SQLi Dork Scanner with Dork list 2025
In modern cyberattacks, SQLi Dork Scanner) remains one of the most prevalent and dangerous vulnerabilities, allowing attackers to manipulate databases and extract sensitive information. Attackers often use specialized tools to automate the discovery of vulnerable websites. One such method involves leveraging search engine dorks—carefully crafted search queries that identify websites with potential security flaws. The […]
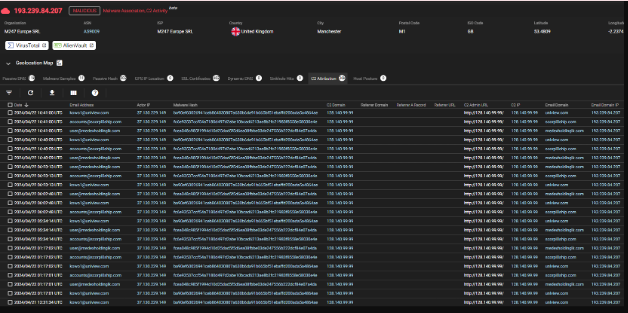
Agent tesla builder-3-2-5-5 cracked
In the ever-evolving world of cyber threats, agent-tesla-builder has become a significant concern for security professionals. These tools allow attackers to create customized malware strains with minimal effort, enabling widespread espionage, data theft, and system compromise. One such example is a well-known Remote Access Trojan (RAT) builder, frequently distributed on underground forums and used in […]
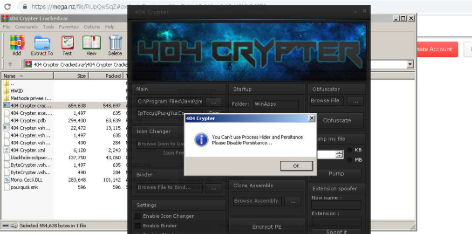
404 Crypter Cracked
In the evolving landscape of cyber threats, 404 Crypter Cracked have become indispensable tools for malicious actors seeking to evade detection. Cracked versions of these programs circulate in underground forums, democratizing access to advanced obfuscation techniques. These tools empower attackers to bypass traditional security measures, facilitating the distribution of ransomware, data stealers, and other malware. […]
Azorult Stealer v3.4 Cracked
In the ever-evolving landscape of cybercrime, information-stealing malware has become one of the most pervasive threats to both individuals and organizations. Among these threats, a particularly dangerous strain has emerged as a favorite among cybercriminals due to its versatility and effectiveness. This Azorult Stealer v3.4 Cracked, often distributed through phishing campaigns and exploit kits, specializes […]
Codelux Crypter v3.0 Cracked
Codelux Crypter v3.0 Cracked have become a critical tool for cybercriminals, enabling them to bypass security measures and deploy malware undetected. Cracked versions of such tools, often leaked or illegally distributed, lower the technical barrier for attackers, allowing even those with minimal expertise to launch sophisticated attacks. These crypters are commonly used in ransomware campaigns, […]
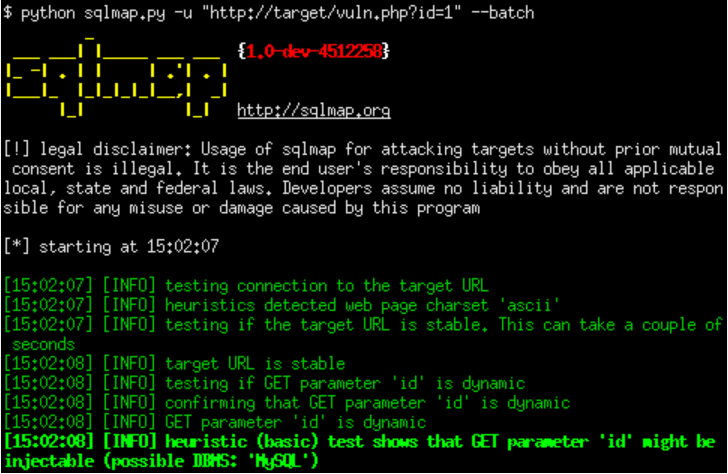
SQLi-DB-SQL Injection Dork Scanner v1.0
SQLi-DB-SQL Injection remains one of the most critical vulnerabilities in web applications, allowing attackers to manipulate databases and extract sensitive information. Automated tools designed to exploit these vulnerabilities play a significant role in both offensive security testing and malicious cyberattacks. Among these tools, SQLi dork scanners are widely used to identify vulnerable websites by leveraging […]
CyberSeal Crypter 2025 Cracked
In today’s threat landscape, CyberSeal Crypter 2025 Crackedplay a significant role in enabling cybercriminals to bypass security defences. These tools are frequently used to obfuscate malicious payloads, making them undetectable by traditional antivirus solutions. By encrypting, compressing, or modifying signatures, crypters allow attackers to deliver ransomware, spyware, and trojans without raising suspicion. Cracked or illegally […]
Trillium-security-multisploit-tool-v4-private-edition
In today’s evolving threat landscape, advanced exploitation frameworks have become a critical tool for both security professionals and malicious actors. One such tool, often referenced in penetration testing and cyberattack simulations, is a Trillium-security-multisploit designed to automate and streamline the exploitation of multiple vulnerabilities. These tools play a dual role—helping ethical hackers assess security defenses while […]
Proxifier Standard Edition V4.03 X64 with Keys
In the realm of cybersecurity, specific tools designed initially for legitimate purposes can be repurposed for malicious activities. One such example is Proxifier Standard Edition V4.03 X64, a powerful network utility that enables users to redirect and manage application traffic through proxy servers. While this software serves legitimate use cases, such as bypassing network restrictions […]