Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
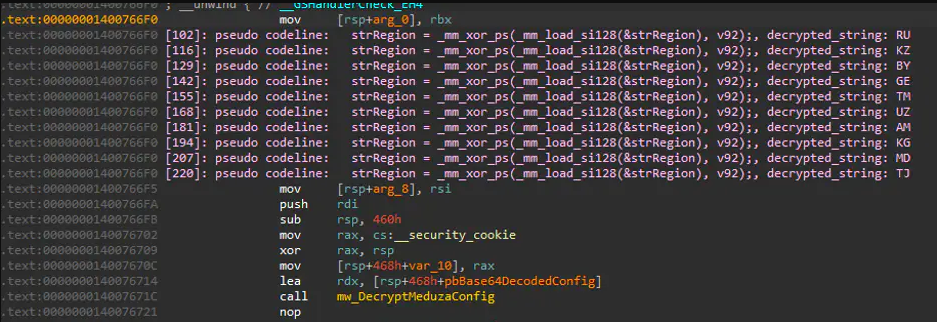
COSMO STEALER 2025
The evolution of information stealers has reached new heights in 2025, with modern variants demonstrating unprecedented sophistication in data harvesting and evasion techniques. Among these threats, a particularly advanced strain has emerged as a favorite of cybercriminals due to its modular design, broad targeting capabilities, and robust anti-detection mechanisms. COSMO STEALER 2025 exemplifies the current […]
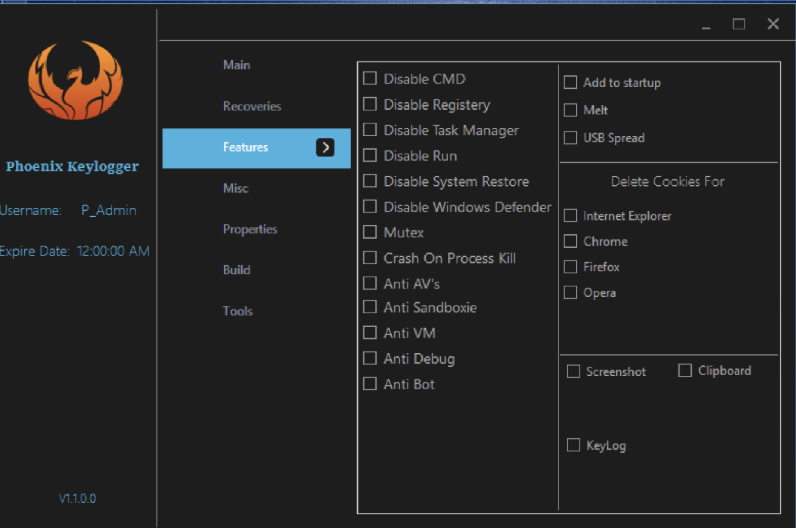
Poenix Keylogger 2025 Cracked
Cyberattacks have evolved significantly in recent years, with keyloggers remaining a persistent threat due to their ability to capture sensitive user data stealthily. Among these, cracked versions of keylogging software—often distributed illegally—pose an even greater risk, as they bypass security measures and licensing restrictions, making them attractive tools for malicious actors. Poenix Keylogger 2025 tools […]
Shinobu Clipper 2025
Cryptocurrency-focused malware has become increasingly prevalent in the cybercrime ecosystem, with clipboard hijackers emerging as one of the most effective tools for stealing digital assets. These specialized malware strains operate by silently monitoring and modifying clipboard contents, allowing attackers to divert cryptocurrency transactions to their wallets. The 2025 iteration of these clippers demonstrates enhanced sophistication, […]
Man Clipper 2025 Cracked
The cryptocurrency ecosystem faces a growing threat from sophisticated clipboard hijacking malware, with Man Clipper 2025 Cracked emerging as one of the most dangerous tools for intercepting digital currency transactions. This advanced malware variant demonstrates how cybercriminals are refining their techniques to target cryptocurrency users with surgical precision. Man Clipper 2025 Cracked has been actively […]
Hack Pack 2025
The cybersecurity threat landscape has seen a surge in all-in-one attack toolkits that bundle multiple malicious capabilities into a single package. These comprehensive suites lower the barrier to entry for cybercriminals by providing ready-made tools for various attack vectors. Particularly concerning is their modular design, which allows even novice attackers to launch sophisticated campaigns with […]
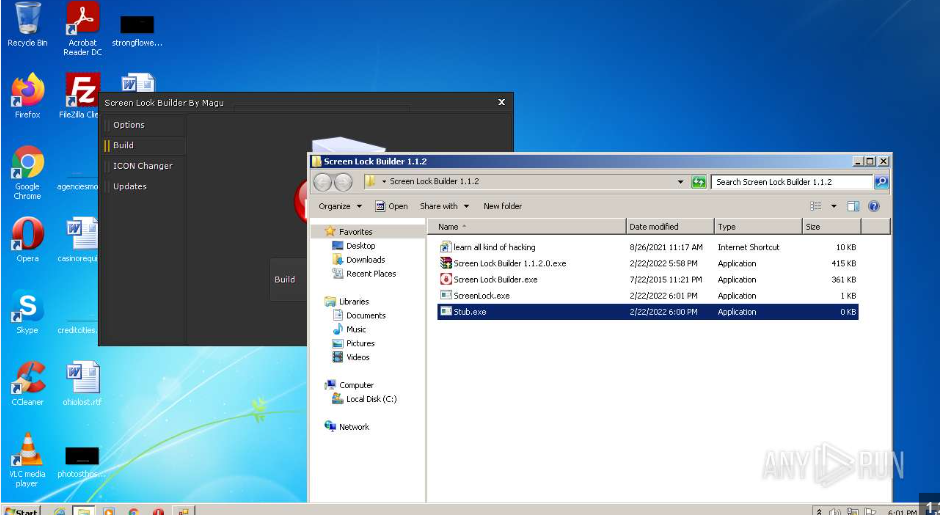
Screen Lock Builder 1.1.2.0
In recent years, cybercriminals have increasingly turned to specialized tools to enhance the effectiveness of their attacks. One such tool, often distributed through malicious campaigns, is designed to lock users out of their systems while demanding payment for restoration. Screen Lock Builder attacks, commonly categorized as ransomware or screen locker threats, disrupt productivity and extort […]
StormKitty Stealer 2025
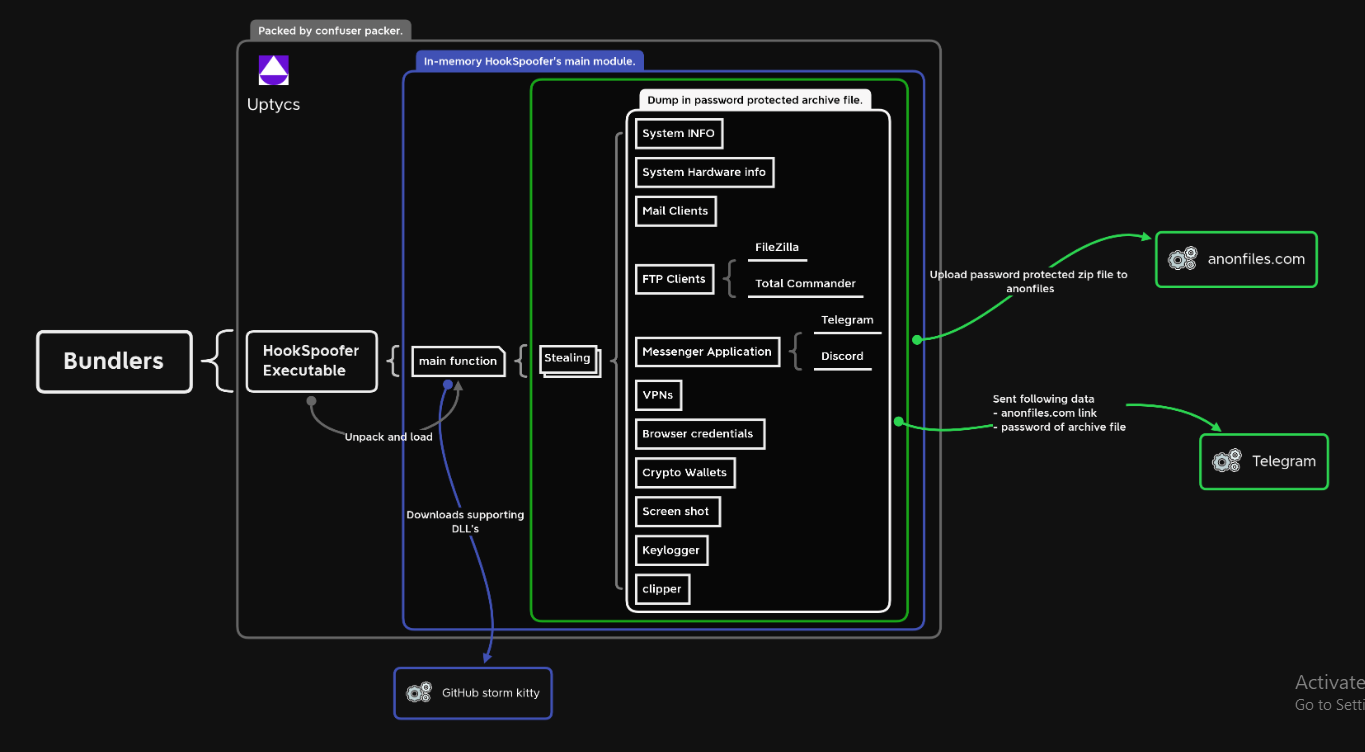
In the ever-evolving landscape of cyber threats, information stealers have become one of the most prevalent and damaging tools in an attacker’s arsenal. These specialized malware variants are designed to covertly harvest sensitive data from infected systems, often leading to financial fraud, identity theft, and corporate espionage. The latest iterations of these stealers demonstrate increasing […]
Mars Stealer v3 Cracked
The cybersecurity landscape faces an escalating threat from sophisticated information stealers, with Mars Stealer v3 Cracked emerging as one of the most dangerous tools in modern credential harvesting campaigns. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful attack tools at minimal cost. Mars Stealer v3 Cracked […]
Cypher Rat 2025 cracked
In recent years, cybercriminals have increasingly relied on sophisticated information-stealing malware to compromise sensitive data. One such tool, often referred to as “X-FILES STEALER 2025,” has gained notoriety for its ability to evade detection while exfiltrating credentials, financial data, and other valuable information. These stealers are frequently distributed through phishing campaigns, malicious downloads, or exploit […]
SpyMax 4 RAT Cracked
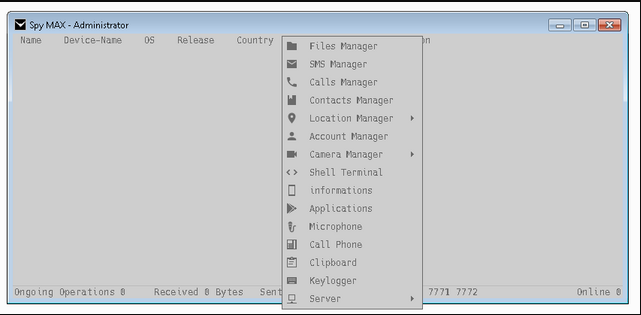
Cybercriminals increasingly rely on commercially available spyware tools to conduct surveillance and data theft operations. Among these threats, cracked or pirated versions of legitimate monitoring software pose a significant risk, as they are often repurposed for malicious activities. SpyMax 4 RAT provides attackers with powerful capabilities while evading legal restrictions, making them attractive for unauthorized […]