Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
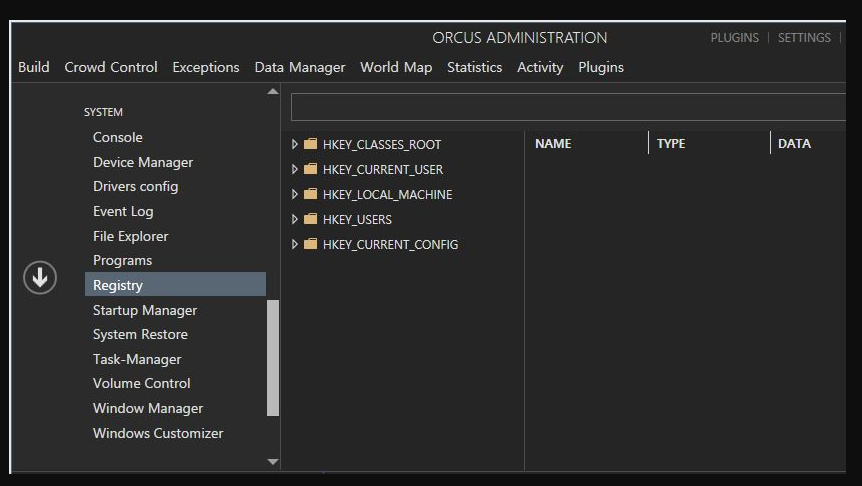
Orcus RAT 1.9.1 + 13 Plugins Cracked
Orcus RAT 1.9.1 with 13 cracked plugins represents one of the most sophisticated remote administration tools available in underground markets. Originally developed as commercial software, its cracked version has been weaponized by threat actors, offering an alarming array of surveillance and system control capabilities. This analysis explores its functionality, risks, and defensive measures to help […]
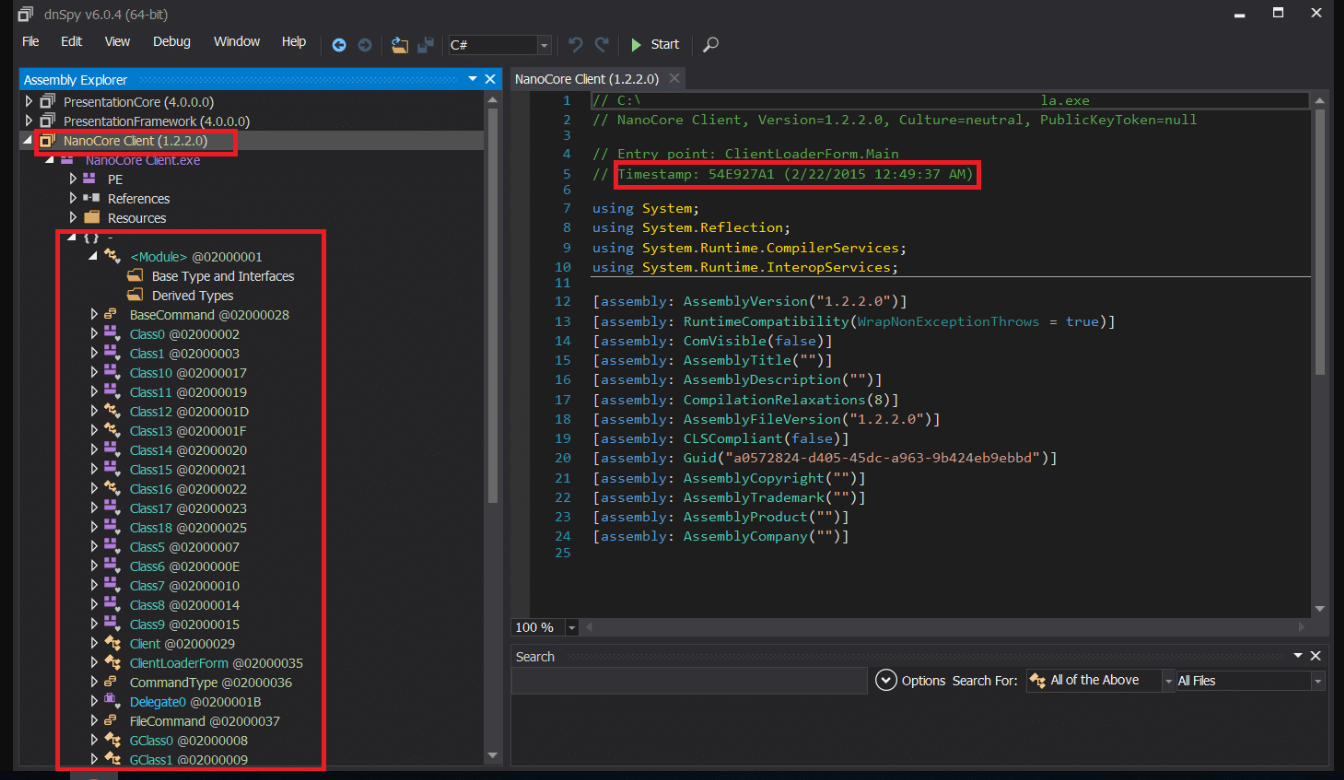
NANOCORE RAT 1.2.2.0 with all plugins CRACKED
NanoCore RAT 1.2.2.0 with all plugins cracked represents one of the most advanced and dangerous Remote Access Trojans (RATs) circulating in underground hacking communities. Originally sold as commercial surveillance software, its cracked version has been widely distributed, enabling malicious actors to gain complete control over infected systems. This analysis explores its capabilities, risks, and defense strategies to help cybersecurity […]
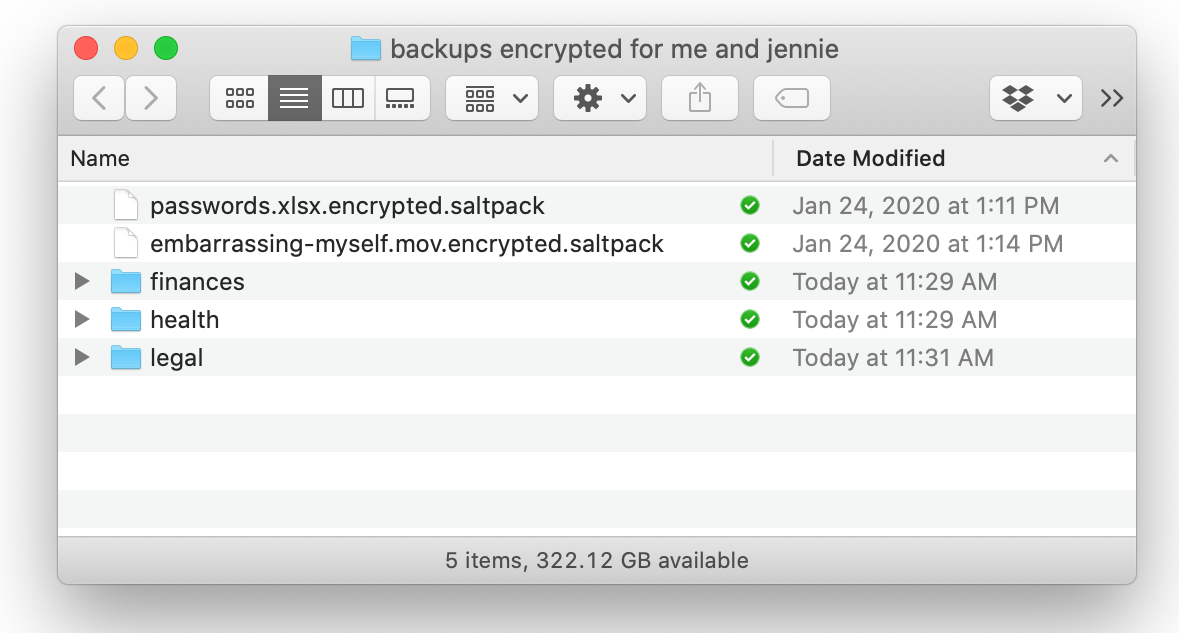
KeyBase v1.5 Beta
KeyBase v1.5 Beta represents a cutting-edge advancement in encrypted communication and identity verification, offering users a secure platform for messaging, file sharing, and cryptocurrency transactions. Designed with privacy-first principles, this beta release introduces enhanced security features while maintaining user-friendly accessibility. As digital privacy concerns grow, understanding KeyBase’s capabilities helps both security professionals and everyday users protect their […]
Anubis Android Banking Botnet v.2.5 with Tutorial
Anubis is a sophisticated Android banking malware that has evolved into a powerful botnet, capable of stealing sensitive financial data, logging keystrokes, and remotely controlling infected devices. Initially discovered in 2017, Anubis v2.5 represents an advanced iteration with enhanced evasion techniques and expanded attack vectors. This article explores its functionality, features, and operational mechanics for educational […]
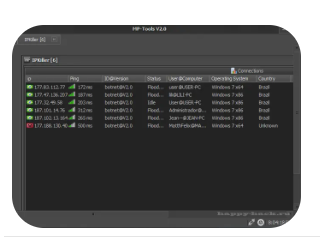
IP Killer 2
IP Killer 2 is a powerful network stress-testing tool designed to simulate high-intensity traffic floods, primarily used for penetration testing, cybersecurity research, and network hardening. While it can be misused for disruptive purposes, ethical hackers and security professionals utilize it to assess network resilience against DDoS (Distributed Denial of Service) attacks. This article explores its functionalities, legitimate applications, and […]
Booters Pack Collection 2024
The Booters Pack Collection 2024 is a compilation of powerful network stress-testing tools designed for cybersecurity professionals, penetration testers, and ethical hackers. These tools simulate DDoS (Distributed Denial of Service) attacks, allowing experts to assess network vulnerabilities, test mitigation strategies, and improve defensive measures. While they can be misused, this article focuses on their legitimate applications in security research and […]
ARES RAT v1.2.1 Cracked
ARES RAT (Remote Access Trojan) is a powerful surveillance and control malware used for remote system administration—often exploited for unauthorized access. The cracked v1.2.1 version circulates in underground forums, allowing hackers to bypass licensing restrictions. While originally marketed as a legitimate remote tool, its misuse poses severe cybersecurity threats, making it essential for security professionals to understand […]
DaRKDDoSeR 5.6c Cracked
DaRKDDoSeR 5.6c Cracked is a modified version of a network stress-testing tool that simulates DDoS (Distributed Denial of Service) attacks. While the original software was designed for legitimate penetration testing, cracked versions often circulate in underground forums, posing significant risks. This article examines its technical aspects, ethical concerns, and defensive applications for cybersecurity professionals. Download Link 1 Download Link 2 […]
Top Powerfull DDOs attack tools 2024
Distributed Denial-of-Service (DDoS) attacks remain one of the most disruptive threats to online services, overwhelming networks with malicious traffic. While ethical hackers and cybersecurity professionals use these tools for stress testing and defense simulations, malicious hackers exploit them to take down websites and services. This article explores the most powerful DDoS tools in 2024, their […]
Orion Keylogger 2.1 Cracked
Orion Keylogger 2.1 Cracked is an illicitly modified version of the original Orion Keylogger, a stealthy surveillance tool designed to record keystrokes, capture screenshots, and steal sensitive data. While the legitimate version may be used for parental control or employee monitoring, the cracked variant is often distributed through malware forums and phishing scams, posing severe risks to cybersecurity and […]