Exploiter
Here you can find all types of Exploiter like , Remote Exploiters, Local Exploiters, Automated Exploit Kits, Web Exploiters, Hardware Exploiters, Social Engineering Exploiters.
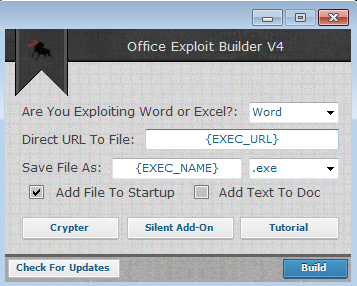
Office Exploit Builder Cracked 2025
Office Exploit Builder delivery has seen a resurgence in modern cyberattacks, with threat actors increasingly leveraging weaponized Office documents as their initial infection vector. The availability of sophisticated exploit builders has significantly simplified the process of creating malicious documents that can bypass security controls. Cracked versions of these tools circulating in underground forums have lowered […]
BIG EXPLOIT COLLECTION 2025
In the ever-evolving landscape of cyber threats, BIG EXPLOIT COLLECTION 2025 frameworks have become a favored weapon for both sophisticated threat actors and script kiddies alike. These Swiss Army knife-like toolkits dramatically lower the barrier to entry for cybercriminals by packaging hundreds of weaponized vulnerabilities with automated exploitation capabilities. The 2025 generation of these frameworks […]
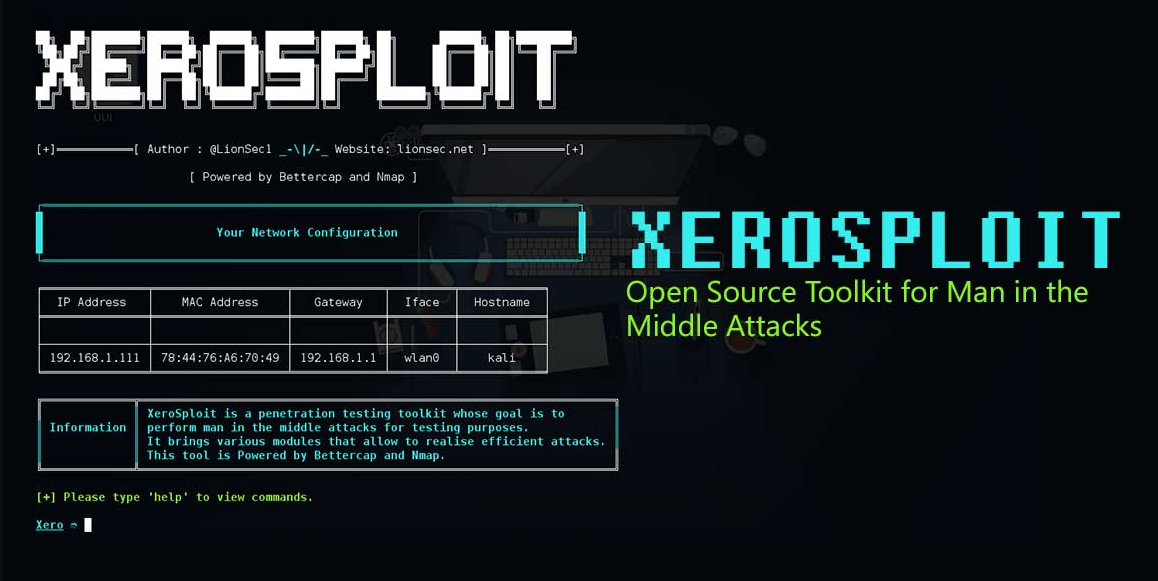
Xerosploit Toolkit 2025
Modern cyberattacks increasingly leverage sophisticated network penetration toolkits that automate man-in-the-middle (MITM) attacks and network exploitation. These frameworks have become particularly dangerous as they enable attackers to intercept, manipulate, and exploit network traffic with minimal technical expertise. When weaponised by malicious actors, Xerosploit Toolkit 2025 can facilitate credential theft, session hijacking, and malware distribution, while […]
Trillium Security MultiSploit Tool v6.5.21 Full
The cybersecurity landscape faces growing threats from sophisticated attack frameworks that bundle multiple exploitation capabilities into a single platform. These advanced Trillium Security MultiSploit lower the barrier to entry for cybercriminals by packaging professional-grade attack vectors with user-friendly interfaces. Particularly dangerous is their ability to automate complex attack chains combining reconnaissance, vulnerability exploitation, and post-compromise […]