Vidar Stealer 2025
What is Vidar Stealer 2025?
Vidar Stealer 2025 is the invisible empire builder that has taken over the infostealer scene in 2025. This sophisticated C++ MaaS malware silently harvests data from 50+ browsers, drains 200+ crypto wallets, steals Discord/Telegram/Steam/Roblox sessions, hijacks clipboards, captures screenshots, grabs files, and collects VPN configs with near-zero detection rates. Updated every 7–14 days by @Vidar_1337, the latest builds include powerful anti-VM protection, modular plugins, and optional ransomware or loader features. Affordable lifetime licenses make it accessible yet extremely powerful. Vidar Stealer 2025 lets operators build massive data empires while staying completely under the radar. Stealthy, modular, and relentlessly effective — this is the stealer that defines 2025. ⚡
🌐 Stealth Browser Harvest Engine
Silently extracts passwords, cookies, autofill, and credit cards from 50+ browsers without any visible activity.
💰 Silent Crypto Wallet Assassin
Drains 200+ wallets including MetaMask, Exodus, Atomic, Trust Wallet, and Phantom with zero user alerts.
🔑 Invisible Session Thief
Grabs Discord tokens, Telegram sessions, Steam, Roblox, and authentication cookies in complete silence.
📋 Phantom Clipboard Hijacker
Replaces copied crypto addresses invisibly with the attacker’s wallet.
📸 Ghost Screenshot & Profiler
Takes desktop screenshots and logs full system information including IP and AV without traces.
📁 Hidden File Grabber
Quietly steals valuable documents and wallet files under 5 MB from key user folders.
🔐 Covert VPN & Messaging Extractor
Pulls NordVPN, OpenVPN, ProtonVPN configs plus Telegram and Signal sessions undetected.
🛡️ Ultimate Anti-Detection Shield
Anti-VM, anti-analysis, and sandbox evasion ensure total invisibility on any system.
📤 Modular Empire Builder
Add ransomware or loader modules to expand operations and drop secondary payloads automatically.
📊 How It Works: Stealth Step-by-Step Assault
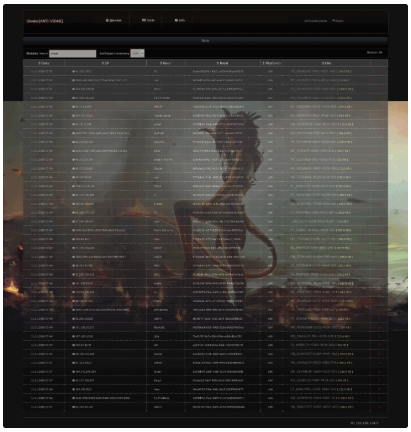
Vidar Stealer 2025 moves like a ghost through the system. The attacker configures the payload via the MaaS panel, selecting C2, wallet addresses, and active modules. The compiled executable is spread through cracked software, fake downloaders, or malicious ads.
Once executed, Vidar elevates privileges and injects silently. The Stealth Browser Harvest Engine begins collecting data from all browsers while the Silent Crypto Wallet Assassin drains wallets. The Invisible Session Thief grabs live tokens and sessions as the Phantom Clipboard Hijacker starts its work.
The Ghost Screenshot & Profiler captures visual evidence and system details. The Hidden File Grabber and Covert VPN & Messaging Extractor pull additional files and configs without any noise. All data is encrypted and exfiltrated to the attacker’s server.
The Ultimate Anti-Detection Shield keeps everything invisible. If chosen, the Modular Empire Builder activates ransomware or drops secondary malware like Lumma or XWorm. The entire process runs with minimal resources and leaves almost no forensic traces.
Operators rely on Vidar Stealer 2025 for its stealth and reliability. Its frequent updates and modular system make it the perfect tool to build and expand data empires silently in 2025. Deploy invisibly, harvest massively, and dominate without ever being seen.