Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
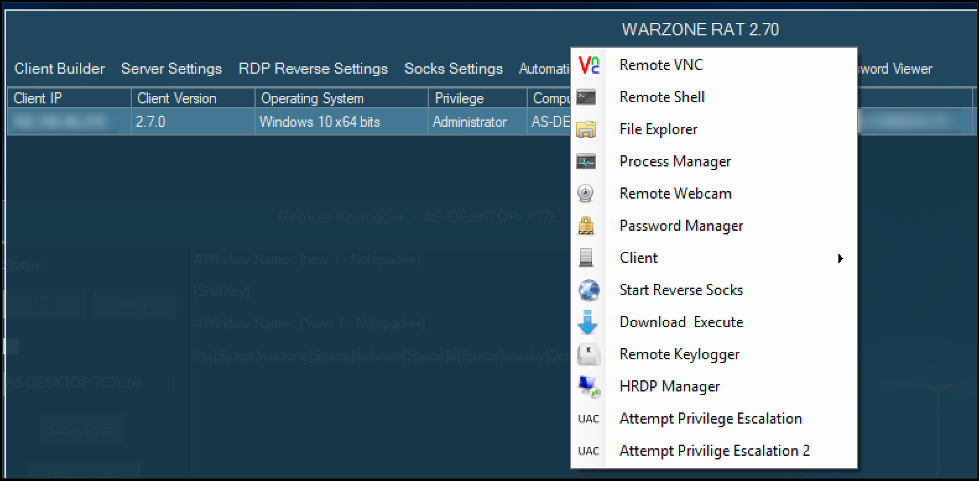
WarZone RAT 3.03 Cracked
In the ever-evolving landscape of cyber threats, Remote Access Trojans (RATs) continue to be a weapon of choice for malicious actors seeking unauthorized access to sensitive systems. The availability of cracked versions of commercial RATs on underground forums has significantly lowered the barrier to entry, enabling even low-skilled attackers to deploy sophisticated surveillance and data […]
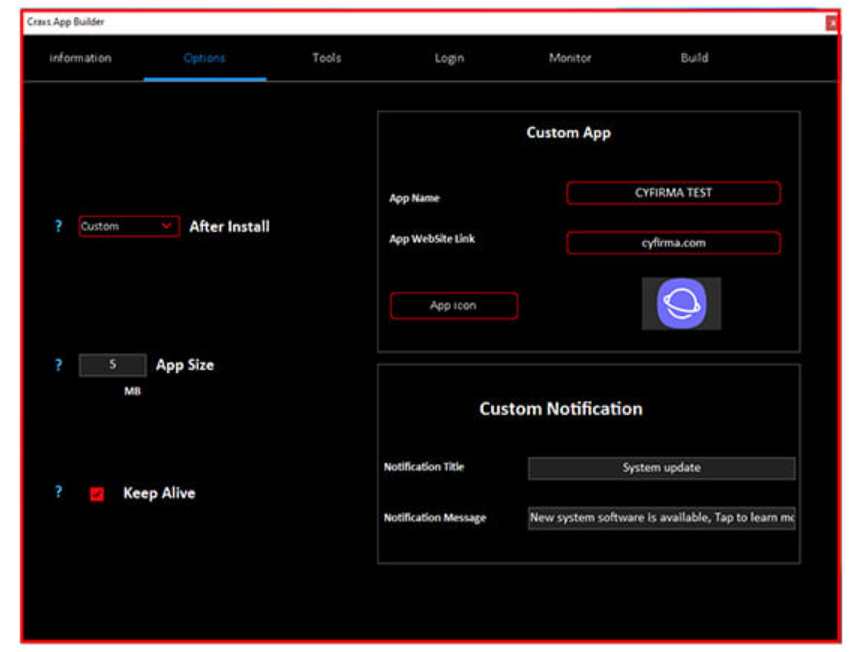
Shark Crypto Clipper 2025
In the evolving landscape of cyber threats, malicious tools designed to hijack cryptocurrency transactions have become increasingly sophisticated. One such tool, emerging in 2025, exemplifies this trend by targeting users during financial transactions, silently altering wallet addresses to divert funds to attackers. Shark Crypto Clipper is a type of malware, often referred to as a […]
Eagle Monitor RAT Reborn V3.2.2.0
Remote Access Trojans (RATs) remain one of the most dangerous tools in a cybercriminal’s arsenal, enabling complete control over compromised systems. Modern variants, often distributed through underground forums and illicit marketplaces, have evolved to include advanced evasion techniques and modular capabilities. Eagle Monitor RAT Reborn is frequently used in targeted attacks against businesses, government entities, […]
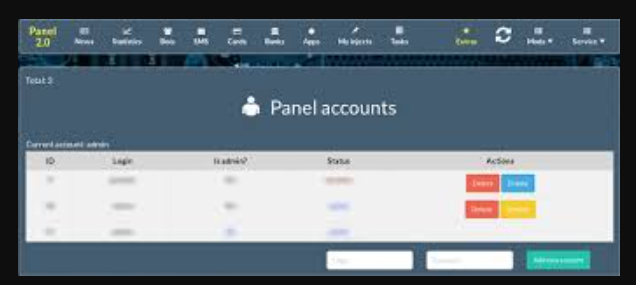
Exobot 2.5 Trump Edition
Cybercriminals continuously evolve their tools to bypass security measures and maximize their illicit gains. Among these threats, advanced banking trojans have emerged as a significant risk, particularly those distributed through underground markets in cracked or modified forms. Exobot 2.5 variants are often designed to steal financial data, automate fraudulent transactions, and evade detection—making them a […]
Falcon Keylogger 2025 Cracked
The threat landscape continues to evolve with increasingly sophisticated surveillance tools, and Falcon Keylogger 2025 Cracked has emerged as one of the most dangerous information-stealing malware variants in modern cyberattacks. This advanced keylogging software demonstrates how cybercriminals are leveraging cracked commercial spyware to conduct large-scale credential theft campaigns. Falcon Keylogger 2025 Cracked has been actively […]
CatLogs Stealer 2025
Cybercriminals are increasingly relying on information-stealing malware to harvest sensitive data, including login credentials, financial details, and personal documents. For example, CatLogs Stealer 2025 represents a sophisticated new strain that efficiently extracts data from infected machines while evading security measures. These malicious tools play a pivotal role in credential theft, financial fraud, and espionage campaigns, often serving […]
Prynt Stealer Cracked 2024
Cybercriminals increasingly rely on stealthy and efficient malware to carry out data theft, financial fraud, and espionage. Among these threats, information stealers have become a preferred tool due to their ability to harvest sensitive data with minimal detection. Prynt Stealer 2024 further lowers the barrier to entry, enabling even less skilled attackers to deploy sophisticated […]
XWORM V2.1 CRACKED
The proliferation of cracked malware variants has become a significant concern in the cybersecurity landscape, with threat actors increasingly leveraging pirated versions of sophisticated attack tools to lower operational costs while maintaining high effectiveness. Among these, a particularly dangerous cracked specimen has emerged as a favorite among cybercriminals due to its modular design and robust […]
Remote Hacker Probe Pro v2
The cybersecurity landscape faces growing threats from sophisticated penetration tools, with Remote Hacker Probe Pro V.2 emerging as a particularly dangerous weapon in modern cyberattacks. This advanced remote access toolkit demonstrates how cybercriminals are professionalizing their operations with feature-rich, commercially inspired hacking software. Remote Hacker Probe Pro V.2 has been actively used in targeted attacks […]
ICARUS RAT 2025 Cracked
The underground market for cracked remote access trojans (RATs) continues to thrive, providing cybercriminals with powerful surveillance tools at minimal cost. Among these offerings, a particularly dangerous cracked variant has emerged in 2025, combining professional-grade remote administration features with malicious capabilities optimized for covert operations. ICARUS RAT 2025 demonstrates how threat actors are leveraging pirated […]