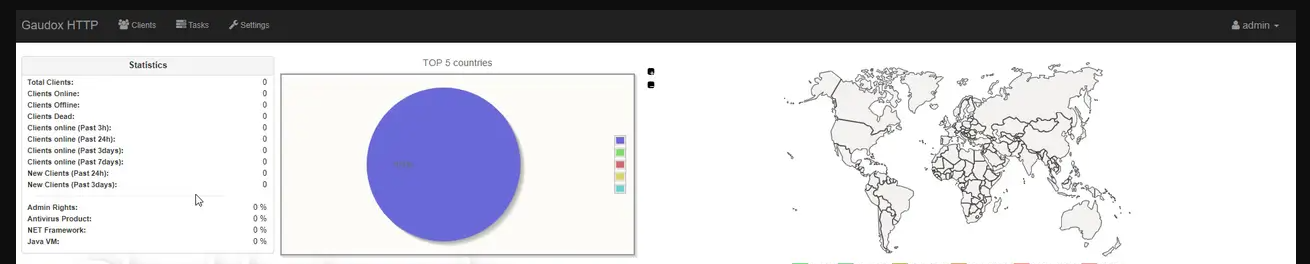
Gaudox Botnet v1.1.0.1
Gaudox Botnet v1.1.0.1 is a sophisticated modular botnet framework designed for large-scale cyber operations, including DDoS attacks, credential harvesting, and cryptocurrency mining. This updated version introduces enhanced encryption, improved command-and-control (C2) resilience, and plugin-based functionality, allowing hackers to deploy customized attack modules on infected machines. Its multi-platform compatibility (Windows, Linux) and stealthy propagation make it a significant […]
Nexus Stealr cracked 2024
Nexus Stealr Cracked 2024 is a highly controversial software tool that has gained notoriety in underground circles for its ability to extract sensitive data from various platforms. While its cracked version offers unauthorized access to premium features, its use raises significant ethical and legal concerns. This article delves into what Nexus Stealr is, its features, […]
Poulight Stealer cracked
Poulight Stealer is a potent information-stealing malware designed to extract sensitive data from infected systems. The cracked version, widely circulated in underground forums, provides unauthorized access to its premium features without payment. While its use is illegal and poses significant cybersecurity risks, understanding its capabilities is essential for defense and awareness. Download Link 1 Download […]
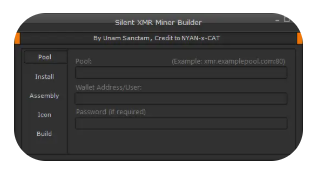
Silent XMR Miner Builder v0.2+Tutorial
Silent XMR Miner Builder v0.2 is a powerful cryptocurrency miner generator designed to create undetectable Monero (XMR) mining payloads. This tool enables hackers to covertly hijack system resources for profit, using advanced evasion techniques to avoid detection by antivirus and endpoint protection. The included tutorial simplifies deployment, making cryptojacking accessible even to less experienced threat actors. With […]
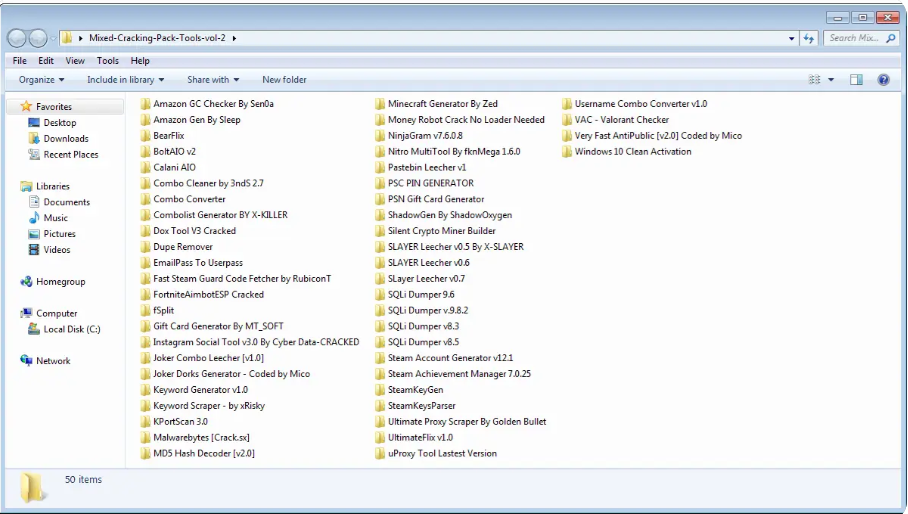
Cracking Tools Mega Pack 2025
The Cracking Tools Mega Pack 2025 is a comprehensive collection of advanced cybersecurity tools designed for penetration testers, ethical hackers, and security researchers. This all-in-one toolkit provides cutting-edge solutions for vulnerability assessment, password cracking, network analysis, and exploit development, making it an indispensable resource for cybersecurity professionals. Download Link 1 Download Link 2 Download Link […]
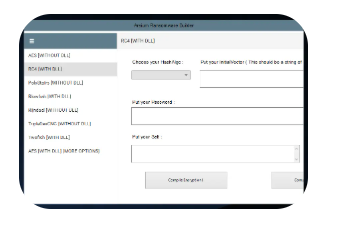
Arsium Ransomware Builder 2024
Arsium Ransomware Builder 2024 represents a dangerous evolution in ransomware development tools, enabling even novice hackers to create customized ransomware strains with minimal technical knowledge. This point-and-click software package generates fully functional ransomware executables with sophisticated encryption, evasion techniques, and built-in cryptocurrency payment systems. The 2024 version introduces polymorphic code generation, expanded target selection options, […]
Predator Pain Keylogger v13
Predator Pain Keylogger v13 represents the latest evolution in stealthy surveillance malware, combining traditional keylogging with modern data exfiltration techniques. This sophisticated tool captures every keystroke, screen activity, and system interaction while remaining virtually undetectable by most security solutions. Its 2024 update introduces enhanced anti-analysis capabilities, expanded browser targeting, and improved persistence mechanisms, making it […]