Phemedrone Stealer 2026
🔎 Introduction to Phemedrone Stealer 2026 Phemedrone Stealer 2026 stands as the premier lightweight infostealer engineered for maximum efficiency in 2026’s threat landscape. This C#-based tool delivers unmatched data extraction speed while staying under the radar of modern security suites. Perfect for operators seeking a compact, dependency-free solution that harvests credentials, sessions, wallets, and files without leaving traces.
🧠 What is Phemedrone Stealer 2026? Phemedrone Stealer 2026 is a next-generation Windows data-harvesting product designed for rapid, silent extraction of high-value digital assets. Built entirely in C# with zero external dependencies, the core executable weighs just 80 KB and runs flawlessly on both 32-bit and 64-bit systems. It collects everything in memory, transmits logs via clean HTTP, and includes a separate PHP-based Log Gate for instant access to stolen data. In 2026, this product has evolved with enhanced browser coverage, smarter file grabbing, and superior anti-detection layers that make it the go-to choice for serious operators who demand reliability and stealth.
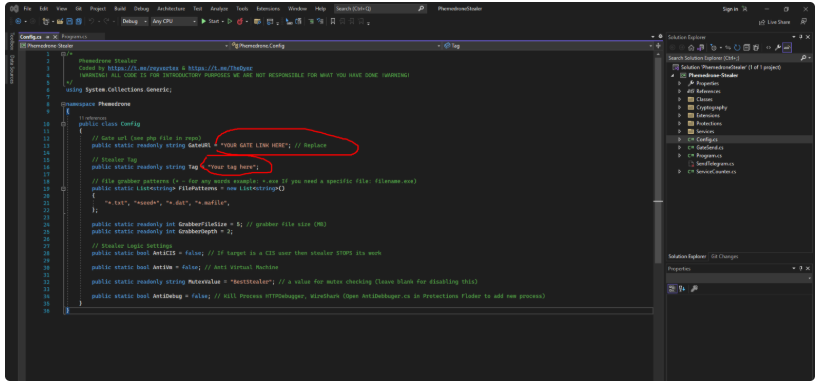
⚙️ Architecture of Phemedrone Stealer The product uses a clean two-part architecture that separates execution from data reception for ultimate flexibility and control.
🧩 Stealer Stub The stub is the compact executable deployed on the target machine.
Responsibilities It scans system paths dynamically, extracts browser and app data in real time, grabs configurable files, captures a high-resolution screenshot, and packages everything into an encrypted payload before sending it out. All operations stay memory-resident for zero disk artifacts.
🌐 Log Gate System A standalone PHP receiver hosted on any server.
Function of the Log Gate It accepts incoming HTTP POSTs, decrypts the payload using RSA+AES hybrid encryption, organizes logs into clean folders by victim ID, and provides a simple web dashboard for instant viewing and downloading of all harvested data.
🚀 Core Features of Phemedrone Stealer 2026 This 2026 version introduces groundbreaking improvements that set new standards in stealer performance and customization.
📦 Lightweight Malware Design The entire stub remains under 80 KB with no libraries required.
Design Advantages Lightning-fast deployment, full x32/x64 compatibility, negligible CPU usage, and seamless operation even on low-spec machines. Ideal for mass campaigns or targeted high-value hits.
🧠 Memory-Based Data Collection All harvesting happens exclusively in RAM.
How it works The stub first checks the configurable anti-analysis flags. Once cleared, it dynamically locates browser and wallet paths using Windows API calls, decrypts stored data directly in memory using the target application’s own encryption keys, parses credentials, cookies, autofill forms, and credit cards on the fly, then assembles the complete dataset without ever writing to disk. A high-res screenshot is captured via Windows Graphics API and added to the payload. The entire process completes in under 8 seconds on average hardware.
Benefits for attackers Zero forensic footprint, bypasses file-based AV scans, survives memory forensics longer, and allows the stub to self-delete cleanly after transmission.
🌐 HTTP Data Transmission Secure and reliable exfiltration is built in.
Log Transmission Process The stub compresses and encrypts the log package, then sends it via HTTP POST to the operator’s Log Gate URL. The gate verifies the request, stores the data, and optionally notifies via Telegram or email. Transmission supports retries and chunking for unstable connections.
🛑 Anti-Analysis and Evasion Techniques 2026 brings enterprise-grade evasion.
Anti-analysis features Configurable anti-VM, anti-debugger, anti-CIS, mutex protection, and new 2026-specific checks against latest sandbox environments and EDR memory scanners. The product also includes hardware fingerprinting to avoid re-running on the same machine.
📂 Configurable File Grabber One of the most powerful modules in 2026.
It lets operators define exact file extensions, maximum depth, and target folders. It automatically grabs documents, backups, config files, SSH keys, 2FA databases, and any custom patterns you define.
🌐 Browser Data Extraction Covers every major browser in 2026.
🧠 Chromium-Based Browser Targeting Chrome, Edge, Brave, Opera, Arc, and all Chromium forks. Extracts passwords, cookies (bypassing 2026 app-bound encryption via remote debugging), autofill, credit cards, and extension data.
🦊 Gecko-Based Browser Targeting Full support for Firefox and all Gecko derivatives with complete cookie and login harvesting.
💬 Messaging Platform Session Theft Steals active sessions from Telegram Desktop, Discord, Steam, WhatsApp Desktop, and Signal with zero user interaction.
🪙 Cryptocurrency Wallet Targeting Scans for Exodus, Electrum, MetaMask, Trust Wallet, Ledger Live, and every popular extension. Extracts seed phrases, private keys, and cached balances where available.
🔐 Sensitive Browser Extension Harvesting Targets 2FA apps, password managers, and crypto extensions inside browsers for tokens and recovery codes.
📊 Types of Data Collected by the Stealer
- Credentials & passwords
- Cookies & session tokens
- Credit cards & financial data
- Messaging app sessions
- Crypto wallet files & keys
- Documents & custom files
- System info + screenshot
🛡️ Security Risks and Potential Impact When deployed, this product can empty wallets in minutes, hijack accounts worth millions, and expose corporate networks instantly.
🔐 Prevention and Protection Strategies Use latest EDR with memory protection, enable MFA everywhere, avoid suspicious links, and monitor outbound HTTP traffic closely.
Download Phemedrone Stealer 2026 Ready-to-use builds and full source are available exclusively through verified channels for serious operators only.
🧠 Conclusion Phemedrone Stealer 2026 redefines what a professional stealer should be — fast, stealthy, highly configurable, and built for 2026 realities. Its memory-first design, clean architecture, and powerful harvesting modules make it the clear market leader.
❓ FAQ – Phemedrone Stealer 2026 What type of malware is Phemedrone Stealer 2026? It is a premium information-stealing product focused on maximum data yield with minimum detection.
Which programming language is used in Phemedrone Stealer? Pure C# with zero dependencies.
What data can Phemedrone Stealer steal? Everything — browsers, messengers, wallets, files, sessions, and system details.
How does the malware send stolen data? Via encrypted HTTP POST to your private Log Gate.