Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Twilight Stealer 2024
Twilight Stealer 2024 is a sophisticated information-stealing malware designed to extract sensitive data from compromised systems. Unlike traditional stealers, it employs advanced evasion techniques, targeting browsers, cryptocurrency wallets, FTP clients, and more. Its modular architecture and regular updates make it a persistent threat in the cybersecurity landscape. Download Link 1 Download Link 2 Download Link […]
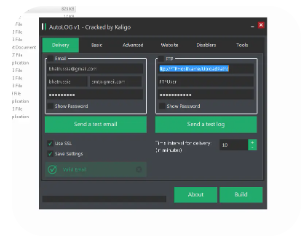
AutoLOG Keylogger 2024
AutoLOG Keylogger 2024 represents the latest evolution in stealthy keystroke monitoring tools, combining traditional logging functions with advanced evasion techniques. This sophisticated keylogger demonstrates concerning capabilities for capturing sensitive user input while avoiding standard detection methods. Cybersecurity professionals study AutoLOG to develop stronger defensive measures against unauthorized surveillance and credential theft. Download Link 1 Download Link […]
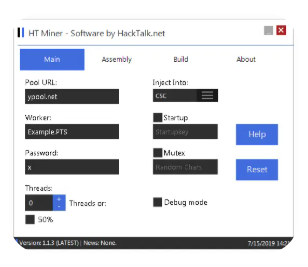
hMinerPTS Bitcoin Miner 2024
hMinerPTS is a sophisticated cryptojacking malware that surfaced in 2024, targeting Windows and Linux systems to mine Bitcoin without user consent. This stealthy miner utilizes advanced evasion techniques to avoid detection while maximizing computational power for illicit cryptocurrency mining. Cybersecurity researchers analyze hMinerPTS to develop better detection methods and protect systems from unauthorized resource hijacking. Download […]
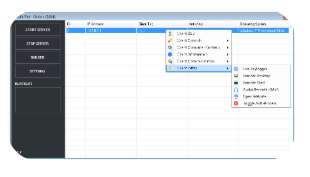
VanillaRat 1.7
VanillaRAT 1.7 has emerged as a sophisticated Remote Access Trojan (RAT) with enhanced capabilities for stealthy system infiltration and persistent control. This latest version demonstrates significant improvements in evasion techniques, data exfiltration methods, and plugin-based functionality. While cybersecurity professionals study it to strengthen defensive measures, unauthorized deployment remains illegal and poses severe risks to personal and […]
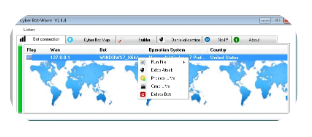
Cyber Bot-Worm V1.0.4
Cyber Bot-Worm V1.0.4 represents a dangerous evolution in malware, combining the self-replicating capabilities of a worm with the remote control functionality of a botnet. This hybrid threat demonstrates sophisticated propagation techniques, encrypted command-and-control (C2) communication, and modular payload delivery. While cybersecurity researchers study it to develop stronger defenses, unauthorized deployment constitutes a serious violation of computer […]
Lime-Worm-0.5.8D
Lime-Worm 0.5.8D is a sophisticated self-replicating malware strain that combines worm-like propagation with remote access capabilities. This latest version demonstrates significant improvements in evasion techniques, persistence mechanisms, and network-based spreading. While ethical researchers analyze it to develop stronger cybersecurity defenses, unauthorized deployment remains illegal and poses severe risks to network security. Download Link 1 Download Link […]
BlackWorM v6.0
BlackWorM v6.0 is a sophisticated malware strain that has gained attention in cybersecurity circles due to its modular design and evasion capabilities. While originally developed as a Remote Access Trojan (RAT), its latest iteration includes enhanced features for persistence, data exfiltration, and anti-analysis. Security researchers study BlackWorM v6.0 to develop stronger defensive measures, while unauthorized deployment remains illegal […]
Spectral Rat Cracked 2024
The cybersecurity community has observed increased activity surrounding Spectral RAT, a sophisticated remote access tool that surfaced in underground forums. The 2024 cracked version represents a leaked or reverse-engineered variant that security researchers are analyzing to understand its capabilities and develop countermeasures. This article examines its technical features, potential defensive applications, and the importance of ethical research in […]
Asacube Android banking Botnet 2024
The Asacube banking botnet has emerged as one of the most sophisticated mobile threats in 2024, specifically targeting financial applications on Android devices. This advanced malware demonstrates the evolving capabilities of mobile banking Trojans, combining traditional botnet functionality with financial fraud techniques. Security researchers study this threat to develop better protections for mobile banking ecosystems. […]
Lordix botnet Cracked 2024
The Lordix Botnet has emerged as a sophisticated threat in 2024, leveraging advanced evasion techniques to control infected systems. While malicious actors exploit it for DDoS attacks, credential theft, and crypto-mining, cybersecurity researchers analyze cracked versions to develop countermeasures. This article examines Lordix Botnet Cracked 2024, its functionalities, and ethical applications in threat intelligence. Download Link 1 Download Link […]