Vortex Malware Clipper V3.5
What is Vortex Malware Clipper V3.5?
Vortex Malware Clipper V3.5 is the invisible crypto ghost that haunts clipboard operations and drains funds across 15+ blockchains in complete silence. This 2025 advanced malware detects copied wallet addresses and instantly replaces them with attacker wallets for Bitcoin, Ethereum, Tron, and many others. Equipped with powerful persistence, anti-VM, code mutation, Defender bypass, file size manipulation, and network/USB spreading, it remains undetectable while operating 24/7. The latest build installs stealthily into system folders, uses mutex protection, and mimics legitimate apps. Vortex Malware Clipper V3.5 is the ultimate low-detection, high-profit tool for operators who need ghost-like crypto theft with zero user awareness. Stealthy, relentless, and built for 2025 dominance. ⚡
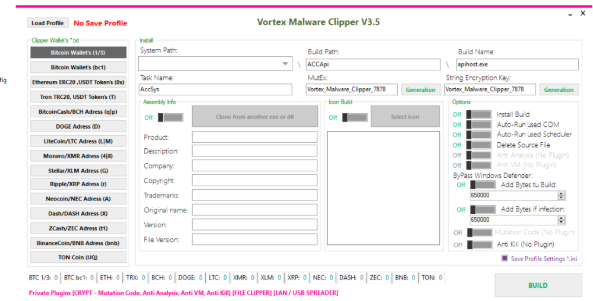
🌐 Ghost Blockchain Targeting
Silently hijacks addresses across Bitcoin, Ethereum, Tron, Dogecoin, Litecoin, Monero, Stellar, Ripple, Dash, ZCash, BNB, TON Coin and more.
📋 Phantom Clipboard Engine
Replaces copied addresses invisibly with zero delay or visible notification.
🛡️ Ultimate Anti-Detection Shield
Anti-VM, anti-debug, sandbox evasion, code mutation, and Defender bypass for total invisibility.
🔄 Eternal Persistence Core
Multiple methods including COM hijacking and Task Scheduler ensure survival forever.
📁 Stealth Size Inflation
Artificially grows file size to bypass heuristic detection systems.
📡 Ghost Spreading Module
Propagates silently via local network and USB devices to expand reach.
🖥️ Invisible Installation Suite
Hides in standard system folders while cloning legitimate application traits.
🔑 Phantom Mutex Protection
Unique mutex prevents conflicts and shields the process from termination.
📊 How It Works: Stealth Step-by-Step Assault
Vortex Malware Clipper V3.5 operates like a true ghost in the machine. The attacker prepares the payload with target wallets and enables all evasion and persistence options. The executable is delivered through any stealth vector.
Once launched, the malware elevates silently and installs itself into multiple hidden system locations while mimicking legitimate software. The Phantom Clipboard Engine activates and begins constant monitoring.
Every time a crypto address is copied, the Ghost Blockchain Targeting instantly detects the pattern and swaps it with the attacker’s wallet. The victim pastes the fake address and loses funds permanently. The entire replacement happens in complete silence.
The Ultimate Anti-Detection Shield constantly scans for threats and activates evasion routines. The Eternal Persistence Core sets up survival mechanisms while the Ghost Spreading Module quietly propagates to other systems. Stealth Size Inflation confuses scanners and the Phantom Mutex Protection keeps everything safe.
No windows, no alerts, no visible activity — just pure invisible theft. The whole process runs smoothly with minimal resources. Operators in 2025 call Vortex Malware Clipper V3.5 the most effective ghost clipper available. Deploy silently, drain continuously, and remain completely invisible. This is next-level crypto ghosting perfected.