RATs Packs 2026
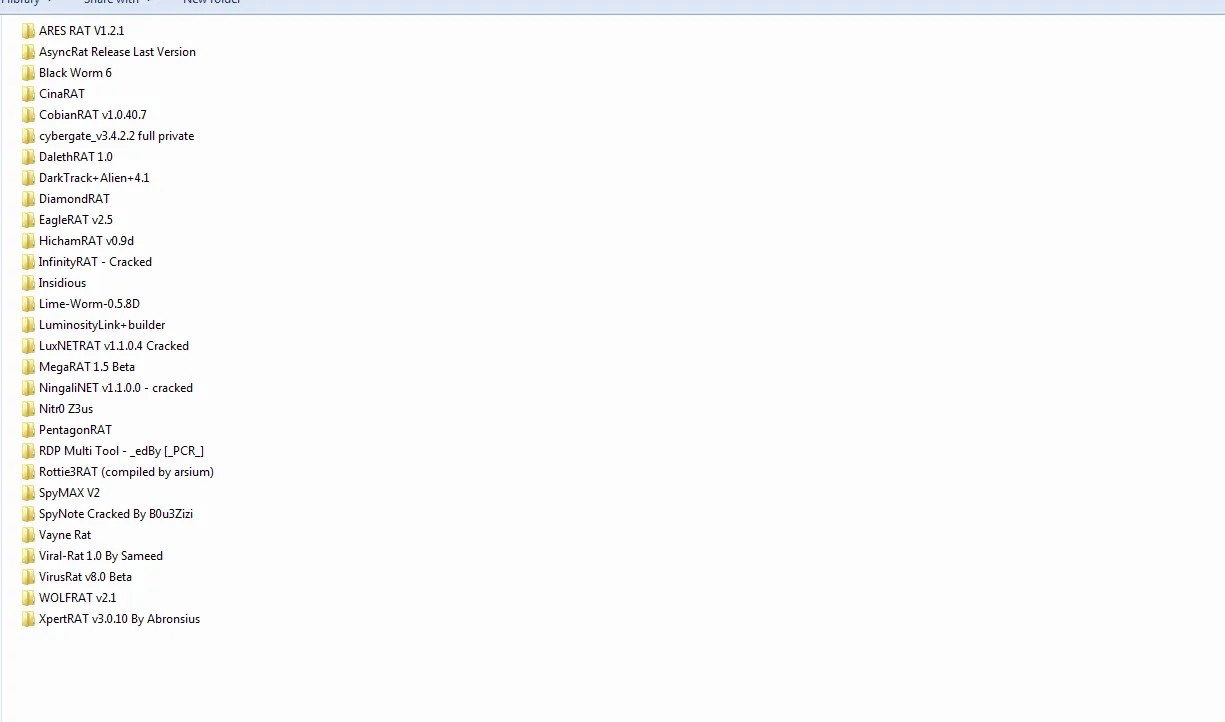
RATs Packs 2026 is a revolutionary cybersecurity asset built to enable specialists in spotting, decoding, and neutralizing remote access risks in online realms. Geared toward ethical hackers and security professionals, its primary goal is to emulate and deconstruct RAT (Remote Access Trojan) functions to enhance safeguards against intricate cyber attacks. The standout advantage? It’s superior instant simulation tools that integrate AI-based analytics with streamlined user experiences, rendering a sophisticated threat exploration approachable for all skill levels.
Key Features and Explanations
- Instant RAT Mimicry Mechanisms: RATs Packs 2026 features robust mimicry engines that emulate real RAT tactics, permitting safe network testing to expose flaws before exploitation occurs.
- AI-Fueled Anomaly Spotting: Employing cutting-edge learning algorithms, it inspects data streams and histories for oddities, issuing predictive warnings on impending RAT threats. Optimized for swift operations, it reduces unnecessary alarms.
- Extensive Malware Study Package: Dive into RAT examples within a secure sandbox, retrieving hidden loads, instruction chains, and endurance features. This package accommodates diverse file kinds and merges forensic aids for detailed analyses.
- Flexible Attack Reconnaissance: Develop personalized breach models to simulate RAT setups across different setups, including IoT and business servers. This encourages preventive measures by disclosing overlooked vulnerabilities.
- Built-In Audit and Regulatory Functions: Create thorough records and regulation-aligned outputs conforming to frameworks like GDPR and NIST. The control panel illustrates threat overviews, facilitating tactical planning.
- Collaborative Upgrade System: Access frequent updates and crowd-sourced RAT types, staying ahead of new challenges. This group dynamic cements its role as a vanguard in cybersecurity. RATs Packs 2026 distinguishes itself with its comprehensive methodology, fusing mimicry, detection, and breakdown to build a solid defense against remote access exploits.