Twitch Tools Pack 2024
As live streaming platforms like Twitch continue to grow in popularity, they have become lucrative targets for cybercriminals seeking to exploit both streamers and viewers. In 2024, specialized toolkits have emerged that automate malicious activities such as viewbotting, chat manipulation, credential theft, and even distributed denial-of-service (DDoS) attacks against broadcasters. Twitch Tools Pack 2024 tools undermine platform integrity, distort analytics, and enable harassment campaigns while evading Twitch’s security measures. Their widespread availability has made them a persistent threat to content creators and the broader streaming ecosystem.
Download Link 1
Download Link 2
Download Link 3
Download Link 4
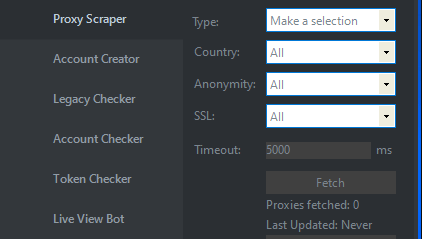
This software package is a collection of utilities designed to interact with Twitch’s platform in ways that violate terms of service. While some components may appear benign (like chat automation tools), the suite often includes capabilities for artificial engagement inflation, account compromise, and channel disruption. Malicious users typically deploy these tools to gain unfair advantages, sabotage competitors, or monetize streams through fraudulent means. The modular nature of the package allows attackers to customize their approach based on specific objectives, ranging from subtle manipulation to overt platform abuse.

Key Features
| Feature | Description |
| Viewbot Network | Artificially inflates viewer counts using proxy-distributed connections |
| Chat Spam Engine | Automates message flooding with configurable delay/rotation |
| Credential Harvester | Phishes login details through fake Twitch auth pages |
| Follow/Sub Bot | Manipulates social metrics using compromised or fake accounts |
| Stream Sniping Toolkit | Provides real-time analytics and alerts for targeted harassment |
| DDoS Component | Launches traffic floods against streamer connections (optional module) |
| Ad Fraud System | Generates fake ad impressions for revenue exploitation |
How Twitch Tools Pack 2024 Works
1. Setup and Configuration
- The operator first configures target channels and desired manipulation parameters
- Proxy lists are imported to distribute malicious traffic across multiple IP addresses
- For credential attacks, fake login pages are hosted on compromised servers with Twitch-branded templates
2. Core Functionality
View Manipulation:
- Creates hundreds of concurrent connections through proxy networks
- Simulates “real” viewer behavior with periodic refresh cycles
- Randomizes watch durations to avoid pattern detection
Chat Abuse:
- Deploys multiple bot accounts with human-like typing delays
- Bypasses spam filters through message variation algorithms
- Can harvest chat logs for social engineering purposes
Account Compromise:
- Sends phishing links disguised as “verification” or “partner program” emails
- Uses WebSocket injections to steal auth tokens from compromised browsers
- Automates credential stuffing attacks against accounts with weak passwords
3. Evasion Techniques
- IP rotation through residential proxy services
- Randomized user-agent strings mimicking popular browsers
- Adaptive timing that slows during Twitch moderator patrols
- Gradual metric inflation to avoid sudden detection spikes
4. Payload Delivery
Depending on the attack type:
- Monetization Fraud: Fake ad clicks generate illegitimate revenue
- Reputation Attacks: Mass false reports trigger automated suspensions
- Competitor Sabotage: Chat spam triggers auto-moderation timeouts
Credential Theft: Stolen accounts are sold or used for further attacks


