Native Stealer Cracked 2025
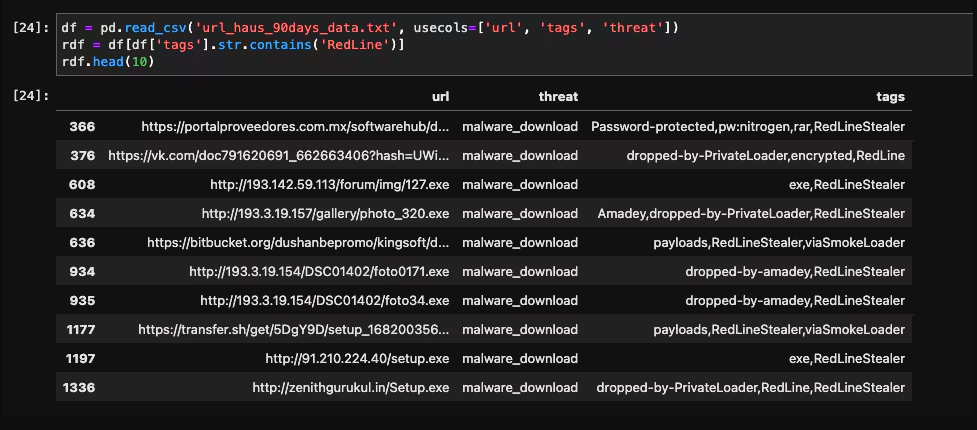
The cybercrime underground continues to evolve with increasingly sophisticated data theft tools, and Native Stealer has emerged as a particularly dangerous threat in modern cyberattacks. This advanced information-stealing malware demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful, low-cost attack tools. This malware has been actively used in credential harvesting campaigns […]
Pandora hVNC Cracked 2024
The rise of advanced remote access tools in cyberattacks has significantly increased the sophistication of modern threats. Among these tools, “Pandora hVNC Cracked 2024” has gained notoriety for enabling stealthy, persistent access to compromised systems. Often distributed through phishing campaigns or exploit kits, this tool allows attackers to bypass security measures and maintain undetected control […]
AVD Crypto Stealer 2025
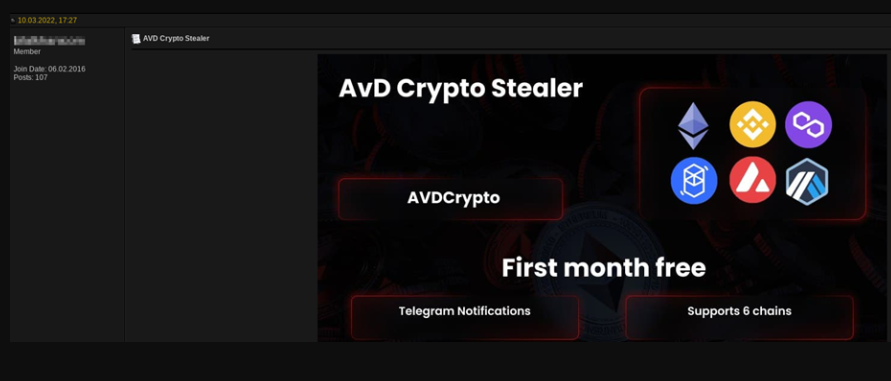
In 2025, cryptocurrency theft has evolved into a highly specialized form of cybercrime, with advanced malware tools targeting both retail investors and institutional crypto platforms. AVD Crypto Stealer 2025 sophisticated stealers represent a significant shift from traditional banking trojans, adapting to the unique challenges of blockchain transactions and decentralized finance (DeFi) ecosystems. Modern variants now […]
AndroSpy-v3
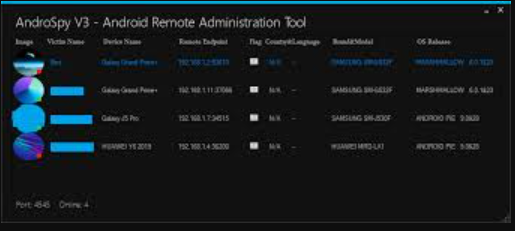
The mobile threat landscape has grown increasingly sophisticated, with AndroSpy v3 emerging as a particularly dangerous tool in modern cyberattacks targeting Android devices. This advanced surveillance malware exemplifies how cybercriminals are developing more stealthy and feature-rich tools to compromise smartphones. This malware has been actively used in targeted attacks against individuals and organizations, demonstrating its […]
PEGASUS LIME HVNC 2025
In 2025, advanced remote access threats have reached unprecedented levels of sophistication, with next-generation HVNC (Hidden Virtual Network Computing) tools becoming a weapon of choice for both cybercriminals and state-sponsored actors. PEGASUS LIME HVNC 2025 stealthy intrusion platforms represent a significant evolution from traditional RATs (Remote Access Trojans), offering complete device control while remaining virtually […]
WiFi Hacking for Beginners 2025
WiFi hacking remains a critical concern in modern cybersecurity, as wireless networks are often the weakest link in an organization’s defense. Attackers exploit vulnerabilities in WiFi Hacking for Beginners 2025, weak encryption, or poor configuration to gain unauthorized access, intercept data, or deploy malware. In 2025, beginner-friendly tools have made these attacks more accessible, allowing […]
Gray Keylogger v3 Cracked
The threat landscape continues to evolve with increasingly stealthy surveillance tools, among which Gray Keylogger has emerged as a particularly insidious threat. This advanced keylogging malware exemplifies how cybercriminals are developing more sophisticated methods to capture sensitive information without detection. Gray Keylogger v3 has been implicated in numerous credential theft campaigns and corporate espionage cases, […]
BTI Cpanel Bruteforcer 2025
In 2025, automated brute-forcing tools targeting web hosting control panels have become a significant threat to online security. BTI Cpanel Bruteforcer 2025 specialised tools allow attackers to systematically guess login credentials for cPanel, WebHost Manager (WHM), and other hosting management interfaces. Successful breaches provide attackers with full control over websites, databases, and email accounts, often […]
Diabolic Traffic Bot Full Edition v8.0 Activated
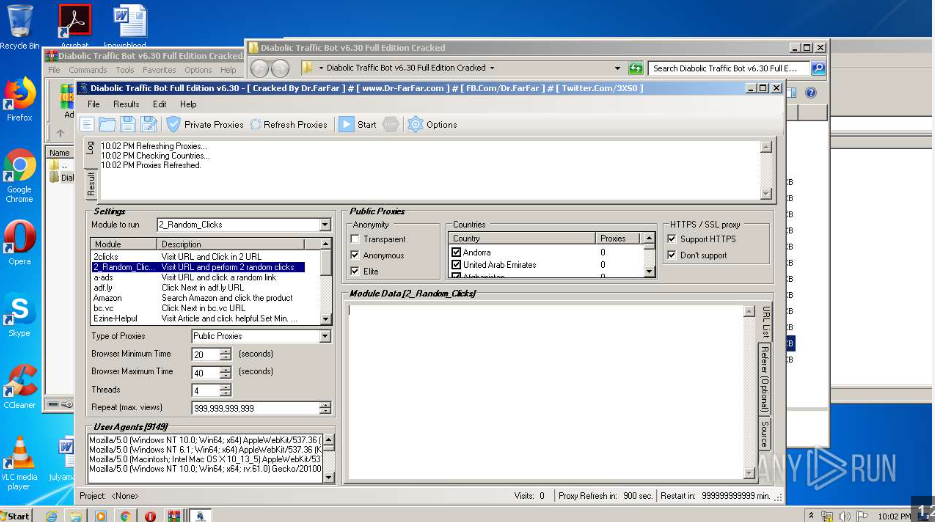
Automated tools that manipulate web traffic pose a growing challenge for cybersecurity professionals. Among these, traffic generation bots are particularly concerning. Diabolic traffic bot simulate human-like interactions to overwhelm websites, distort analytics, or commit fraud. Often, attackers use them in distributed denial-of-service (DDoS) attacks, ad fraud, or competitive sabotage. Because they mimic legitimate users at scale, […]
Blood DORKER 2025
In the evolving landscape of cyber threats, tools like Blood DORKER 2025 have gained notoriety for their role in modern cyberattacks. This software, in particular, exemplifies the growing sophistication of malicious tools. Often, it is used in targeted attacks to exploit vulnerabilities, exfiltrate data, or deliver additional payloads. Moreover, its modular design and evasion techniques […]