Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
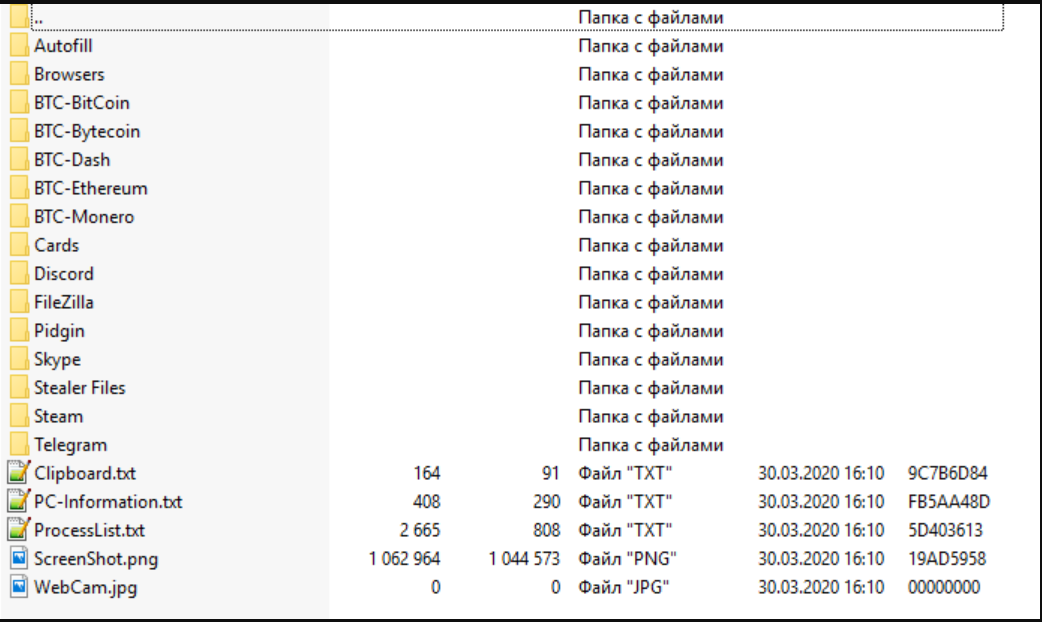
Poulight Stealer cracked
Poulight Stealer is a potent information-stealing malware designed to extract sensitive data from infected systems. The cracked version, widely circulated in underground forums, provides unauthorized access to its premium features without payment. While its use is illegal and poses significant cybersecurity risks, understanding its capabilities is essential for defense and awareness. Download Link 1 Download […]
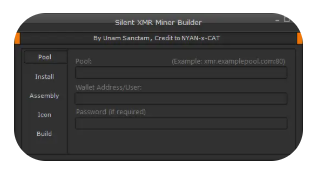
Silent XMR Miner Builder v0.2+Tutorial
Silent XMR Miner Builder v0.2 is a powerful cryptocurrency miner generator designed to create undetectable Monero (XMR) mining payloads. This tool enables hackers to covertly hijack system resources for profit, using advanced evasion techniques to avoid detection by antivirus and endpoint protection. The included tutorial simplifies deployment, making cryptojacking accessible even to less experienced threat actors. With […]
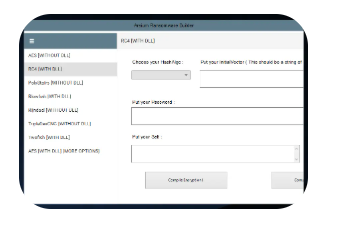
Arsium Ransomware Builder 2024
Arsium Ransomware Builder 2024 represents a dangerous evolution in ransomware development tools, enabling even novice hackers to create customized ransomware strains with minimal technical knowledge. This point-and-click software package generates fully functional ransomware executables with sophisticated encryption, evasion techniques, and built-in cryptocurrency payment systems. The 2024 version introduces polymorphic code generation, expanded target selection options, […]
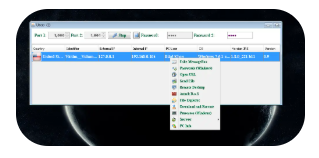
Predator Pain Keylogger v13
Predator Pain Keylogger v13 represents the latest evolution in stealthy surveillance malware, combining traditional keylogging with modern data exfiltration techniques. This sophisticated tool captures every keystroke, screen activity, and system interaction while remaining virtually undetectable by most security solutions. Its 2024 update introduces enhanced anti-analysis capabilities, expanded browser targeting, and improved persistence mechanisms, making it […]
Galaxy logger 2024
Galaxy Logger 2024 is a sophisticated information-stealing malware designed to harvest credentials, financial data, and system information with unprecedented efficiency. This advanced keylogger and data stealer targets browsers, cryptocurrency wallets, and authentication tokens, using cutting-edge evasion techniques to bypass security measures. Its modular architecture and regular updates make it a persistent threat in the cybersecurity landscape. […]
Frutas rat english 2024
Frutas RAT English 2024 is an emerging Remote Access Trojan that has gained notoriety for its lightweight design and effective evasion capabilities. Originally developed in Spanish-speaking hacking communities, this English version now poses a global threat with improved functionality. Unlike more complex RATs, Frutas maintains a low profile while providing comprehensive system control, making it particularly dangerous […]
Mega RAT 1.5 Beta
Mega RAT 1.5 Beta is an advanced Remote Access Trojan (RAT) designed to provide hackers with complete, undetected control over compromised systems. This latest version introduces enhanced evasion techniques, expanded surveillance capabilities, and improved command-and-control (C2) communication. Targeting both Windows and Android devices, Mega RAT 1.5 Beta poses a significant threat to personal privacy and enterprise […]
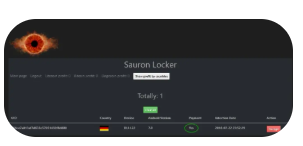
Sauron Locker 2024
Sauron Locker 2024 represents a significant leap in ransomware sophistication, combining advanced encryption methods with stealthy infiltration techniques. This malware variant targets both individual users and enterprise networks, employing a double-extortion model that encrypts files while exfiltrating sensitive data. Its modular design and polymorphic code make it particularly resistant to traditional security measures, posing a […]
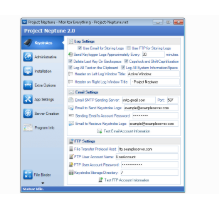
Project Neptune v2.0
Project Neptune v2.0 is a sophisticated credential-harvesting malware designed to stealthily collect sensitive login information from compromised systems. Built with modular architecture and advanced evasion techniques, it primarily targets web browsers, email clients, and financial applications. Its ability to bypass security measures while remaining undetected makes it a significant threat in the cybersecurity landscape. Download Link […]
LimeStealer 2024
LimeStealer 2024 is a cutting-edge information-stealing malware designed to extract sensitive data from infected systems with high efficiency. Known for its stealthy operation and modular design, it targets browsers, cryptocurrency wallets, gaming credentials, and financial applications. Its evolving evasion techniques make it a significant threat in cybersecurity. Download Link 1 Download Link 2 Download Link […]