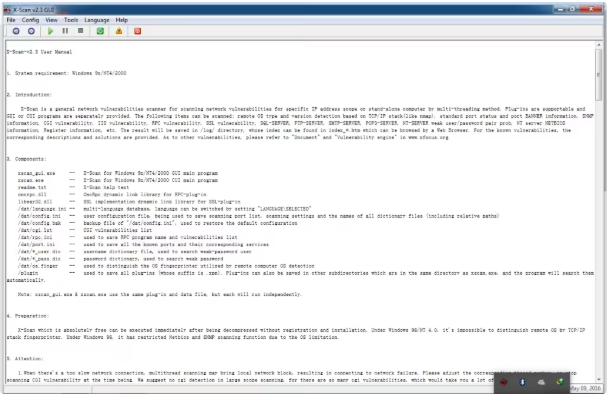
X Scan V3.3
What is X Scan V3.3?
X Scan V3.3 is the silent network ghost that quietly scans and enumerates credentials across multiple protocols with zero noise in 2025. This stealthy Windows tool checks hostnames, default ports, FTP user/pass, SSH vulnerabilities, Telnet, SMTP, fingerprints, HTTP, POP3, NT weak accounts, IMAP, MySQL, and CISO passwords while staying completely under the radar. Designed for discreet, high-volume operations, it delivers clean results without triggering alerts or leaving traces. Lightweight, portable, and built for operators who need silent reconnaissance and credential collection, X Scan V3.3 is the ultimate ghost scanner for building massive databases and identifying hidden weaknesses across any network. Invisible, efficient, and relentlessly effective. ⚡
🚀 Silent Hostname & Port Ghost
Resolves and scans targets invisibly with zero visible activity.
🔑 Phantom Credential Harvester
Quietly validates FTP, POP3, IMAP, MySQL, and NT accounts in complete silence.
🛡️ Invisible SSH & Telnet Ghost
Detects vulnerabilities and access points without any network noise.
📧 Stealth SMTP & HTTP Scanner
Analyzes servers discreetly with no alerts or footprints.
🧬 Ghost Fingerprint Module
Identifies services silently for perfect targeting.
📬 Phantom Account Enumerator
Enumerates accounts across protocols without triggering defenses.
🖥️ Silent NT Weakness Finder
Locates weak accounts and patterns in total stealth.
🔓 CISO Password Ghost Cracker
Cracks high-value passwords invisibly and efficiently.
📊 How It Works: Stealth Step-by-Step Assault
X Scan V3.3 operates like a ghost in the network. Launch the portable tool and the minimalist interface loads instantly. Import targets silently and the Silent Hostname & Port Ghost begins its invisible work.
All modules run in stealth mode: Phantom Credential Harvester, Invisible SSH & Telnet Ghost, Stealth SMTP & HTTP Scanner, and Ghost Fingerprint Module collect data without any visible signs. The Phantom Account Enumerator and Silent NT Weakness Finder work quietly while the CISO Password Ghost Cracker handles premium targets.
Results appear in the clean dashboard with zero noise. Export everything discreetly and repeat the process on new networks. The entire operation stays under the radar while delivering maximum intelligence.
Operators trust X Scan V3.3 for its silent efficiency and perfect stealth in 2025. This is invisible network domination perfected.