Malware
Here are various types of malware you can download. Virus, Worm, Trojan, Ransomware, Spyware, Adware, Keylogger, Rootkit and Botnet Malware.
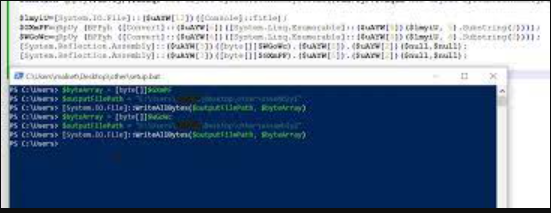
Crypto Stealer 2025 Cracked
The cryptocurrency ecosystem faces growing threats from increasingly sophisticated malware, with Crypto Stealer 2025 Cracked emerging as one of the most dangerous tools for digital asset theft. This advanced malware variant demonstrates how cybercriminals are leveraging cracked versions of commercial stealers to create powerful, low-cost attack tools. Crypto Stealer 2025 Cracked has been actively used […]
Quasar RAT v1.3 Cracked
Cyber threats continue to evolve, with remote access trojans (RATs) playing a significant role in modern attacks. One such tool, a cracked version of a well-known RAT, has spread widely across underground forums, enabling malicious actors to gain unauthorized access to systems. Quasar RAT v1.3 Cracked empowers attackers to conduct espionage, steal data, and deliver […]
Pack of NYAN CAT’s 2024
The “Pack of NYAN CAT’s 2024” has emerged as a significant threat in modern cyberattacks, particularly due to its modular design and ability to evade traditional security measures. This toolkit is often distributed through phishing campaigns, exploit kits, or malicious downloads, enabling attackers to deploy a range of payloads, from ransomware to remote access trojans […]
RAT Pack 2025 Cracked
The cybersecurity landscape faces an escalating threat from modular malware frameworks, with Rat Pack emerging as a particularly dangerous example of adaptable attack tools. This sophisticated suite of malicious components has become increasingly prevalent in modern cyberattacks due to its ability to combine multiple infection vectors into coordinated campaigns. Rat Pack exemplifies the growing trend […]
njRAT v0.7d Edition by Hidden Person
The cyber threat landscape continues to evolve with increasingly sophisticated remote access tools, among which njRAT v0.7d Edition has emerged as a particularly dangerous variant of a well-known remote administration tool. This enhanced version demonstrates how cybercriminals are refining existing malware with new capabilities to bypass modern security measures. njRAT v0.7d Edition by Hidden Person […]
Teardroid v4
In the evolving landscape of cyber threats, remote access trojans (RATs) continue to be a persistent tool for attackers, allowing unauthorized control over compromised systems. Among these, Teardroid v4 has emerged as a notable Android-based malware, frequently employed in targeted attacks to steal sensitive data, monitor user activity, and deliver additional payloads. Its modular design and […]
Lost Door Aws 9.2
In the evolving landscape of cloud-based cyberattacks, sophisticated tools targeting AWS (Amazon Web Services) environments have become increasingly prevalent. Lost Door Aws 9.2 specialized utilities enable threat actors to exploit misconfigured cloud resources, escalate privileges, and establish persistent access to critical infrastructure. As organizations continue migrating operations to the cloud, attackers have adapted by developing […]
Subbus RAT 2025 Cracked
The cybersecurity landscape faces an escalating threat from next-generation remote access Trojans, with Subbus RAT 2025 emerging as a particularly sophisticated example of modern malware evolution. This advanced threat demonstrates how cybercriminals are leveraging cutting-edge techniques to create more resilient and feature-rich attack tools. SUBBUS RAT has been observed in high-profile attacks against financial institutions […]
PENTAGON RAT 2024
The “PENTAGON RAT 2024” is a highly advanced remote access trojan (RAT) that poses a major threat in modern cyberattacks. Unlike traditional malware, it not only evades detection but also maintains persistent access to compromised systems. Security experts have linked it to espionage, data theft, and credential harvesting. Itsmodular architecture allows attackers to deploy additional malicious payloads. As a result, it has become a versatile tool for both cybercriminals and state-sponsored […]
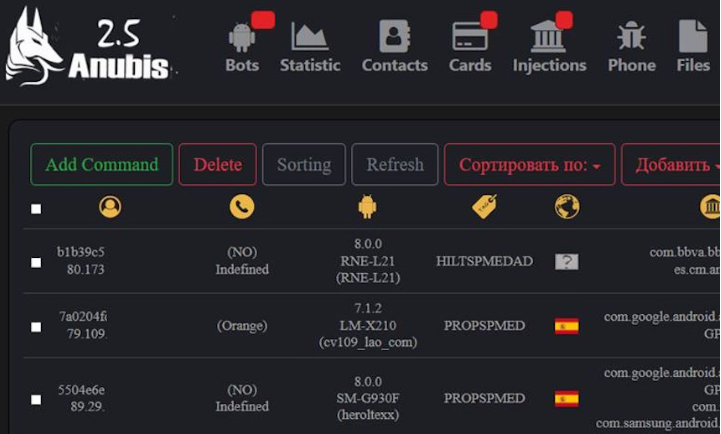
ANUBIS 7.0 ANDROID BOTNET (Panel + Builder+ Tutorial)
The rise of mobile-focused malware has introduced dangerous new threats to personal and enterprise security, with advanced botnet frameworks posing one of the most severe risks. Modern Android botnet kits now offer sophisticated infection vectors, evasion techniques, and monetization capabilities that rival traditional Windows malware. ANUBIS 7.0 ANDROID BOTNET toolkits typically include builder applications, command-and-control […]