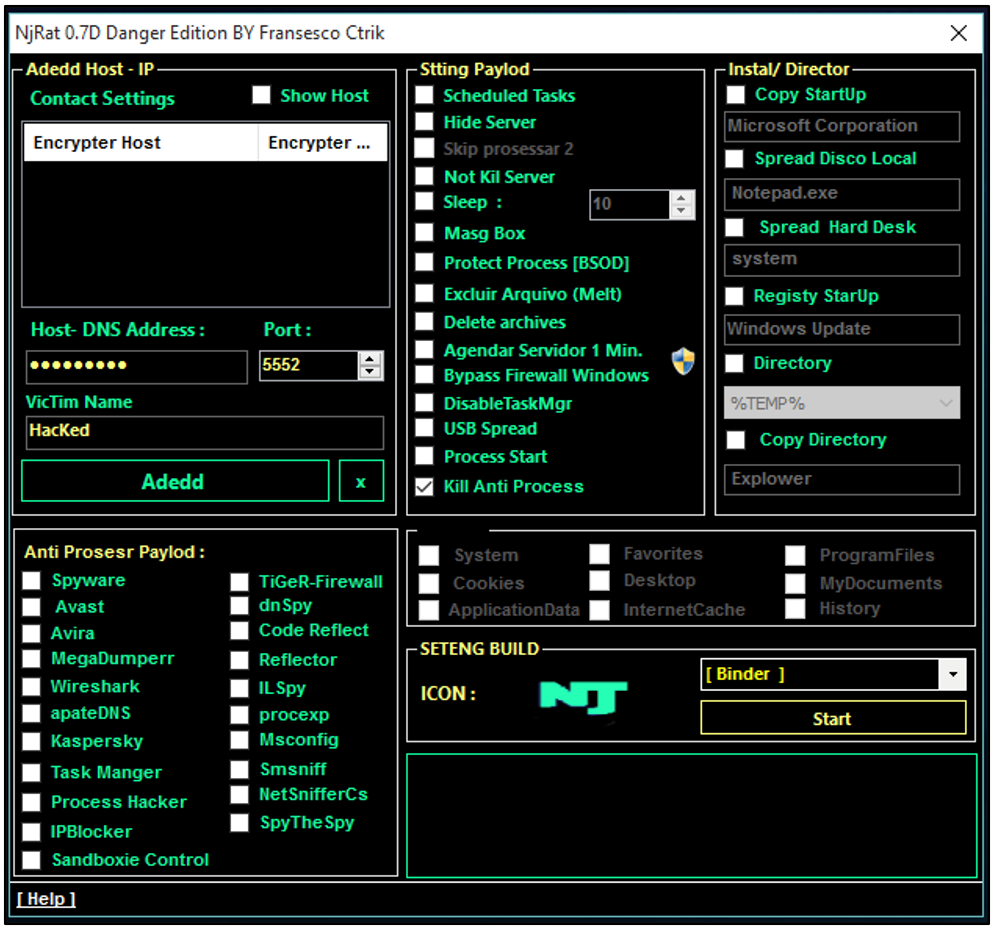
njRAT v0.8.0 LIME EDITION
The cyber threat landscape continues to evolve with the resurgence of modified legacy Remote Access Trojans (RATs) that have been enhanced with modern capabilities. Among these, a particularly concerning variant has emerged, combining the proven effectiveness of traditional RAT functionality with contemporary evasion techniques. njRAT v0.8.0 exemplifies how threat actors are revitalizing older codebases with […]
Sseur Keylogger 2025 Cracked
Keyloggers continue to pose a persistent threat in cybersecurity, frequently used to steal sensitive information, including login credentials, financial data, and personal communications. Cracked or pirated versions of keylogging software, usually distributed through underground forums, amplify this risk by making powerful surveillance tools accessible to malicious actors. Sseur Keylogger 2025 tools are frequently deployed in […]
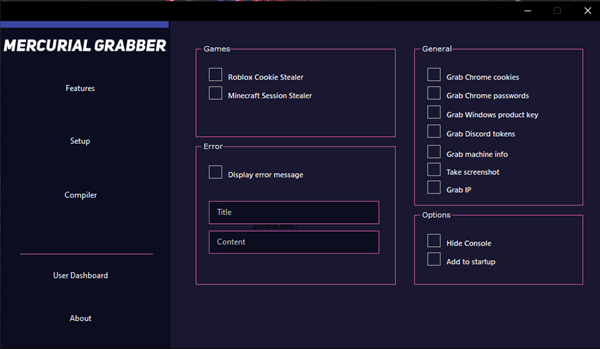
Mercurial Grabber 2025
The cybersecurity landscape in 2025 has witnessed the emergence of highly sophisticated credential-stealing malware designed to bypass modern security measures with unprecedented efficiency. Among these threats, a particularly agile and evasive strain has gained prominence for its ability to rapidly adapt to different environments and extract sensitive authentication data. Mercurial Grabber 2025 exemplifies the growing […]
AB Stealer 2025 Cracked
The cybersecurity landscape faces an escalating threat from sophisticated information stealers, with Ab Stealer 2025 Cracked emerging as one of the most dangerous tools in modern credential harvesting campaigns. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful attack tools at minimal cost. Ab Stealer 2025 Cracked […]
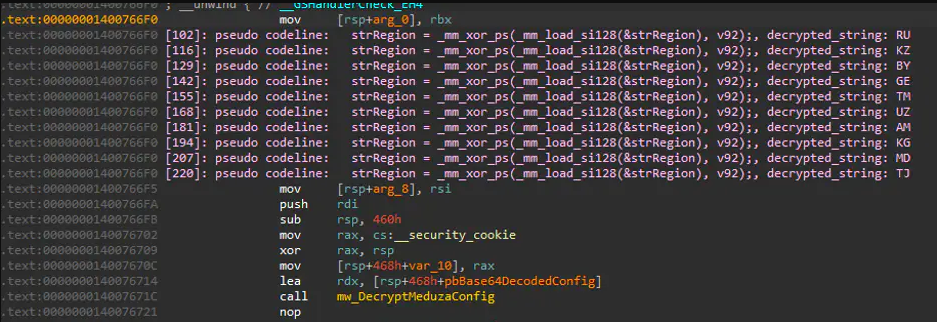
COSMO STEALER 2025
The evolution of information stealers has reached new heights in 2025, with modern variants demonstrating unprecedented sophistication in data harvesting and evasion techniques. Among these threats, a particularly advanced strain has emerged as a favorite of cybercriminals due to its modular design, broad targeting capabilities, and robust anti-detection mechanisms. COSMO STEALER 2025 exemplifies the current […]
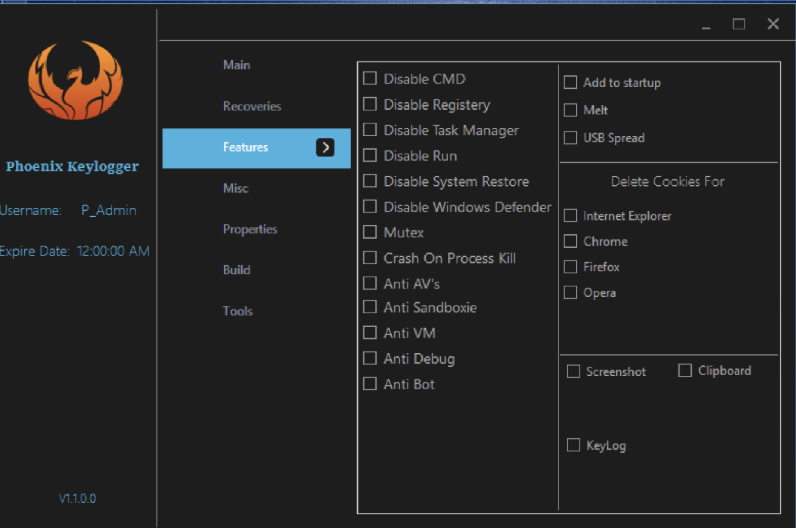
Poenix Keylogger 2025 Cracked
Cyberattacks have evolved significantly in recent years, with keyloggers remaining a persistent threat due to their ability to capture sensitive user data stealthily. Among these, cracked versions of keylogging software—often distributed illegally—pose an even greater risk, as they bypass security measures and licensing restrictions, making them attractive tools for malicious actors. Poenix Keylogger 2025 tools […]
Shinobu Clipper 2025
Cryptocurrency-focused malware has become increasingly prevalent in the cybercrime ecosystem, with clipboard hijackers emerging as one of the most effective tools for stealing digital assets. These specialized malware strains operate by silently monitoring and modifying clipboard contents, allowing attackers to divert cryptocurrency transactions to their wallets. The 2025 iteration of these clippers demonstrates enhanced sophistication, […]
Man Clipper 2025 Cracked
The cryptocurrency ecosystem faces a growing threat from sophisticated clipboard hijacking malware, with Man Clipper 2025 Cracked emerging as one of the most dangerous tools for intercepting digital currency transactions. This advanced malware variant demonstrates how cybercriminals are refining their techniques to target cryptocurrency users with surgical precision. Man Clipper 2025 Cracked has been actively […]
Hack Pack 2025
The cybersecurity threat landscape has seen a surge in all-in-one attack toolkits that bundle multiple malicious capabilities into a single package. These comprehensive suites lower the barrier to entry for cybercriminals by providing ready-made tools for various attack vectors. Particularly concerning is their modular design, which allows even novice attackers to launch sophisticated campaigns with […]
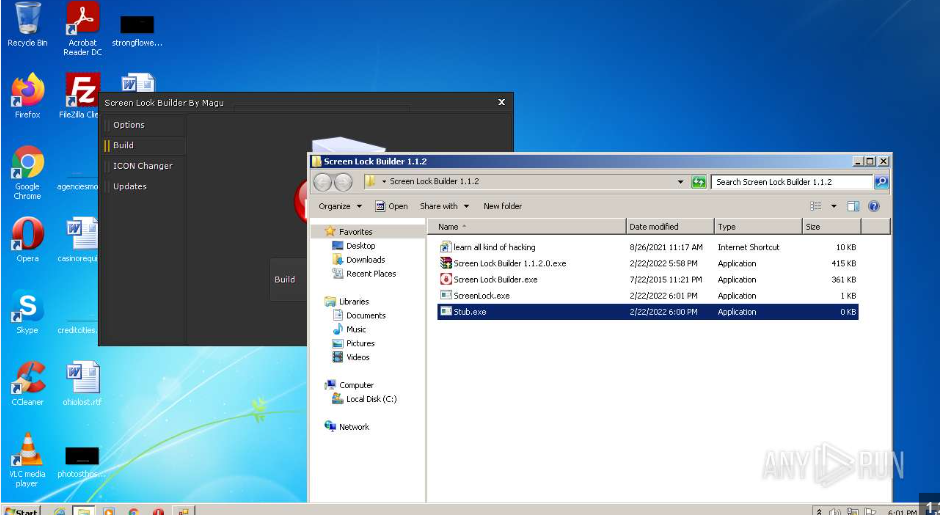
Screen Lock Builder 1.1.2.0
In recent years, cybercriminals have increasingly turned to specialized tools to enhance the effectiveness of their attacks. One such tool, often distributed through malicious campaigns, is designed to lock users out of their systems while demanding payment for restoration. Screen Lock Builder attacks, commonly categorized as ransomware or screen locker threats, disrupt productivity and extort […]