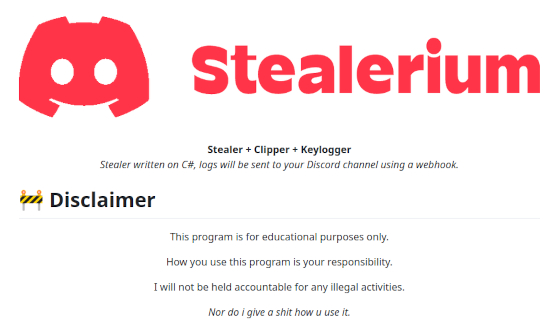
Stealerium Stealer 2026
Stealerium Stealer 2026 emerges as an elite cybersecurity instrument tailored for penetration testers and white-hat hackers, dedicated to replicating and investigating data exfiltration risks in simulated conditions. At its heart, it assists enterprises in detecting weaknesses through the emulation of cutting-edge malicious software strategies, fostering robust safeguards against online invasions. A notable benefit lies in its exceptional covert operation, which gathers crucial data quietly without flagging detection systems, crucial for forward-looking security evaluations.
Download Link 1
Download Link 2
Download Link 3
Feature Breakdown
- Concealed Execution: Enables the program to function undetected on infected devices, pulling out private information, including access credentials and online logins, without arousing antivirus alerts, ideal for extensive security checks.
- Multi-OS Compatibility: Works across Windows, macOS, and Linux platforms, facilitating widespread data gathering and allowing specialists to scrutinize diverse environments for latent security gaps.
- Instant Logging Features: Includes live logging that documents all processes immediately, supplying in-depth overviews of data transmission trails, supporting experts in tracing breach points and reinforcing defenses.
- Flexible Malware Customization: Allows users to tailor scripts for precise applications, such as mirroring attacks on financial or networking services, increasing its utility in research and emergency preparedness exercises.
- Sophisticated Bypass Mechanisms: Utilizes advanced cloaking strategies to sidestep current endpoint security solutions, ensuring uninterrupted testing and providing knowledge on circumvention approaches.
- Export and Examination Capabilities: Easily forwards amassed information in various file formats for detailed scrutiny, with support for tools like Wireshark to amplify cyber threat analysis.