Prosto Clipper 2024
Cybercriminals are constantly refining their tools to exploit financial transactions, and one such threat, often referred to as Prosto Clipper 2024, has become a significant concern in modern cyberattacks. This malware specializes in intercepting and altering cryptocurrency transactions by silently modifying clipboard contents, redirecting funds to attacker-controlled wallets. Unlike ransomware or traditional stealers, this type of […]
VENOM RAT 5.0.4 HVNC Cracked
Remote Access Trojans (RATs) continue to evolve as one of the most dangerous tools in a cybercriminal’s arsenal, enabling complete takeover of compromised systems. The emergence of cracked, commercially available RATs has lowered the barrier to entry for attackers, allowing even low-skilled threat actors to conduct sophisticated intrusions. The latest versions of these tools incorporate […]
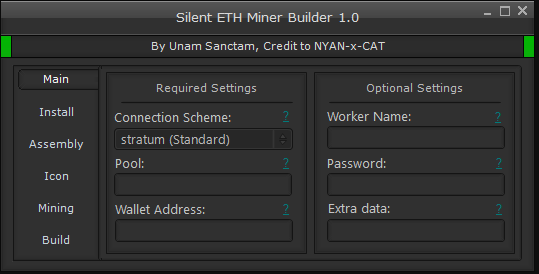
Silent ETH Miner v1.6.0
The cryptocurrency mining landscape has seen a surge in malicious cryptojacking attacks, with Silent ETH Miner v1.6.0 emerging as a particularly stealthy and efficient threat in modern cyberattacks. This sophisticated mining malware demonstrates how cybercriminals are exploiting system resources for unauthorized cryptocurrency mining without user consent. Silent ETH Miner v1.6.0 has been actively used in […]
Proxy Grabber and Proxy Checker 2025
In the ever-evolving landscape of cybercrime, tools that facilitate anonymity and bypass security measures have become increasingly valuable to threat actors. Among these, proxy manipulation utilities have gained prominence as they enable attackers to mask their activities and evade detection. The 2025 versions of Proxy Grabber demonstrate sophisticated capabilities that go beyond simple proxy management, […]
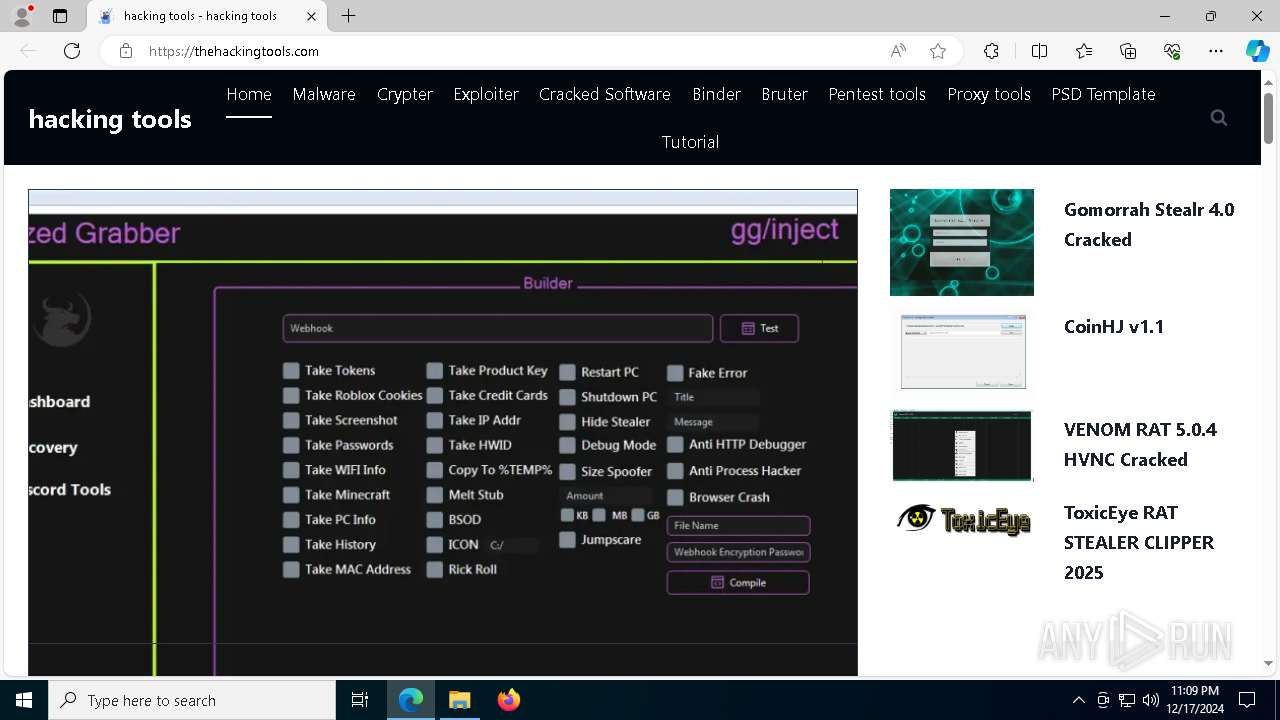
CoinHJ v1.1 – Crypto Coin Clipboard Hijacker
Cryptocurrency-related malware has become increasingly prevalent as digital currencies gain mainstream adoption. Among these threats, clipboard hijackers have emerged as a particularly insidious tool for cybercriminals. CoinHJ v1.1 operates silently in the background, monitoring and manipulating clipboard activity to redirect cryptocurrency transactions. The latest versions of such malware demonstrate improved stealth capabilities and broader targeting […]
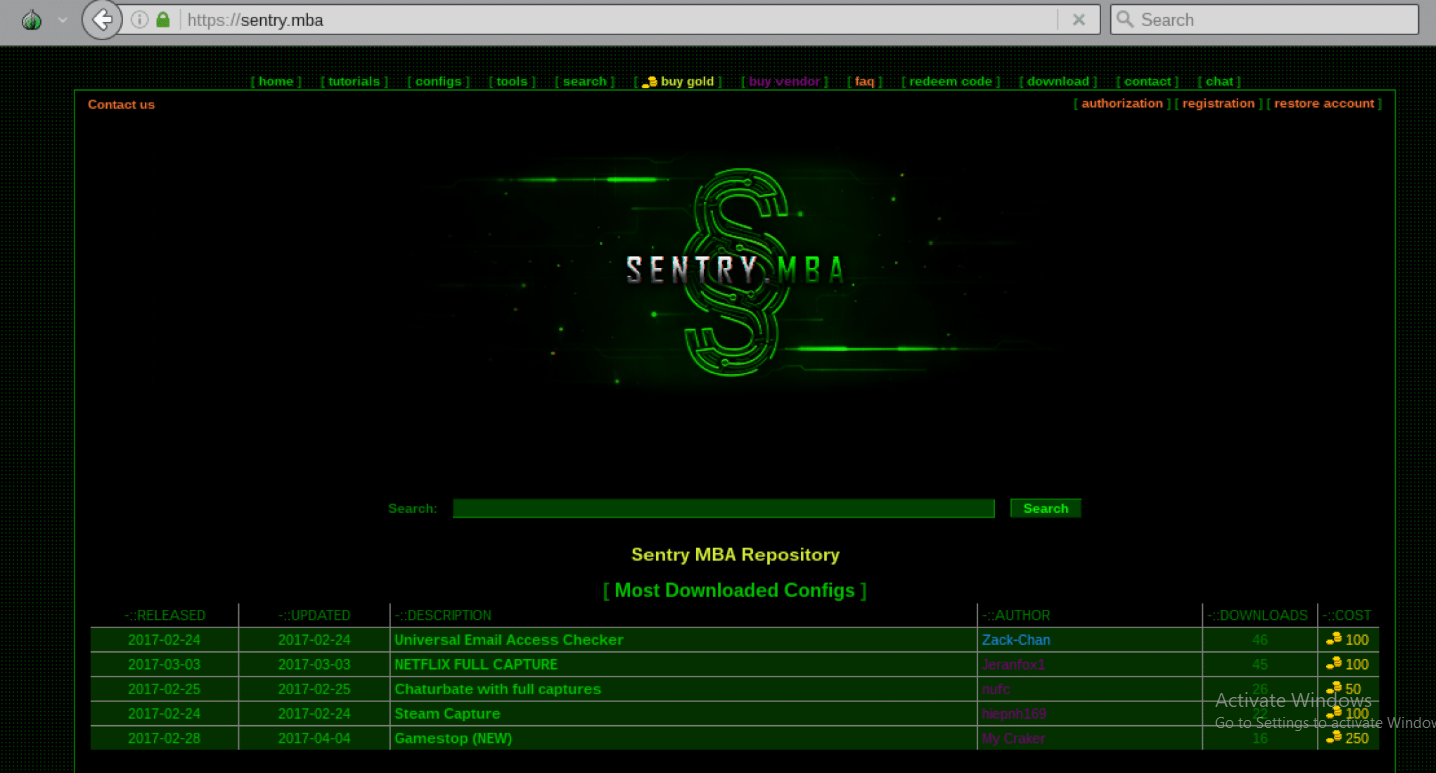
Sentry MBA 1.4.1 Cracked
Automated credential-testing tools have become a cornerstone of modern cyberattacks, enabling threat actors to breach online accounts at an unprecedented scale. Among these tools, modified versions of legitimate security testing software pose a particular threat when weaponized by malicious actors. These cracked or repurposed tools often incorporate enhanced evasion capabilities and underground exploit modules not […]
All Mail Brute 2025
Email account breaches remain one of the most damaging and prevalent threats in cybersecurity, serving as gateways to corporate espionage, financial fraud, and identity theft. Automated credential-cracking tools have become increasingly sophisticated, evolving to bypass modern security measures, such as multi-factor authentication (MFA) and account lockout policies. The 2025 generation of these attack platforms demonstrates […]
SpyBoxRAT Autumn Update 2
The SpyBoxRAT Autumn Update 2 of this surveillance tool highlights its growing sophistication in modern cyberattacks. As threats evolve, this software has adapted to bypass traditional security measures, making it a significant concern for organizations and individuals alike. Its ability to stealthily infiltrate systems, exfiltrate sensitive data, and maintain persistence underscores its role in advanced […]
Proxy Goblin 2.5.9.1 Cracked
Cyberattacks grow increasingly sophisticated as threat actors adopt advanced tools to bypass security measures and exploit vulnerabilities. Proxy Goblin 2.5.9.1, often distributed in cracked or illicit forms, is a proxy abuse utility designed to mask malicious activities. Attackers use this software to route traffic through multiple intermediaries, obscuring their origin and complicating detection. Security teams […]
BURP SUITE PROFESSIONAL V2023
In modern cybersecurity, web application vulnerabilities are a primary target for attackers, and tools that automate the exploitation of these weaknesses play a significant role in both offensive and defensive operations. BURP SUITE PROFESSIONAL V2023, widely used by both security professionals and malicious actors, is a powerful platform designed for testing and exploiting web applications. […]