Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
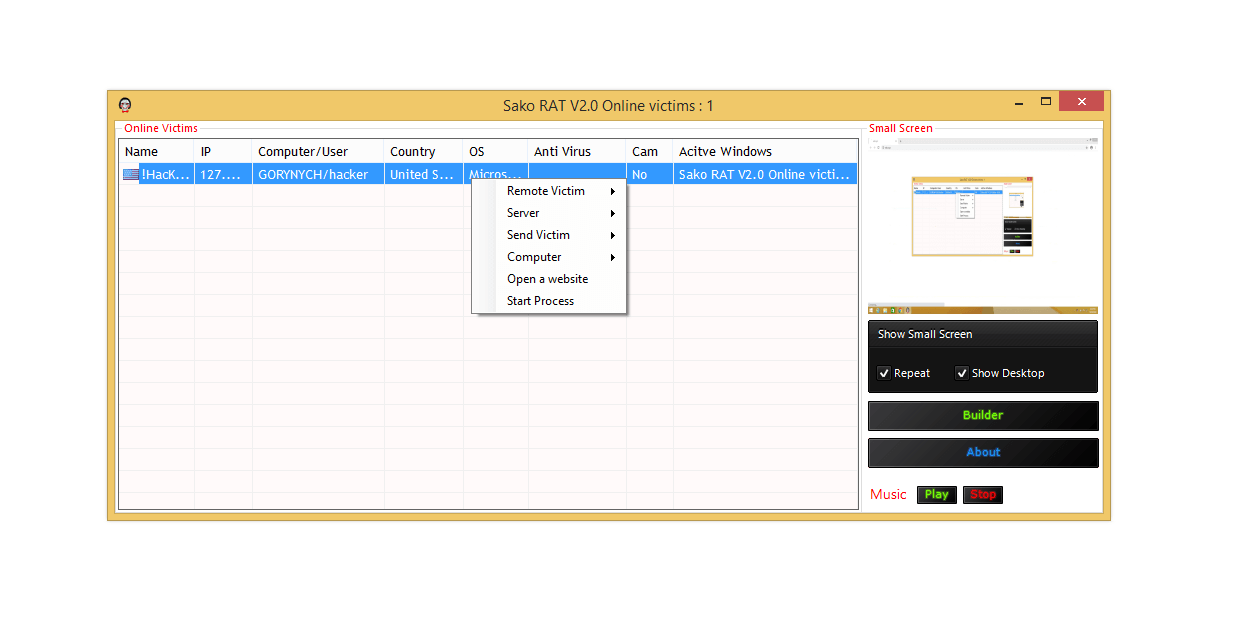
Sako RAT v2.0
Sako RAT v2.0 is a cutting-edge Remote Access Trojan that has emerged as a significant threat in 2024, building upon its predecessor with enhanced stealth, modularity, and evasion capabilities. Named after its developer “Sako,” this RAT distinguishes itself through military-grade encryption, AI-driven behavior adaptation, and multi-platform targeting. Its ability to mimic legitimate network traffic and […]
Awesome Miner 7.3 + Patch
Awesome Miner 7.3 + Patch is a modified version of a legitimate cryptocurrency mining management tool. While the original software is designed for efficient mining operations, the patched version bypasses licensing restrictions, making it a subject of interest for cybersecurity researchers. This article examines its features from a defensive security perspective, focusing on malware analysis, unauthorized mining […]
Sseur Keyloger 2024
Sseur Keyloger 2024 is an advanced keystroke logging tool frequently analyzed in cybersecurity research to understand modern data-exfiltration techniques. While keyloggers have legitimate uses (e.g., parental controls or employee monitoring), unauthorized deployment constitutes a severe privacy violation. This guide explores its functionalities strictly for ethical hacking, malware analysis, and defensive cybersecurity purposes. Download Link 1 Download Link […]
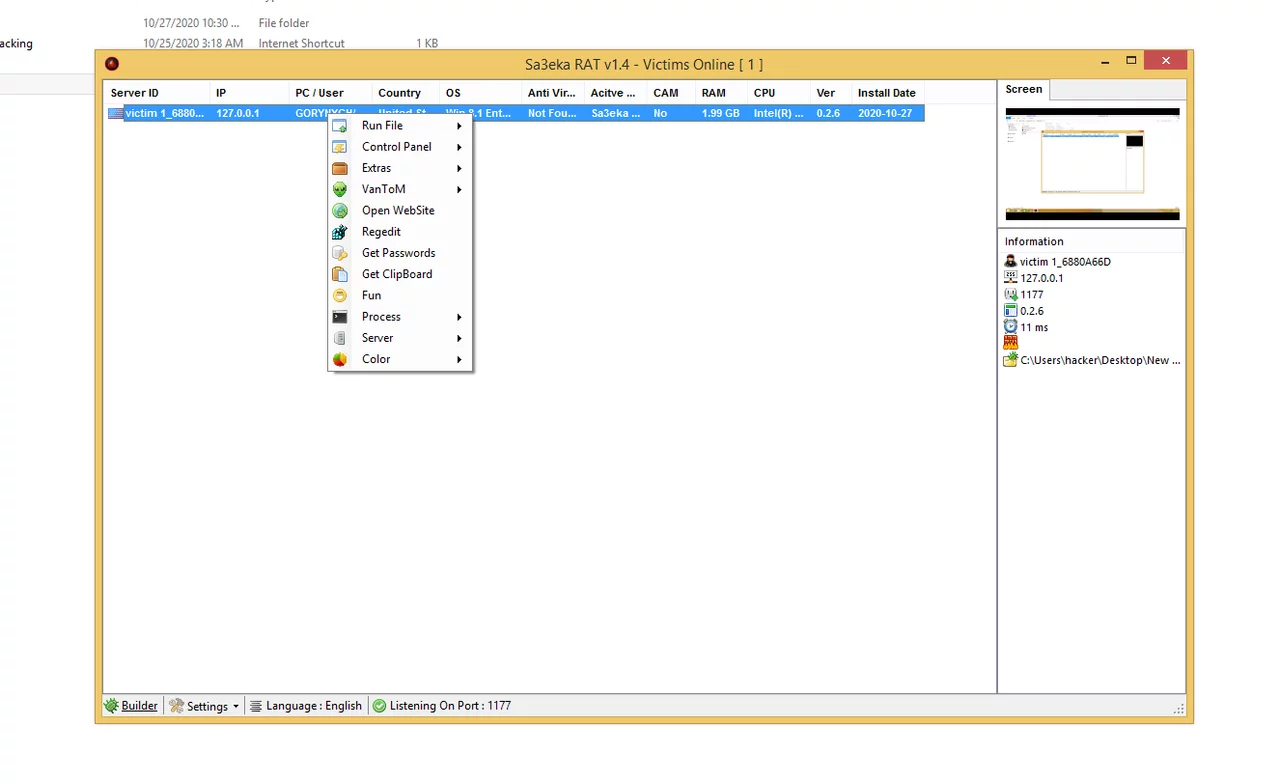
Sa3eka RAT v1.4
Sa3eka RAT v1.4 is an emerging remote access trojan that first appeared in underground hacking forums in early 2024. Designed for persistent surveillance and data exfiltration, this Arabic-origin malware (“Sa3eka” meaning “hunter”) has quickly gained popularity among sophisticated threat actors due to its unique evasion techniques and multi-vector attack capabilities. Unlike conventional RATs, version 1.4 […]
Napoleon Monitor v1.3 Cracked
Napoleon Monitor v1.3 (Cracked) is a modified version of a commercial monitoring tool often examined in cybersecurity research. While originally designed for legitimate surveillance purposes (e.g., parental control or employee monitoring), its cracked variant is frequently misused by threat actors for unauthorized access. This article explores its functionalities from a defensive cybersecurity perspective, emphasizing ethical hacking and malware […]
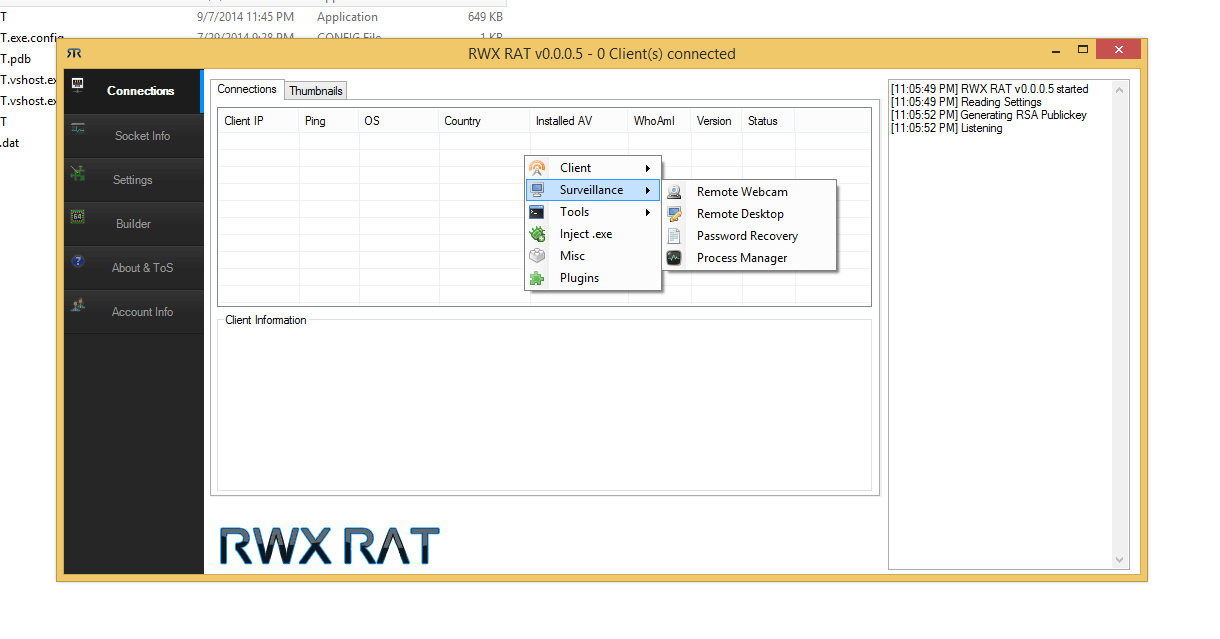
RWX Rat 2024
RWX RAT (Read-Write-Execute Remote Access Trojan) 2024 represents the latest evolution in sophisticated malware, combining advanced penetration techniques with unprecedented stealth capabilities. Emerging in early 2024, this Windows-based threat has quickly gained notoriety among cybersecurity professionals due to its modular architecture and ability to bypass modern security measures. Unlike traditional RATs, RWX 2024 employs innovative […]
Spynote v5.0
Spynote v5.0 is an advanced Remote Access Trojan (RAT) often analyzed by cybersecurity professionals to understand modern surveillance malware. While originally developed for penetration testing and ethical hacking research, it has been misused by threat actors for unauthorized access. This article explores its functionalities, ethical implications, and defensive measures. Download Link 1 Download Link 2 Download Link […]
Shadow Miner 2.0 with Tutorial
Shadow Miner 2.0 is a powerful, next-generation cryptocurrency mining tool designed for security researchers, penetration testers, and ethical hackers to analyze mining-related vulnerabilities. It provides advanced features for detecting, exploiting, and mitigating unauthorized cryptocurrency mining (cryptojacking) attacks on networks and web applications. This guide explores its functionalities, features, and ethical use cases. Download Link 1 […]
Poison Ivy 3.0.3 with Crypto Currencies Clipper
Poison Ivy 3.0.3 with Cryptocurrency Clipper module, now enhanced with an integrated represents a dangerous evolution in remote access malware. This hybrid threat combines the classic RAT’s powerful system control capabilities with real-time financial theft functionality, targeting both sensitive data and cryptocurrency transactions. The 2024 variant introduces AI-assisted evasion techniques and blockchain-based C2 infrastructure, making it particularly effective against […]
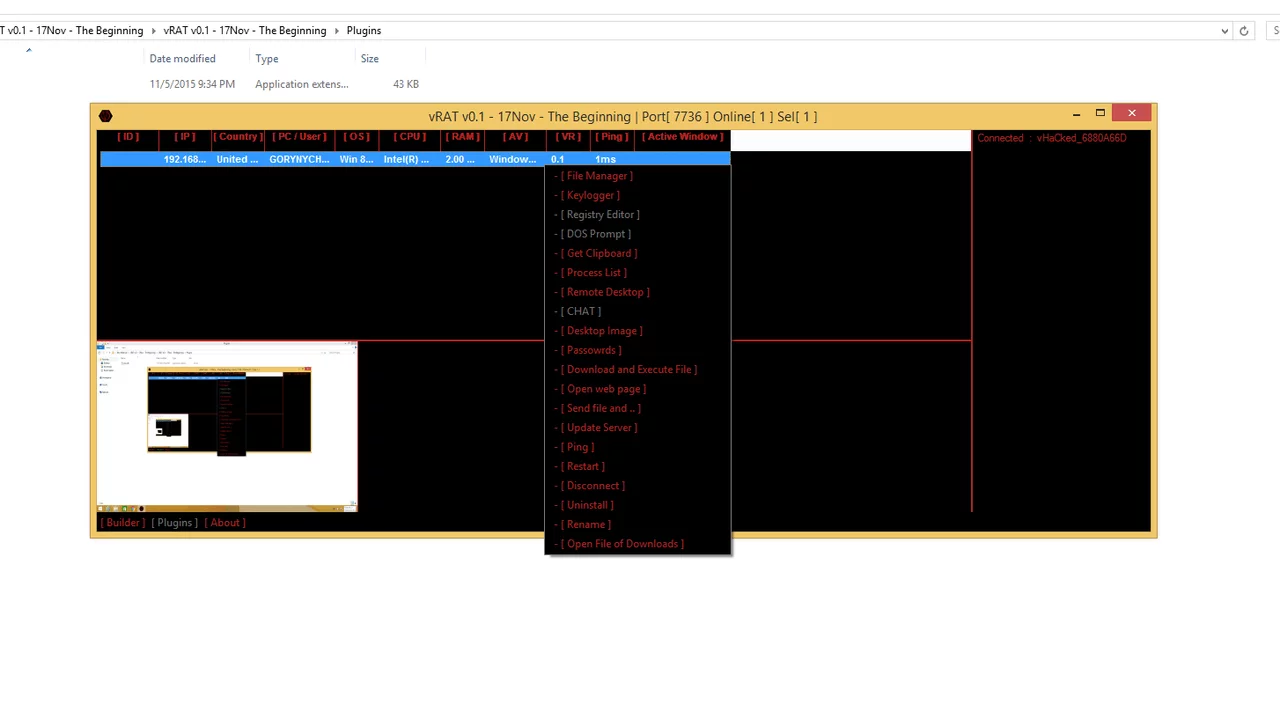
vRAT v0.1
vRAT v0.1 (Virtual Remote Access Trojan) is a newly emerging remote administration tool that has gained attention in cybersecurity circles. While it claims to be a legitimate remote management utility, its capabilities make it a preferred choice for hackers seeking unauthorized access to systems. With its lightweight design and modular approach, vRAT v0.1 poses a significant threat […]