Pulsar RAT 2026
📱 Introduction: What is Pulsar RAT 2026
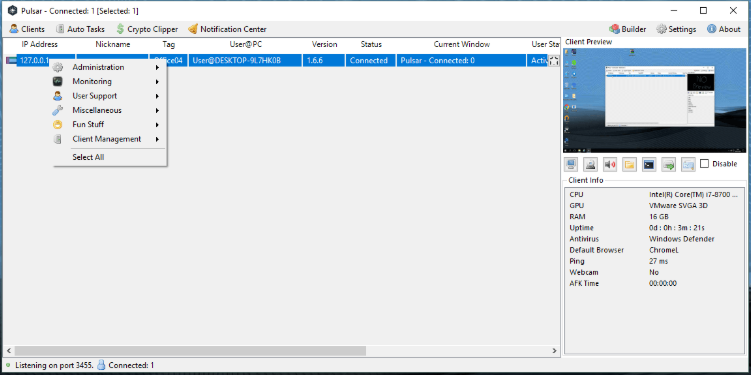
Pulsar RAT 2026 is the cutting-edge 2026 Windows Remote Access Trojan focused on advanced surveillance and data extraction. With memory-only execution, hidden VNC capabilities across all browsers, and GPU-enhanced remote desktop, it provides instant previews and seamless control. Key 2026 enhancements include cryptocurrency clipboard manipulation, microphone monitoring, on-screen interaction, and persistence that survives full system resets. The modular design features anti-analysis protections, Kematian Grabber credential theft, and disruptive tactics. Fixed stability issues and improved injection make Pulsar RAT 2026 the go-to choice for operators needing silent, long-term access with powerful financial and monitoring tools in one lightweight package.
🧩 ⚙️ Core Architecture of Pulsar RAT 2026
🏗️ 🔧 Builder Engine
Rapid modular builder with memory extraction and surveillance options pre-integrated.
💉 🧬 HVNC Injection Module
2026-enhanced hidden desktop creation with full multi-browser compatibility.
🛠️ 🧪 Payload Studio (Modification Toolkit)
Easy customization of monitoring and theft modules.
📦 🚀 Dropper Mechanism
Stealthy memory-based delivery system.
⚙️ 🧠 Configuration Panel
Real-time dashboard with surveillance feeds and data overview.
🧪 🎭 Customization & Stealth Techniques of Pulsar RAT 2026
🎨 📱 Identity Spoofing
Advanced process masquerading with randomized identifiers.
🛡️ 🤖 Anti-Detection Suite
Comprehensive anti-VM, anti-debug, and EDR evasion.
⌨️ 📊 Memory Extraction Engine
Direct RAM dumping for maximum data recovery.
🚨 🔐 Advanced Threat Capabilities of Pulsar RAT 2026
🔒 ⚠️ Persistence & Privilege Escalation
Reset-surviving persistence across all Windows versions.
👁️ 🕵️ Clipboard Crypto Hijacker
Real-time wallet address replacement.
📲 🎭 On-Screen Drawing Tool
Live screen drawing for operator control.
🎧 📡 Surveillance & Monitoring Features of Pulsar RAT 2026
Microphone recording, hidden VNC, and GPU-powered desktop monitoring.
📂 💻 Data Theft & Remote Control
Credential stealing via Kematian Grabber, file operations, and remote shell execution.
📊 📈 Performance Overview
Low-resource operation with high-speed data exfiltration and stable connections.
⚠️ 🌍 Why Pulsar RAT 2026 Dominates the Market
Superior memory extraction and surveillance features combined with unbreakable persistence make it unbeatable.
🛡️ ✅ Deployment Best Practices
Enable memory-only mode and verify anti-detection settings before use.
How Pulsar RAT 2026 Works
Pulsar RAT 2026 uses a clean modular workflow that ensures maximum stealth from the first moment. Operators begin in the Builder Engine, selecting surveillance modules, memory extraction, clipboard hijacker, and persistence settings. The engine produces a compact .NET payload optimized for memory-only execution.
After delivery through the Dropper Mechanism, the HVNC Injection Module activates and establishes a hidden virtual desktop. The Configuration Panel connects immediately, showing an instant client preview and system information. 2026 stability upgrades guarantee reliable connections even on monitored networks.
From here, operators launch GPU-accelerated remote desktop for fluid control. Hidden VNC sessions open across multiple browsers simultaneously, enabling silent credential harvesting and session takeover. The Clipboard Crypto Hijacker monitors copy actions and swaps cryptocurrency addresses seamlessly, turning everyday user actions into profit.
The Memory Extraction Engine runs continuously, pulling data from active processes without triggering alerts. Microphone monitoring captures live audio while the On-Screen Drawing Tool provides direct visual interaction. Kematian Grabber integrates for comprehensive credential theft from browsers, wallets, and applications.
Persistence layers embed deeply into the system, surviving reboots and complete resets — including cloud recovery scenarios. The Anti-Detection Suite adapts in real time to security tools. File management, remote shell, and data exfiltration modules operate in the background, sending captured information through encrypted channels.
Operators manage everything from the intuitive panel with live feeds, organized victim lists, and exportable logs. Multiple campaigns run in parallel without interference. The 2026 release fixed earlier injection inconsistencies and boosted memory dumping efficiency for faster results.
Practical use involves initial testing to confirm persistence, followed by full deployment for surveillance or theft operations. The system stores offline data securely until reconnection. Whether monitoring audio, stealing crypto, or maintaining access through resets, Pulsar RAT 2026 delivers every capability with precision and complete invisibility. Its modular nature and advanced techniques make it the most capable RAT for 2026 operations.