Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Spynote v5.0
Spynote v5.0 is an advanced Remote Access Trojan (RAT) often analyzed by cybersecurity professionals to understand modern surveillance malware. While originally developed for penetration testing and ethical hacking research, it has been misused by threat actors for unauthorized access. This article explores its functionalities, ethical implications, and defensive measures. Download Link 1 Download Link 2 Download Link […]
Shadow Miner 2.0 with Tutorial
Shadow Miner 2.0 is a powerful, next-generation cryptocurrency mining tool designed for security researchers, penetration testers, and ethical hackers to analyze mining-related vulnerabilities. It provides advanced features for detecting, exploiting, and mitigating unauthorized cryptocurrency mining (cryptojacking) attacks on networks and web applications. This guide explores its functionalities, features, and ethical use cases. Download Link 1 […]
Poison Ivy 3.0.3 with Crypto Currencies Clipper
Poison Ivy 3.0.3 with Cryptocurrency Clipper module, now enhanced with an integrated represents a dangerous evolution in remote access malware. This hybrid threat combines the classic RAT’s powerful system control capabilities with real-time financial theft functionality, targeting both sensitive data and cryptocurrency transactions. The 2024 variant introduces AI-assisted evasion techniques and blockchain-based C2 infrastructure, making it particularly effective against […]
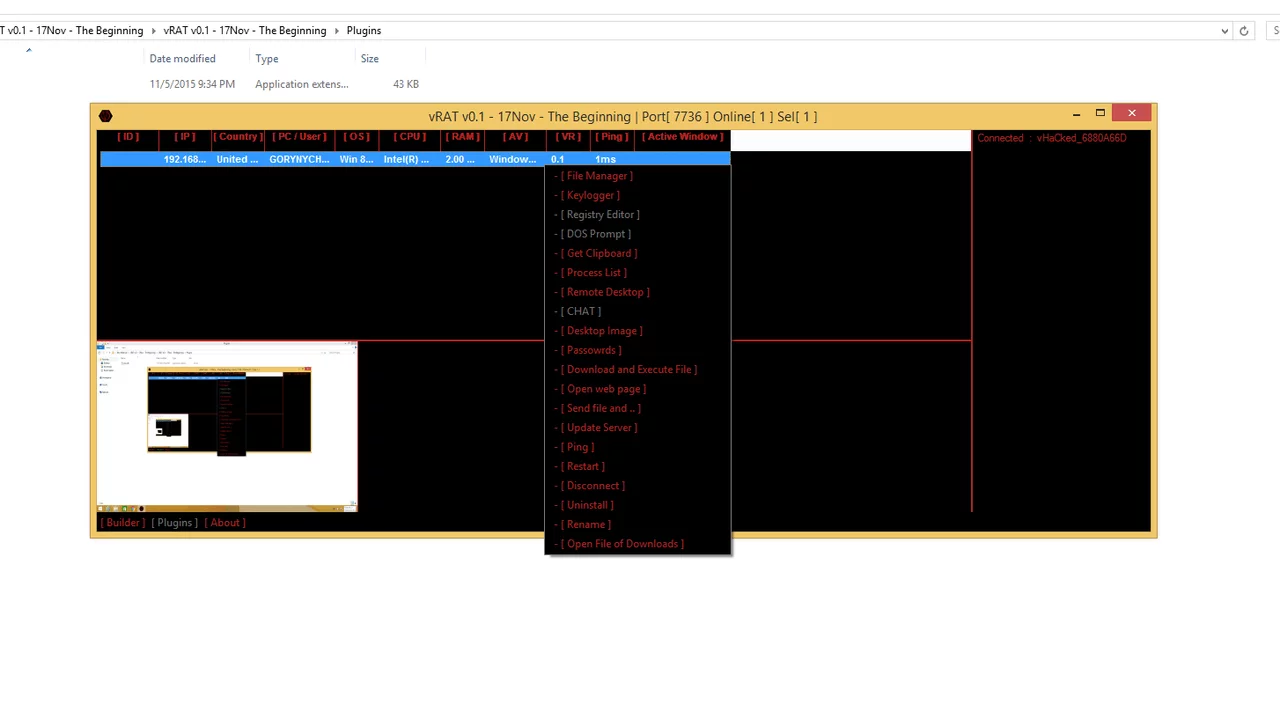
vRAT v0.1
vRAT v0.1 (Virtual Remote Access Trojan) is a newly emerging remote administration tool that has gained attention in cybersecurity circles. While it claims to be a legitimate remote management utility, its capabilities make it a preferred choice for hackers seeking unauthorized access to systems. With its lightweight design and modular approach, vRAT v0.1 poses a significant threat […]
Crypto Coin Stealr 2.0
Crypto Coin Stealr 2.0 is a sophisticated malware specifically engineered to target cryptocurrency wallets and exchanges, enabling hackers to steal private keys, seed phrases, and login credentials. This upgraded version introduces AI-driven target identification, enhanced evasion techniques, and cross-platform compatibility, making it one of the most dangerous threats to crypto investors in 2024. Its ability to operate stealthily while extracting high-value financial data […]
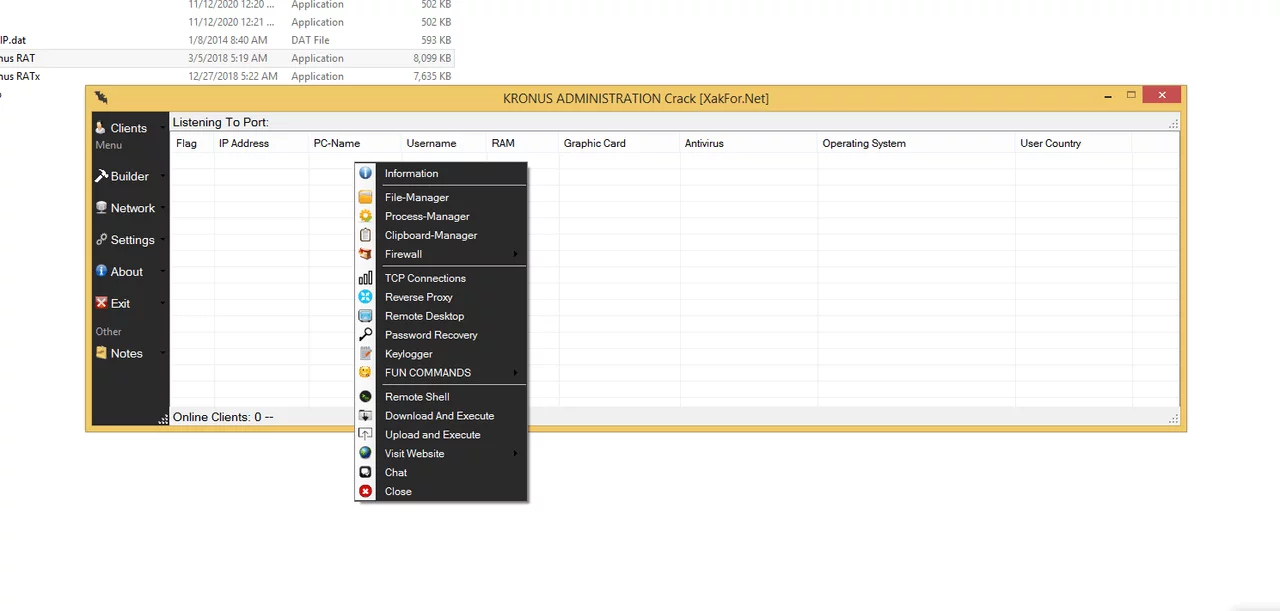
Kronus RAT 2024
Kronus RAT (Remote Access Trojan) is a powerful surveillance and remote-control tool that emerged in 2024. While marketed as a legitimate remote administration tool, it is often exploited by hackers for unauthorized access, data theft, and system manipulation. Its advanced evasion techniques and modular design make it a significant threat in cybersecurity. What is Kronus […]
LuxNET RAT Cracked 2024
LuxNET RAT Cracked 2024 is a pirated version of a premium remote administration tool circulating in hacker forums, offering unauthorized remote system access without licensing restrictions. This cracked variant retains the original malware’s powerful surveillance capabilities while incorporating custom obfuscation techniques and enhanced persistence mechanisms, making it particularly dangerous for both personal privacy and enterprise security. The 2024 […]
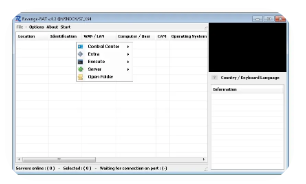
Revenge RAT V 0.2 with Tutorial
Revenge RAT v0.2 with tutorial is a next-generation Remote Access Trojan designed for covert system infiltration and persistent control. This lightweight yet powerful tool combines fileless execution, advanced evasion techniques, and modular plugin support, making it a significant threat to both individual users and enterprise networks. Bundled with a detailed tutorial, Revenge RAT v0.2 enables even less experienced hackers […]
MobiHok V4 with Tutorial
MobiHok V4 is a sophisticated Android Remote Access Trojan (RAT) that enables complete device control through stealthy, persistent access. This latest version introduces enhanced evasion techniques, AI-driven target profiling, and automated data exfiltration, making it one of the most dangerous mobile threats in 2024. Bundled with a comprehensive tutorial, MobiHok V4 allows even novice hackers to deploy advanced surveillance operations, […]
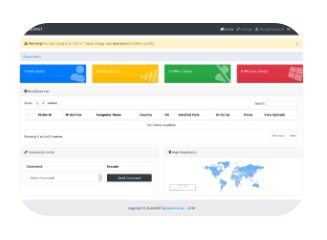
BlackNET v1.0
BlackNET v1.0 is a sophisticated botnet-as-a-service (BaaS) platform emerging in underground cybercrime forums, offering hackers a modular, customizable infrastructure for large-scale attacks. This next-generation framework combines AI-driven target selection, blockchain-based C2 resilience, and polymorphic malware generation to create an exceptionally stealthy and persistent threat. Designed for DDoS campaigns, credential harvesting, and cryptojacking operations, BlackNET represents a significant escalation in automated cyber […]