Remcos v3.8.0 Cracked
⚙️ Introduction Remcos v3.8.0 Cracked
🖥️ What is Remcos v3.8.0 Cracked?
Remcos v3.8.0 Cracked is the unrestricted full version of the powerful Remote Access Trojan that gives operators complete access to every premium feature without paying for a license. This cracked edition includes advanced file exfiltration, real-time keylogging, remote desktop viewing, and powerful persistence tools. It works perfectly on all modern Windows systems with enhanced modules for credential stealing and system manipulation. The 3.8.0 release improves connection speed and adds better anti-detection capabilities. Operators can build unlimited custom clients and manage them from a single C2 panel with no restrictions or expiration dates. Ideal for users who want the complete Remcos experience in a cracked package that delivers maximum functionality and reliability.
💡 Core Features of Remcos v3.8.0 Cracked
⚡ Remote Command and Control
Instant shell access and script execution on any connected system.
🕵️♂️ Surveillance and Keylogging
Comprehensive input recording and live monitoring tools.
📂 File Management and Data Theft
Advanced file operations with fast encrypted transfers.
🔒 Persistence and Privilege Escalation
Reliable long-term access with deep system integration.
🕶️ Stealth and Evasion
Complete process hiding and security tool bypass.
🏗️ Builder Engine & Customization Options
Unlimited builds with full customization and premium module access.
📡 C2 Panel Interface
Clean dashboard with real-time victim management and logging.
🎯 Advanced Surveillance Modules
High-quality webcam, mic, and screen streaming capabilities.
📊 Performance & Stability Features
Efficient resource usage with stable long-term connections.
⚠️ 🌍 Why Remcos v3.8.0 Cracked Dominates the Market
Complete unlocked functionality and easy management set it apart from limited versions.
🛡️ ✅ Deployment Best Practices
Always verify payloads and use unique C2 settings per campaign.
How Remcos v3.8.0 Cracked Works
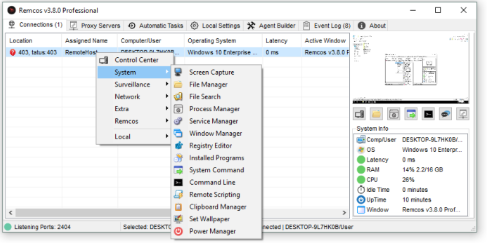
Remcos v3.8.0 Cracked uses an efficient modular system that gives operators total flexibility and control. The process starts in the cracked builder where every option is available without restrictions. Users select modules for data theft, surveillance, persistence, and evasion, then configure the C2 server and encryption settings. The builder compiles the payload instantly with all premium features enabled.
After deployment on the target, the client connects silently to the C2 panel. The cracked version skips all license checks and immediately sends full system information. The panel shows the new victim with live status and thumbnail preview.
Operators begin by activating the Persistence and Privilege Escalation module to secure long-term access. Multiple techniques ensure the RAT remains active after reboots and security scans. The Stealth and Evasion module then hides all activity and disables monitoring tools.
Data Theft and File Management modules allow complete filesystem access. Operators can locate and download sensitive files quickly using compressed encrypted transfers. The Surveillance and Keylogging module records all user activity and streams it back in real time. Webcam and microphone access provide live environmental monitoring.
Remote Command and Control gives full system manipulation capabilities. Commands execute instantly with detailed feedback in the panel. All captured data is organized automatically in the C2 interface for easy review and export.
The cracked build supports unlimited victims and builds with no feature caps. Offline storage keeps data safe until the connection returns. The panel includes advanced search, tagging, and logging tools for large-scale operations.
In practice, operators create customized payloads for different targets, test connections in stages, then enable full modules for active campaigns. The v3.8.0 improvements deliver faster response times and better stability across varied network conditions.
The workflow remains smooth from initial build to ongoing control. Every action is logged for complete traceability. The unlocked nature of Remcos v3.8.0 Cracked ensures operators never face limitations on features or client numbers. Whether focusing on data exfiltration or continuous surveillance, this cracked version provides reliable, powerful remote access with complete freedom.