Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
Arkei Stealer Cracked 2025
In the rapidly evolving landscape of cybercrime, information-stealing malware has become one of the most pervasive and damaging threats. Among these threats, a particularly sophisticated data theft tool has emerged as a favorite among cybercriminals due to its modular design and comprehensive stealing capabilities. Arkei Stealer Cracked 2025 has been actively involved in credential theft campaigns, […]
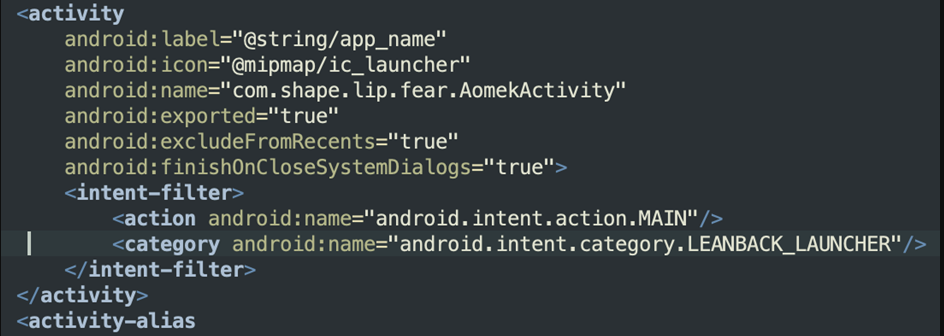
AdBot Android Spying 2025
The mobile security landscape faces growing threats from sophisticated surveillance tools, with AdBot Android Spying 2025 emerging as a particularly dangerous example of modern spyware. This advanced malware variant demonstrates how cybercriminals are weaponizing seemingly legitimate ad-serving technology for covert surveillance operations. Adbot Android Spying 2025 has been implicated in numerous privacy breaches, showing how […]
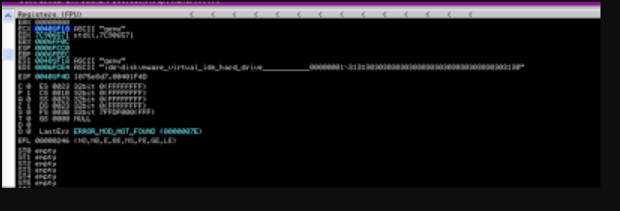
Smoke Loader Botnet 2025 Cracked
The cyber threat landscape continues to evolve with increasingly sophisticated malware delivery systems, and among these, a particularly resilient loader has established itself as a critical enabler for modern cyberattacks. This Smoke Loader Botnet 2025, first observed several years ago, has undergone numerous iterations to maintain its effectiveness against security defenses. Acting as a gateway […]
Clipper Morphine 2025 Cracked
The cryptocurrency ecosystem faces growing threats from sophisticated malware, with Clipper Morphine 2025 emerging as a particularly dangerous evolution of clipboard hijacking malware. This advanced threat demonstrates how cybercriminals are adapting traditional attack methods to target digital asset transactions specifically. Clipper Morphine has been implicated in numerous high-value cryptocurrency thefts, showcasing how simple clipboard manipulation […]
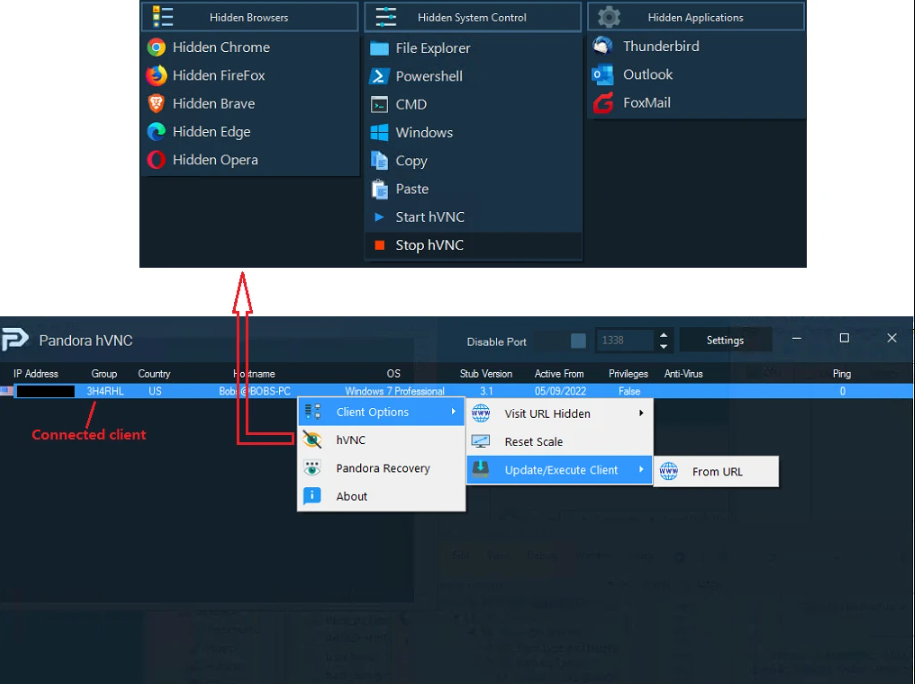
BitRAT HVNC RAT 2025 Cracked with Source code
In the evolving landscape of cyber threats, remote access trojans (RATS) remain a persistent and dangerous tool for attackers. These malicious programs enable unauthorized access to compromised systems, allowing cybercriminals to steal sensitive data, deploy additional malware, or maintain long-term persistence within a network. Among these threats, advanced RATS with features like Hidden Virtual Network […]
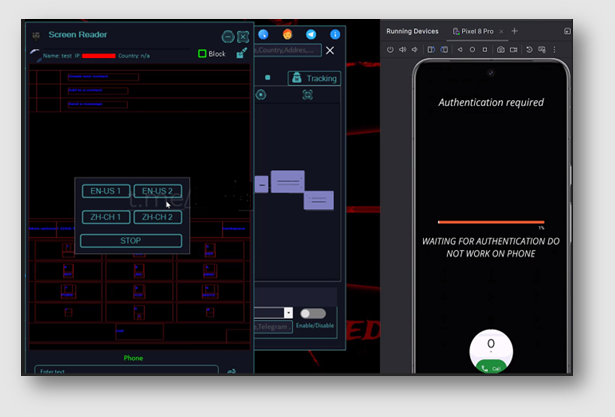
Eagle Monitor RAT Reborn 2025
In 2025, the resurgence of advanced Remote Access Trojans (RATs) has introduced a new wave of sophisticated cyber threats, with modern variants demonstrating unprecedented stealth and functionality. These evolved surveillance tools have become weapons of choice for both cybercriminals and state-sponsored actors, enabling complete device takeover while evading traditional security measures. Eagle Monitor RAT Reborn […]
CERBERUS V4 Cracked
The Android banking malware landscape has become increasingly dangerous with the emergence of CERBERUS V4 Cracked, a sophisticated variant that demonstrates how cybercriminals are adapting commercial malware tools for widespread attacks. This advanced banking trojan has been actively used in campaigns targeting financial institutions and their customers worldwide, showcasing its ability to bypass modern security […]
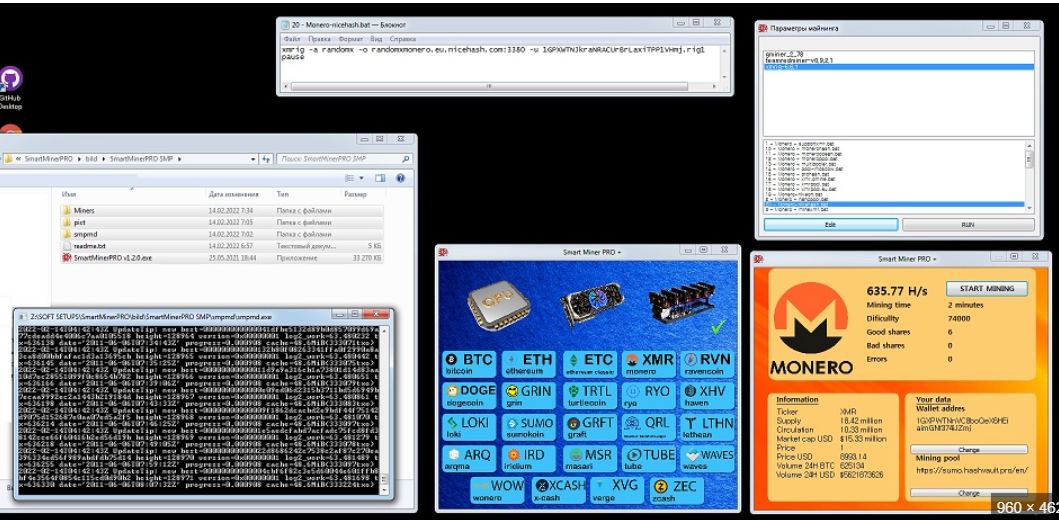
Silent Crypto Miner V 2.0.2
In the evolving landscape of cyber threats, cryptojacking has emerged as a lucrative and stealthy attack vector. One such tool, often referred to as Silent Crypto Miner V 2.0.2, exemplifies the growing sophistication of malicious mining software. Unlike traditional malware, which disrupts systems or steals data, this tool operates covertly, hijacking computing resources to mine […]
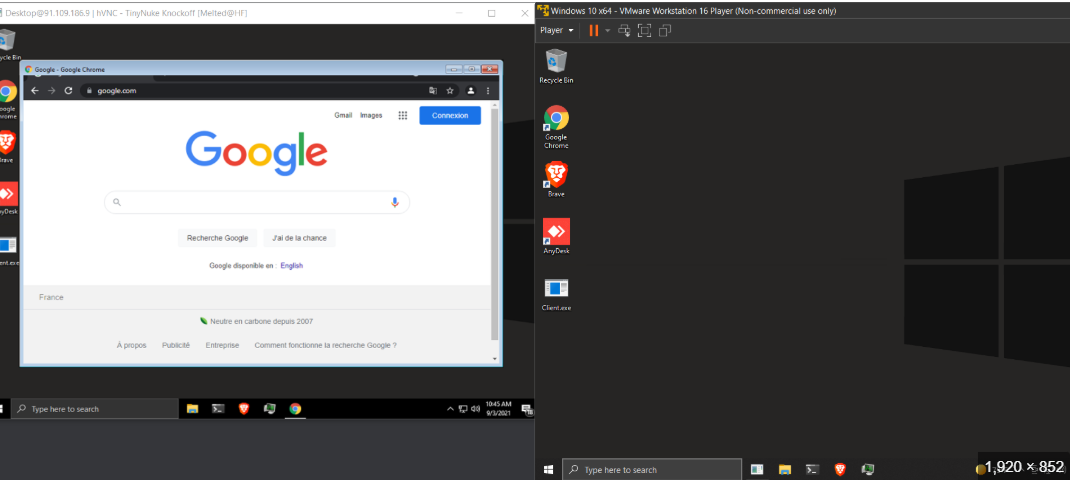
HVNC Tinynuke 2024
In the evolving landscape of cyber threats, remote access tools—both legitimate and malicious—play a significant role in modern attacks. One such tool, often referred to in cybersecurity circles, is the “HVNC Tinynuke 2024,” a sophisticated piece of malware designed to provide attackers with stealthy, persistent control over compromised systems. Unlike traditional Remote Access Trojans (RATS), […]
Alien Android Banking Botnet 2025 Cracked
The mobile banking threat landscape has reached alarming sophistication with Alien Android Banking Botnet 2025 Cracked, a powerful malware suite that combines banking trojan capabilities with botnet functionality. This advanced threat demonstrates how cybercriminals are weaponizing cracked versions of commercial malware to create large-scale attack networks. Alien Android Banking Botnet 2025 Cracked has been implicated […]