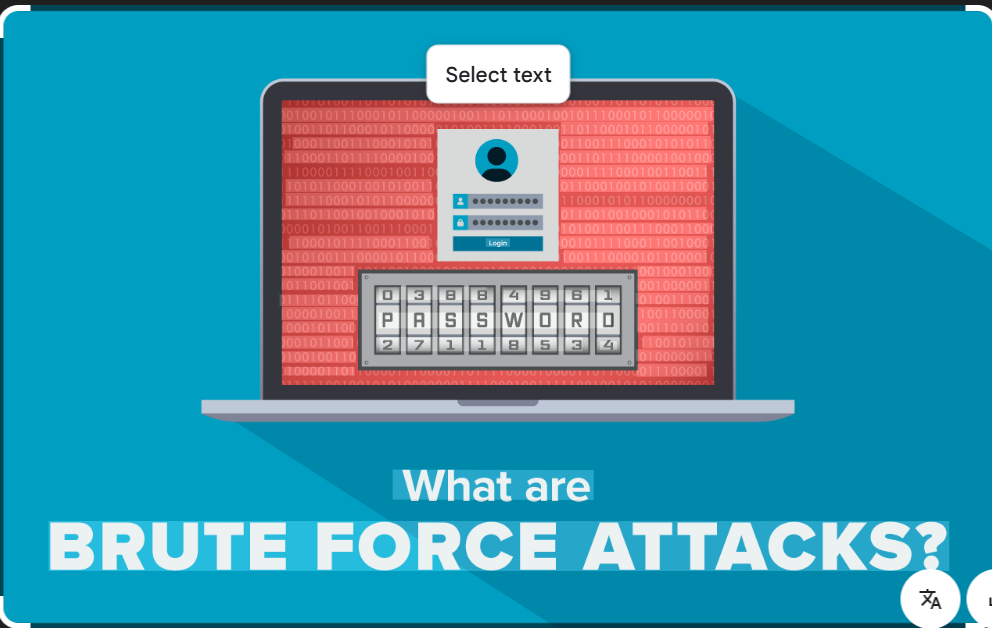
Bruter
Here are all types of bruter like Password Bruters, Hash Bruters, Wi-Fi Bruters, API/Token Bruters, ZIP/RAR Bruters, Credential Stuffing Tools.
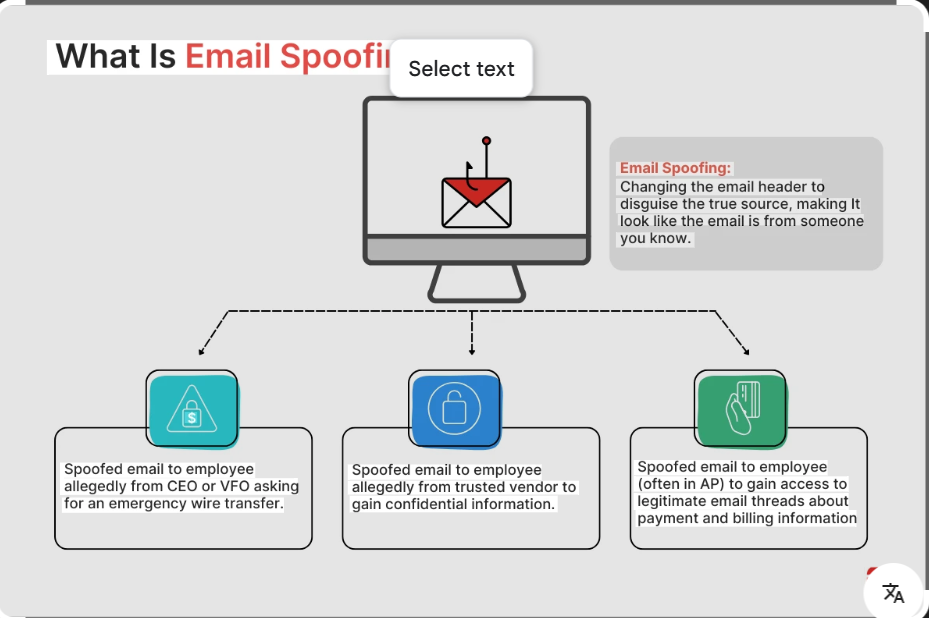
Neos Email Spoofer 2026 The Premier Tool for Spoofing Mastery
Short Intro: Neos Email Spoofer 2026 is an innovative cybersecurity utility engineered for spoofing emails to test network vulnerabilities and enhance defenses. It serves the purpose of enabling controlled simulations of phishing attacks and sender impersonation in professional environments. What sets it apart is its adaptive stealth mode, which automatically adjusts to maintain invisibility against […]
Master SMS Flooding with NSD SMS Bomber 2026 Full Version
Short Intro: As a specialized cybersecurity tool, NSD SMS Bomber 2026 empowers security experts to perform rigorous SMS bombardment tests on mobile infrastructures. Its main objective is to expose weaknesses in SMS handling systems, promoting stronger defenses against distributed attacks. Boasting lightning-fast performance and intuitive controls, it delivers unmatched precision for professional-grade analysis. Feature Explanations: […]
Elevate Your Security Arsenal Exploring Combat SMS Bomber 2025
Short Intro: Combat SMS Bomber 2025 is a premier cybersecurity instrument crafted to emulate and counteract SMS flooding assaults, safeguarding communications infrastructure. Its core function is to unveil weaknesses in SMS protocols through controlled experiments, driving stronger protective measures. The standout USP is its AI-driven optimization, which adapts simulations for maximum accuracy and minimal disruption. […]
Secure Your Digital Assets with Saddam Crypter 2026
Short Intro: Introducing Saddam Crypter 2026, a powerful cybersecurity solution crafted to encrypt and obfuscate executables, preventing unauthorized access and analysis. It serves developers and enterprises by offering unparalleled protection against decompilers and forensic tools, revolutionizing how sensitive code is secured. What sets it apart is its AI-driven adaptive encryption, which evolves to counter the […]
Introducing Zeus Crypter 2026 Cybersecurity Solution
Short Intro: Zeus Crypter 2026 stands as a premier cybersecurity tool engineered to encrypt executables and shield them from prying eyes. Its core purpose revolves around creating impervious barriers against detection technologies, empowering users in the digital landscape. What sets it apart is its unparalleled efficiency in achieving a fully undetectable status, a game-changer for […]
Advanced Cybersecurity with Anubis Android Banking Bot 2026
Short Intro: Anubis Android Banking Bot 2026 is a cutting-edge cybersecurity tool designed to simulate and detect sophisticated banking malware on Android devices. Its primary purpose is to empower security professionals and developers to test defenses against financial threats in a controlled environment. A key USP is its real-time emulation of banking bot behaviors, providing […]
Penetration Testing Using the Reliable Gmail Bruteforcer 2026
Short Intro: Introducing the Gmail Bruteforcer 2026, an essential cybersecurity utility for professionals conducting authorized brute-force simulations on Gmail logins to expose weak password practices. Its core purpose is to empower security experts in fortifying online accounts against unauthorized access through rigorous testing. What sets it apart is its user-friendly interface combined with robust algorithms, […]
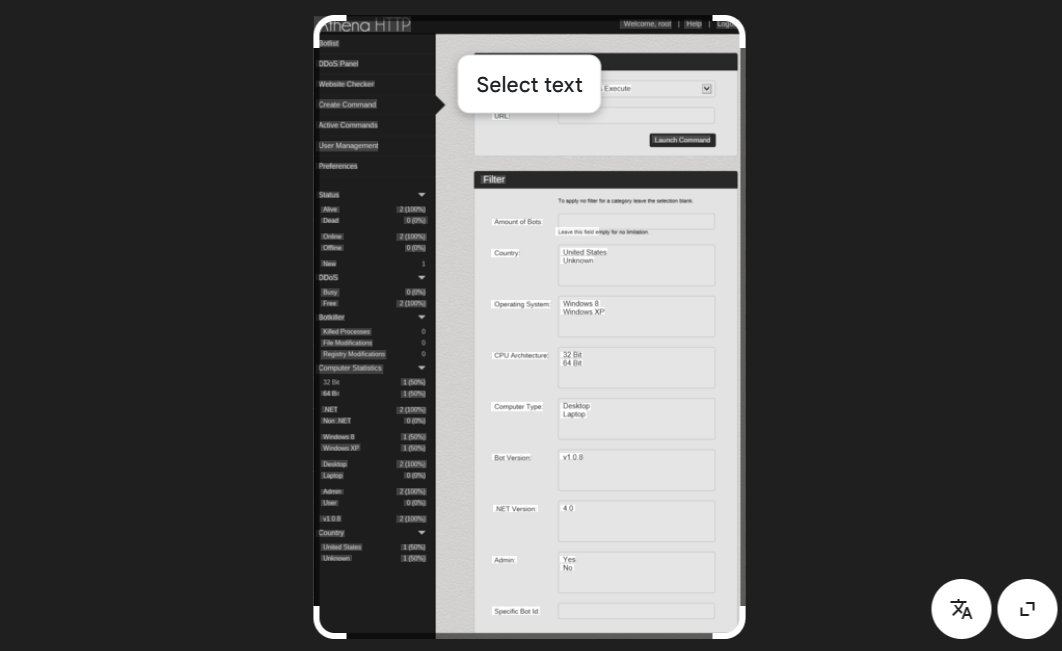
Revolutionize Your Cybersecurity Arsenal with HTTP Botnet Mastery Athena HTTP Botnet 2026
Short Intro: Introducing Athena HTTP Botnet 2026, a premier cybersecurity solution tailored for penetration testers and IT security teams. This tool specializes in orchestrating HTTP botnet simulations to identify and mitigate vulnerabilities in web infrastructures. What sets it apart is its AI-driven automation, which adapts attacks in real-time for more authentic and effective testing scenarios. […]
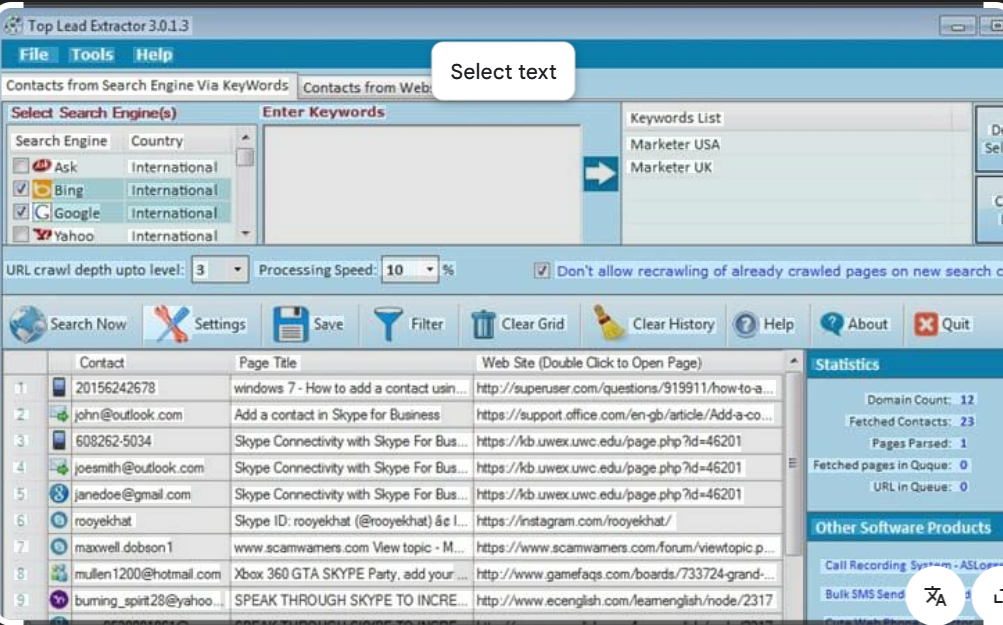
Email Extractor 2026 Advanced Cybersecurity Solution for Email Data Retrieval
Short Intro: Email Extractor 2026 stands out as a robust cybersecurity tool engineered to harvest email addresses from diverse sources, empowering experts to fortify defenses against cyber threats. Its core purpose revolves around facilitating rapid data analysis for risk assessments and forensic investigations. The standout USP lies in its encryption-focused architecture, which safeguards extracted information […]
Advanced RDP Bruter and Scanner 2026: Boost Your Cyber Defense Arsenal
Short Intro: Introducing the Slayer RDP Scanner and Bruter 2026, a powerful cybersecurity solution tailored for auditing RDP (Remote Desktop Protocol) environments through comprehensive scanning and brute-force attacks. It serves to fortify defenses against unauthorized remote access by pinpointing exploitable RDP flaws. The standout USP is its adaptive intelligence that learns from failed attempts to […]